Summary
- The Acronis TRU team identified a threat cluster leveraging a customized Adwind (Java RAT) variant with polymorphic characteristics to deliver a ransomware module, tracked as ‘JanaWare.’
- Analysis of malware samples, infrastructure and telemetry indicates the campaign is likely focused on Turkish users. The malware enforces execution constraints based on system locale and external IP geolocation, which likely restricts activity to systems located in Turkey.
- Observed samples and telemetry suggest the activity has been ongoing since at least 2020. A sample compiled in November 2025 indicates that associated command-and-control infrastructure remains active. Obfuscation, polymorphism and geographic restrictions have likely contributed to limited visibility.
- Victimology appears to primarily include home users and small to medium-sized businesses. Initial access is assessed to occur via phishing emails delivering malicious Java archives. Ransom demands observed in analyzed samples range from $200–$400, consistent with a low-value, high-volume monetization approach.
- This combination of consumer- and SMB-focused victimology, low ransom demands and opportunistic targeting suggests the operation is distinct from enterprise-focused ransomware campaigns, which typically prioritize high-value targets and larger payouts.
Introduction
The investigation began with the analysis of a customized Adwind RAT variant suspected to be associated with ransomware activity. After collecting several JAR archive samples from VirusTotal, we discovered that one of them behaved differently during testing. When executed in our analysis environment, the sample dropped the following ransom note on the test machine:
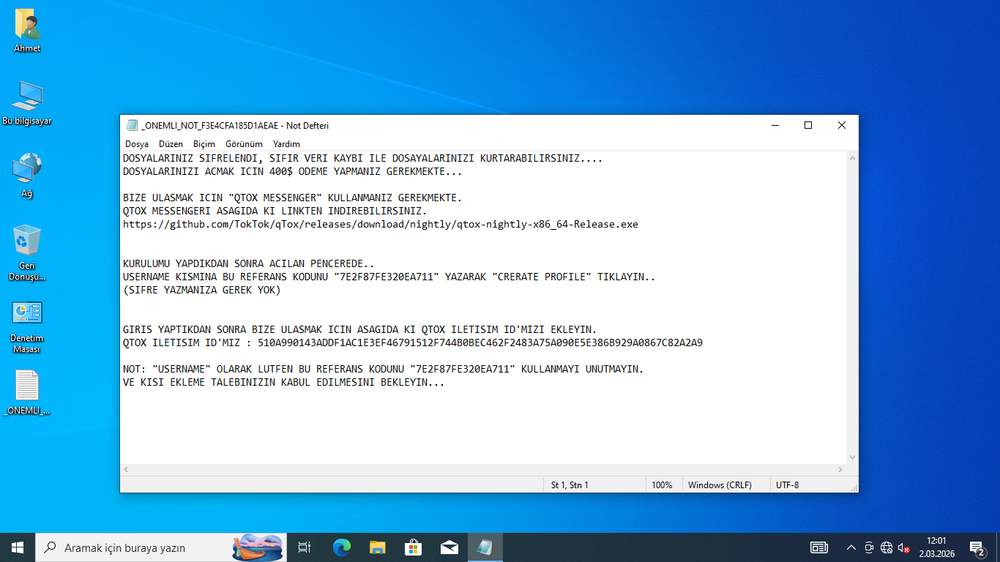
The ransom note was written in Turkish. Its translated content is shown below:
The attackers encourage victims to establish contact through a secure and private channel, such as qTox — a free, open-source desktop messaging application that operates over the Tox peer-to-peer network. qTox is a decentralized chat client with no central servers, that provides end-to-end encryption and is designed to protect user privacy and anonymity. In some campaigns, however, instead of using qTox, victims were instructed to download the Tor Browser and visit a dedicated .onion site to communicate with the attackers.
