Companies aren’t in the habit of keeping servers that they don’t need online. But there are certain types of servers that rise to a different level of importance.
We call these servers critical servers. A critical server is a computer system that runs a function which is vital to the sustained survival of a business.
Examples of common types of critical servers include ERP systems, Electronic Medical Record systems or authentication and authorization systems.
Every company has their own definition of what represents a critical server, but identifying one is simple: they’re the systems where if they go offline, the company will experience an outsized negative financial or operational impact.
In order to understand the resilience requirements of critical servers, we must address their specific operational requirements. In this post, we’ll break down how to think about backing up and restoring critical servers for your business.
How immutable backups protect critical systems
Because critical servers are so important to your business, it’s non-negotiable that they leverage immutable backups.
An immutable backup is one that cannot be edited in any way once it has been saved.
That means that every byte of your critical system is frozen in time at the point of the backup, ensuring that if you need to restore from that backup point, you will return to the known-good operation of that system.
Ideally, you never want to use a server backup in anger. But in reality, applying a backup to a server often happens during the most stressful moments for your organization. That goes double for critical servers.
The last thing that you want to worry about is whether any of the data in your backup is corrupt. With an immutable backup, that’s a worry you never need to consider, because the data in the backup cannot change.
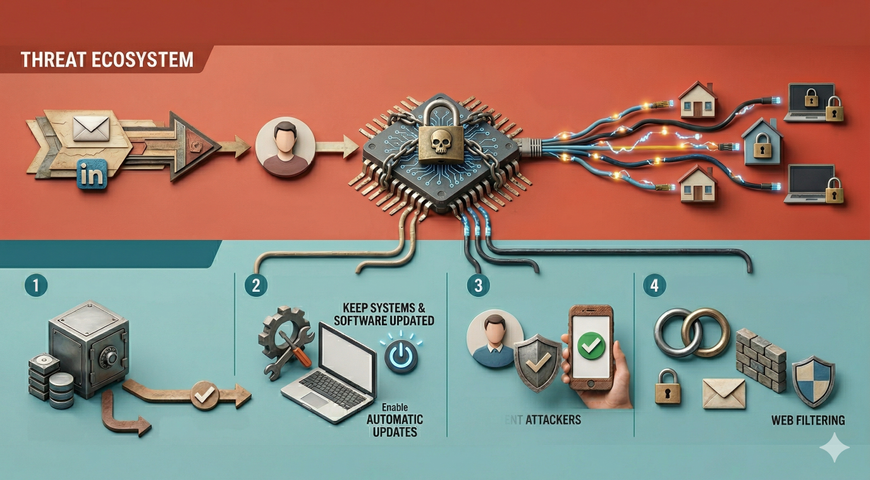
Sophisticated attackers today recognize the value of backups just as much as the servers themselves. If someone wants to hold your data for ransom, they know that there’s no value if you can simply restore things with no headaches.
So ransomware intentionally attacks your backups just the same as your existing servers. Immutable backups prevent this by preventing any modification of your backup data at all
Practical steps to improving critical server resilience
If you’re looking to reinforce your critical server resilience, we have a clear-cut step-by-step plan for doing that. Let’s walk through each of the steps.
1. Identify mission-critical workloads
Critical servers need additional attention due to their high importance. But before you can give them that extra attention, you have to first identify them.
In order to do that, you need to first outline your mission-critical workloads as a company and then the resources that service those workloads.
2. Map business impact
Once you identify your mission-critical workloads, the next step is to understand the business impact of losing those services.
According to ITIC, over 90% of mid-sized and large enterprises report that a single hour of downtime costs $300,000 or more, with 44% seeing costs exceed $1 million per hour.
When you can quantify the cost of losing a particular service, it’s trivial to then budget for outage prevention costs.
3. Implement immutable backup
Now that you know where your most critical systems are and how much it costs you when they go down, you’ve developed a budget for disaster prevention on those systems. Expending that budget to support immutable backups is the next step.
4. Validate backup integrity
Once you are collecting backups, you need to validate that those backups are sound. An untested backup is one that has the potential to fail at the most important time. But many companies don’t ever test their backups because doing so is a costly time commitment.
5. Test clean restore
The first way that you want to test your restoration is to restore to a clean server. In an emergency scenario, you want to restore as quickly as possible. In many situations, the simplest way to do that is to restore to a completely clean server.
Modern cloud solutions support this workflow explicitly, meaning that it’s simple and straightforward for teams to plan for this recovery scenario.
6. Create DR runbooks
Now that you know that your backups will restore a working server from the drop, you can outline a recovery plan when disaster strikes.
One key consideration for disaster recovery documents is that you need to make sure that they are kept up to date. Just like a broken backup, a DR document which references servers that aren’t used anymore doesn’t do you any good in a moment of crisis.
7. Simulate failover/fallback
Finally, to ensure that your backups and disaster recovery plans are suitable, you should run full simulated failure and recovery processes.
