AI-enabled systems are becoming more common in operational technology (OT) environments. What many industry analysts call “Physical AI” refers to AI systems embedded in physical environments — such as industrial cameras, robots and edge systems — that can perceive, interpret and act on real-world conditions. In industrial settings, this includes machine vision systems, predictive maintenance models, robotics optimization and edge analytics operating close to production assets.
Unlike enterprise IT AI, Physical AI operates within production environments. It processes operational data and supports monitoring, decision making and, in some cases, automated actions that directly affect uptime, quality, safety validation and energy efficiency. As these capabilities become more embedded in operational layers, they are reshaping automation, manufacturing, and critical infrastructure.
Recent developments show how real this shift has become. Siemens and NVIDIA expanded their partnership at CES 2026 around an Industrial AI Operating System intended to bring AI deeper into engineering, manufacturing, production and operations. ABB has been advancing AI-based robotic vision through its LandingAI collaboration. Honeywell executives have also described “Physical AI” as gaining traction in operations technology. While these examples differ in application, they point in the same direction: More industrial intelligence is being introduced into operational layers.
Physical AI is moving from concept to operations
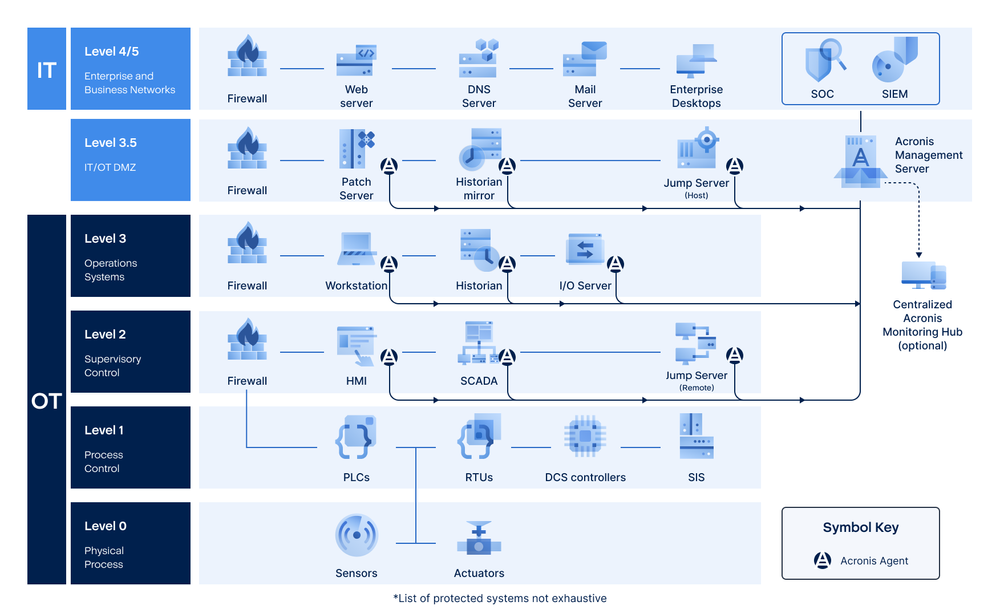
Physical AI expands primarily across Levels 2 and 3 of the Purdue Model. Disruption at these tiers may not even stop the physical process immediately, but it can compromise visibility, validation and coordination, extending downtime and increasing operational uncertainty. This can halt quality validation, delay production release and force manual fallback procedures because these layers depend heavily on software integrity and configuration consistency.
For instance, if we look closer at Level 3, AI can be integrated into MES platforms, production scheduling systems, digital twins and advanced analytics servers, which increasingly connect to enterprise IT and cloud platforms. At Level 2, AI appears in advanced HMIs, machine vision stations and supervisory workstations that provide operators with augmented insight.

This evolution introduces a specific challenge: a new Level 2 workstation running AI-based inspection often introduces a general-purpose operating system, additional services and drivers, new integration paths to historians or MES systems and credentials that may be used across zones. Each of these elements must be managed under existing zone-and-conduit architecture. If segmentation, access control and system hardening are not maintained, it increases exposure — not because of the AI itself, but because of the increased software dependency.
The security risk: Loss of validated state
Since software-driven systems at Levels 2 and 3 increasingly rely on Windows or Linux, inter-zone connectivity, APIs and edge compute, the architecture of industrial environments becomes more exposed to threats that were historically concentrated in enterprise IT environments. This is why public guidance on AI in OT has become more direct. In December 2025, CISA, NSA and partner agencies published guidance on securely integrating AI into OT, warning that while AI can improve productivity and efficiency, it also introduces new safety, security and reliability risks if integration is not handled carefully.
To consider a practical example: a Level 2 quality inspection station uses AI-based image recognition running on a Windows workstation connected to a historian at Level 3. If the inspection workstation becomes encrypted by ransomware introduced through a compromised engineering laptop, the PLC continues operating the line. However:
- Quality validation cannot be confirmed.
- Operators cannot release finished product.
- Manual inspection must begin.
- Throughput drops.
- Compliance documentation is disrupted.
In this scenario, the operational impact is not just “cyber downtime”; it’s the loss of validated state. Restoring that workstation manually may require reinstalling the OS, reconfiguring inspection software and reconnecting to upstream systems.
Resilience through predictable recovery
If a validated system image exists, restoration becomes predictable rather than improvised. An image-based backup allows a system to return to its last validated state and reduces mean time to stable operations, preserving:
- OEM-certified software versions.
- Driver compatibility.
- Network configuration.
- Application dependencies.
Furthermore, in air-gapped environments, local recovery is essential, and in segmented networks, recovery must not depend on cloud access. As digitalization increases software dependency and compliance requirements such as IEC 62443, NIS 2, and EU CRA become stricter, predictable recovery becomes part of operational engineering discipline. Reliable backup and predictable recovery are essential OT controls: They help restore validated system states quickly, reduce downtime and let digitalization move forward without turning software failure into a production crisis.
Supporting modern and legacy environments
Manufacturing environments rely heavily on Windows-based HMIs, engineering workstations, SCADA nodes, historians and edge systems for visibility and coordination. These systems often sit on legacy operating systems, run in segmented networks or operate in air-gapped plants where centralized IT access is limited by design. When they fail, rebuilding them manually is slow, error prone and disruptive.
In both legacy and modern manufacturing environments, reliable recovery supports several critical objectives:
- Restoring Windows- and Linux-based OT systems to certified, known-good states.
- Preserving validated OEM configurations and software dependencies.
- Supporting air-gapped, partially connected or hybrid plant environments where centralized IT access may be limited.
- Allowing local recovery workflows without waiting for external specialists.
- Reducing downtime duration by avoiding manual rebuilds and configuration drift.
If a Level 2 PC or historian fails after a software issue, a validated image can bring the system back to its previous state instead of forcing a full manual rebuild. This reduces the risk of configuration drift, which becomes more important as AI-enabled systems add more dependencies to the operational stack.
Industry deployments and what this means for OT resilience
Automation vendors and large industrial enterprises are embedding more analytics and software capability into their platforms. That increases operational value but also increases lifecycle management responsibility. Acronis Cyber Protect for OT is deployed in environments that include major automation vendors and Global 2000 manufacturers such as Honeywell, ABB, Rockwell Automation, Yokogawa, Tata Steel and Toyota.
In these environments, backup and recovery are implemented to preserve validated system states, support legacy operating systems that remain required in production and enable restoration within segmented or air-gapped networks. Digital transformation in OT is accelerating; resilience must scale with it.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 60+ countries. Acronis Cyber Platform is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.