Attack chain
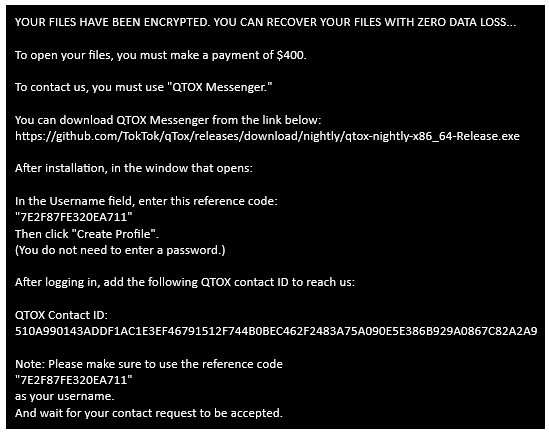
Through telemetry hunting, we reconstructed the infection sequence using EDR data, revealing how the ransomware is delivered and executed within the victim environment. The analysis indicates that the campaign relies on email-based phishing to initiate the attack, leading users to download a malicious payload that ultimately results in ransomware execution. The overall infection flow is illustrated below:
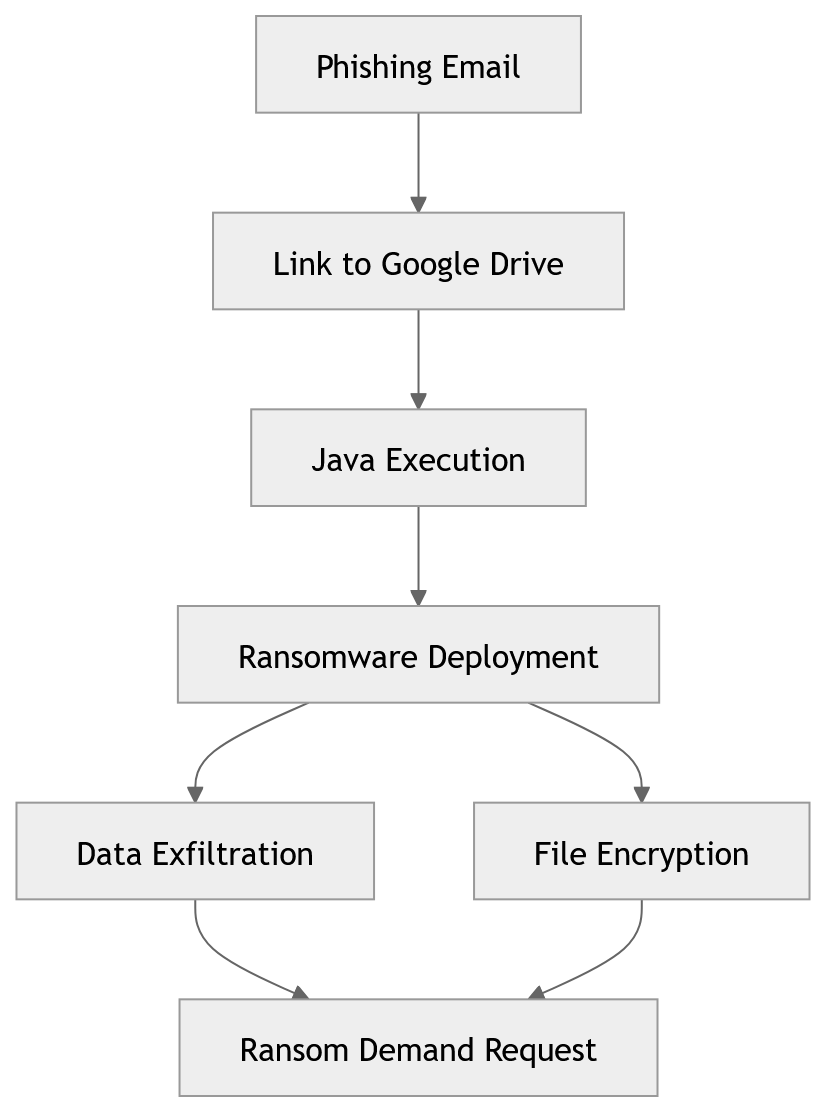
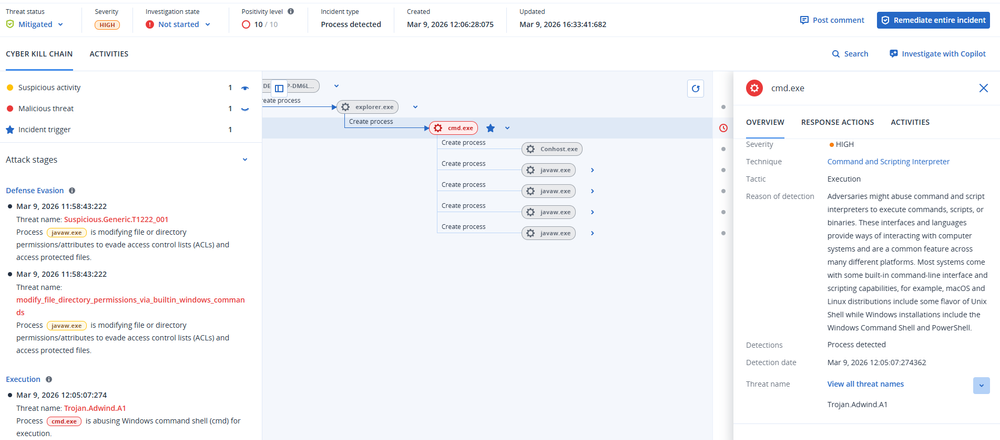
The reconstructed attack chain is supported by EDR telemetry, which captures the process execution flow on compromised systems:
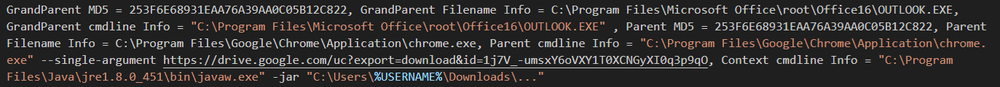
Analysis of telemetry data indicates that the victim accessed an email through Outlook, which triggered the launch of a Chrome process to open a Google Drive link. This resulted in the download and subsequent execution of a malicious JAR file via javaw.exe:
- Grandparent Process: OUTLOOK.EXE (MD5: 253F6E68931EAA76A39AA0C05B12C822) located at C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE
- Parent Process: chrome.exe (MD5: 253F6E68931EAA76A39AA0C05B12C822) located at C:\Program Files\Google\Chrome\Application\chrome.exe with the command line: "C:\Program Files\Google\Chrome\Application\chrome.exe" --single-argument hxxps://drive.google[.]com/uc?export=download&id=1j7V_-umsxY6oVXY1T0XCNGyXI0q3p9qO
- Ransomware Execution: javaw.exe executing the JAR archive: "C:\Program Files\Java\jre1.8.0_451\bin\javaw.exe" -jar "C:\Users\%USERNAME%\Downloads\...."