Doing that gives you confidence that, when things break for real, you’ll be prepared to get the business back to operating normally as quickly as possible.
Why critical servers matter (business & operational impact)
Critical servers are critical because they either represent an outsized financial impact for the company or because they support legally-required business functionality. Sometimes, they do both.
Attackers understand this, so they target a business’s most critical servers during attacks like ransomware attacks.
Aberdeen estimates that the cost of outages for businesses worldwide is a staggering $1.4 trillion per year. As we noted earlier, the business going down costs from $300K-$1 million per hour. The risks of outages on a critical server are much higher than more mundane IT services.
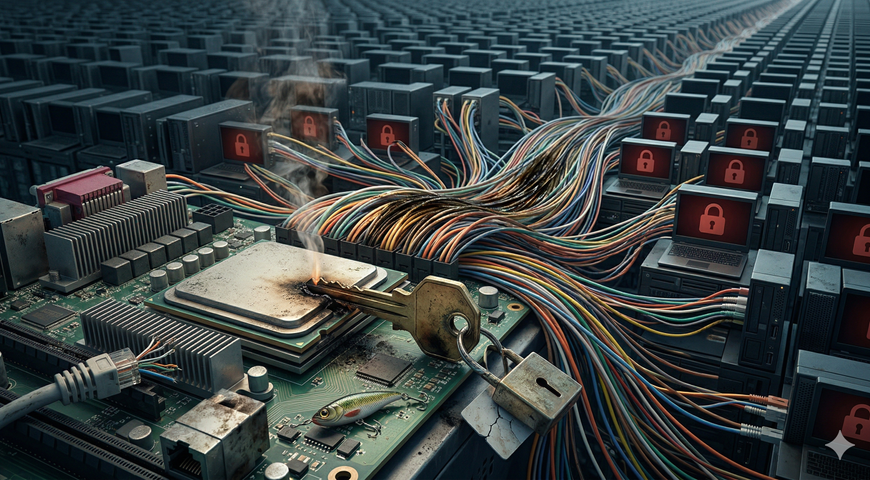
Why traditional backups fail for critical servers
Traditional server backups use a snapshot approach, which does have some benefits. However, snapshots aren’t the same thing as full backups. Snapshots save incremental differences between points in time.
This makes full recovery more difficult, because they don’t allow for a blank-slate restoration of a system. Instead, you must restore the server step by step.
That means that if there are any corruption issues with a snapshot, you can’t recover the server from a snapshot more recent than that.
Given the paramount importance of critical servers, losing out on financially- or legally-critical data on your server due to an incremental backup issue is unacceptable.
Clean recovery vs fast recovery (introducing MTCR)
Mean time to clean recovery (MTCR) is an emerging industry-wide KPI that recognizes the specific threats posed by ransomware attacks.
Sophisticated attackers will attack your backups, as we’ve already noted. If your incremental backup is corrupted by malware, it doesn’t do you any good.
So instead, clean recovery focuses on rebuilding the entire service from scratch, with a known-good immutable backup. While this has the potential to be slower than restoring from an incremental backup, it eliminates risk by taking a “clean room” approach.
A brand new server with no exposure to the outside world is much safer during the middle of an ongoing attack. For your most critical server, getting this right is better than doing it quickly—especially because if you get it wrong, you’re going to have to do it again.
Persona-specific view: why this matters
Whatever hat you wear, there’s a good reason for you to support immutable backups for your critical servers.
- CIO: Immutable backups support uptime and continuity for your most critical systems.
- CISO: Immutable backups improve MTCR and reduce your risk exposure.
- CFO: The financial risk due to downtime and ransomware is mitigated by ensuring clean recovery.
- IT Operations: Clean recovery means that when things go wrong, the pressure is lower.
Across the business, the benefits of immutable backups and a shorter MTCR are clear: they provide a high-quality return on investment.
A well-defined disaster recovery plan that you test and verify regularly means that you can operate with confidence that your most critical servers aren’t at elevated risk. And your company isn’t at elevated risk, as a result.
Acronis integration & conclusion
Platforms like Acronis support immutable backups, promoting the industry best-practice 3-2-1 backup approach. In today’s cloud-based world, a clean-restore backup approach is simple and straightforward, allowing companies to minimize their mean time to clean recovery.
Critical servers have an outsized impact on the operation of your business. Any time that they’re out of operation is crushing to business outcomes. Wise companies recognize the need for engineered resilience, versus simply hoping for the best with their backups.
They choose immutable backups, regularly test their restoration process, maintain high-quality disaster recovery plans, and keep clean lines of communication in the event that disaster strikes.
Companies like Acronis work alongside them every step of the way, providing the kind of assistance that keeps things flowing smoothly, no matter the size of your business.
If you’re interested in engineering resilience for your critical servers, there’s no time like the present. Reach out to Acronis and see how they can help today.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 60+ countries. Acronis Cyber Platform is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.