Author: Alexander Ivanyuk — Senior Director, Technology
Incident of the month
In February 2026, Google’s Threat Intelligence Group (GTIG), their cybersecurity firm Mandiant and partners disclosed the disruption of a global cyber-espionage campaign attributed to a suspected China-linked actor tracked as UNC2814, targeting telecommunications providers and government networks. The activity was assessed as ongoing since at least 2023, impacting 53 organizations in 42 countries, with suspected infections in at least 20 more.
A key capability in the operation was a newly observed C-based backdoor, GRIDTIDE, which abused the Google Sheets API for command and control (C2). By authenticating through a Google service account and using spreadsheet cells as a tasking and data channel, the malware could blend attacker traffic into legitimate SaaS activity while supporting system reconnaissance and remote command execution, as well as file upload / download.
The response effort included terminating attacker-controlled Google Cloud projects, revoking Google Sheets API access, and sinkholing domains, while directly notifying affected organizations and providing cleanup support. The incident underscores a persistent trend in state-aligned intrusion sets: Shifting C2 and operator workflows into trusted cloud services to reduce detection and complicate network-based monitoring.
February malware threat detections
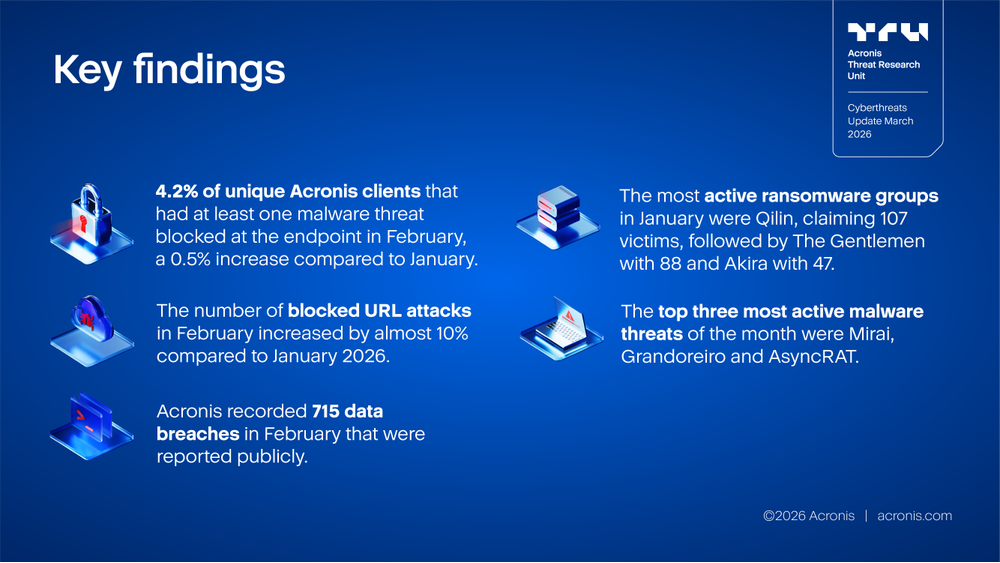
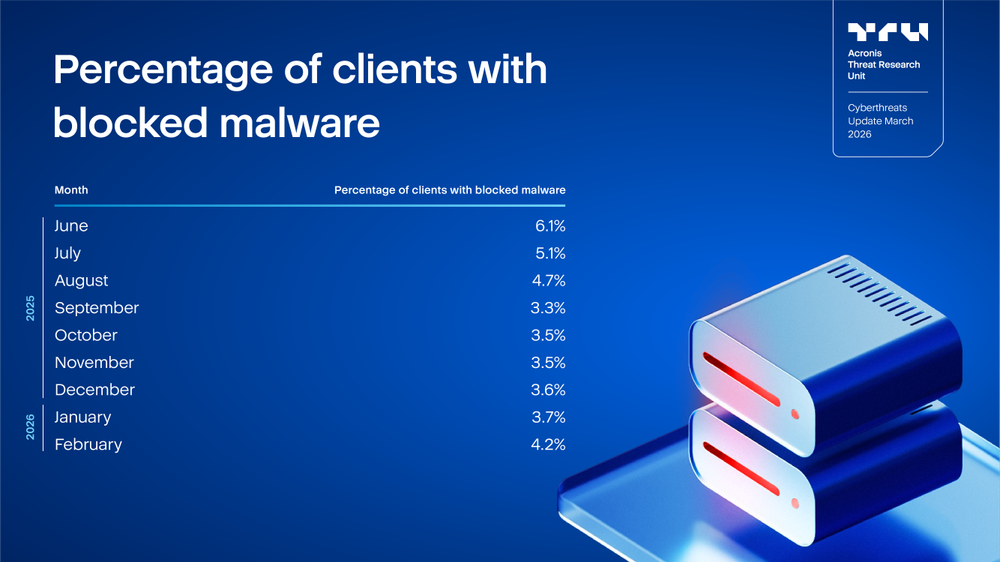
The table below show the percentage of unique Acronis clients that had at least one malware threat blocked at the endpoint. In February 2026, the percentage increased slightly to 4.2%, representing a month-over-month rise of 0.5 percentage points compared to January 2026.