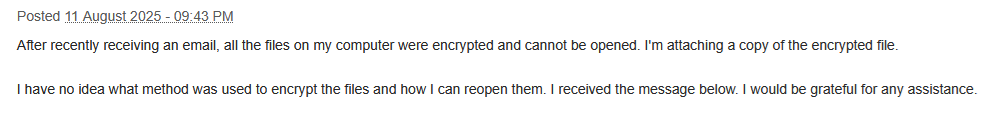
This activity is clearly part of a phishing campaign, where users are tricked into clicking a link in a deceptive email, ultimately downloading and running the ransomware. This distribution method is further corroborated by victim reports on public forums (such as www.bleepingcomputer.com), where users describe similar infection scenarios:
Technical details
Obfuscation
Although Java bytecode is relatively easy to decompile, this becomes significantly more difficult when obfuscation is applied. The malware authors employ multiple obfuscation and protection techniques, including custom class loaders. During our analysis, we identified two publicly available obfuscators in use: Stringer and Allatori. The open-source project java-deobfuscator provides tooling that can assist in reversing protections implemented by both of these obfuscators.
Polymorphism
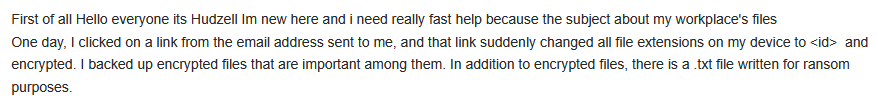
Furthermore, the malware contains a class named FilePumper, whose purpose is to perform self-modification. Instead of simply copying itself to the target system during installation, the malware adds random content to its JAR archive, inflating the file size by tens of megabytes. As a result, each deployed instance becomes unique, producing a different file hash (e.g., MD5) on every infected machine. In the screenshot below, we can observe the randomly added classes within the JAR archive, compared to the original version.
This technique effectively hinders straightforward hash-based detection and signature matching.