When compared to mid-2025 levels, February 2026 remained lower, with malware exposure affecting roughly 30% fewer clients than in June 2025.

In February, the top three countries most frequently attacked or demonstrating poor cyber hygiene remained unchanged: Palestine recorded the highest malware detection rate globally, with 52.5% of unique users experiencing at least one malware detection, indicating an exceptionally high level of threat exposure. Sri Lanka (19.7%) and Bangladesh (13.7%) followed at a considerable distance, highlighting a sharp drop-off after the top-ranked country and a highly uneven geographic distribution of malware activity.
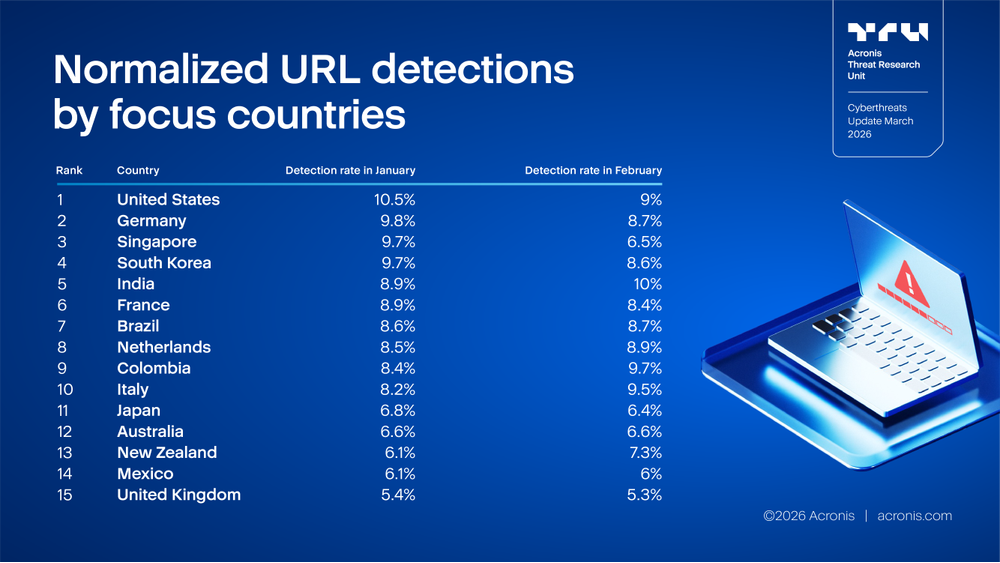
Across most countries, February 2026 showed a broad decline or stabilization versus January. The biggest drops were in Singapore (9.7% to 6.5%, ~33% lower), Canada (12.3% to 9.3%, ~24% lower), and the United States (10.5% to 9.0%, ~14% lower), with additional modest decreases in Germany, South Korea, France, Japan, Mexico and the U.K. Brazil was essentially flat (8.6% to 8.7%) and Australia was unchanged (6.6% to 6.6%), suggesting either steady exposure levels or consistent detection coverage month to month.
At the same time, several markets moved materially upward in February, indicating localized pressure increases rather than a uniform global improvement. The most notable rises were in Italy (8.2% to 9.5%, ~16% higher), Colombia (8.4% to 9.7%, ~15% higher), New Zealand (6.1% to 7.3%, ~20% higher), and India (8.9% to 10%, ~12% higher). Netherlands also edged up (8.5% to 8.9%). Generally speaking, the pattern looks like risk is “shifting” geographically: Overall rates have eased in several large markets, while a handful of countries saw clear upticks. It’s worth validating whether this reflects true threat activity changes, campaign targeting or telemetry / detection coverage differences in those regions.
Protection
The threats can be detected and mitigated with solutions from Acronis.
Acronis Cyber Protect Cloud protects against both known and never-before-seen threats through a multilayered protection approach. This includes behavior-based detection, AI- and ML-trained detections and anti-ransomware heuristics, which can detect and block encryption attempts and roll back any tampered files automatically without any user interaction.
Additional email security and URL filtering can help you protect against social engineering threats. And, your Acronis #CyberFit Score helps you quickly identify systems that need attention, while integrated patch management makes updating your software to the latest versions simple.
Acronis XDR for Acronis Cyber Protect Cloud brings the visibility needed to understand attacks while simplifying the context for administrators and enabling efficient remediation of any threats.