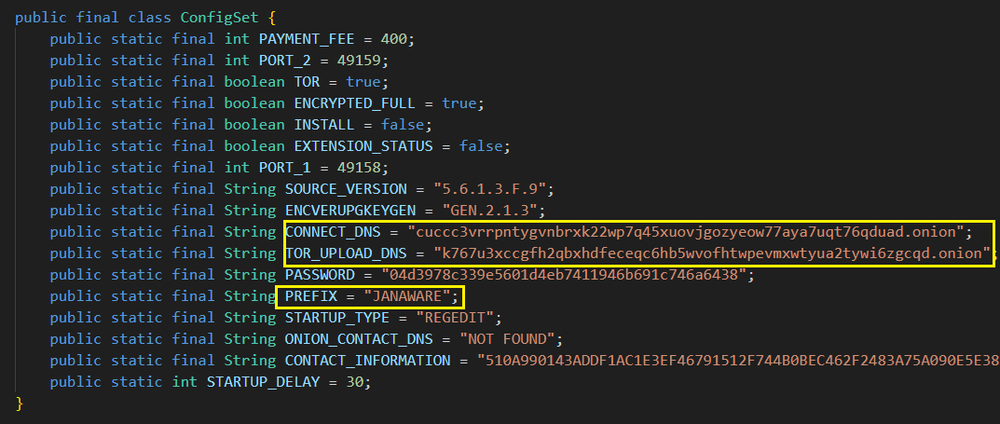
Configuration
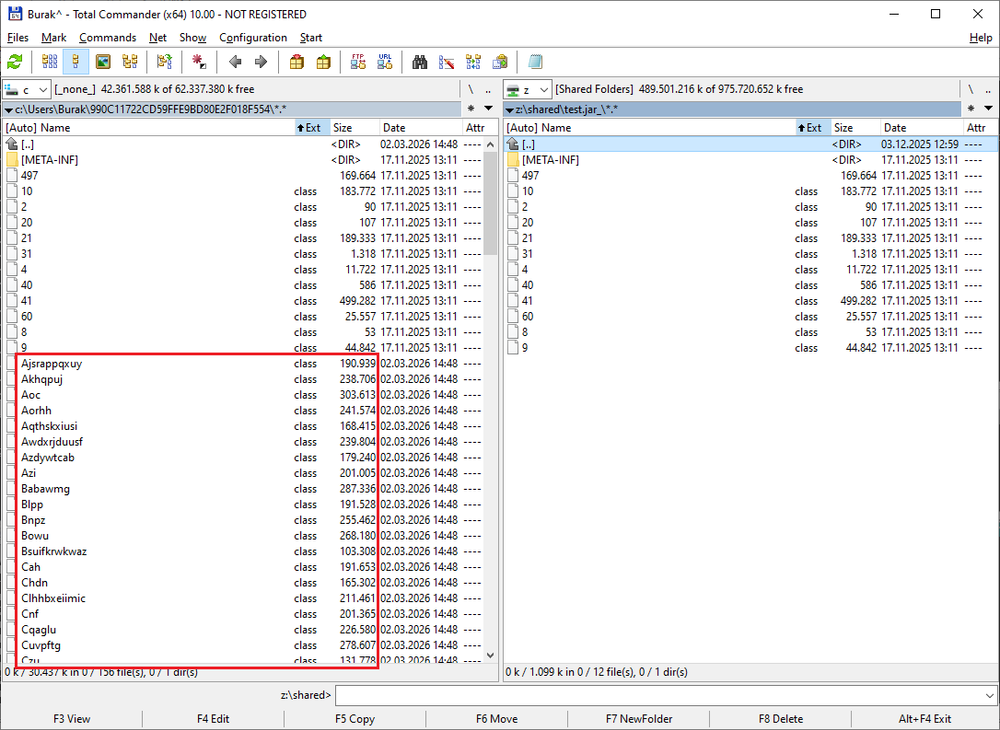
At the beginning of its initialization process, the malware loads a set of hard-coded configuration parameters embedded in a Java class. These parameters define key aspects of its runtime behavior and communication.
The configuration specifies the command-and-control (C2) infrastructure, including a domain and two TCP ports, which the malware uses to establish and maintain its control channel. It also includes references to TOR-related paths and components, indicating that the malware can route over the TOR network. In this context, TOR is not related to payment mechanisms, but rather to network obfuscation and potential anonymized communications or data exfiltration.
The configuration also contains a version identifier, suggesting the malware is maintained as part of an evolving codebase, and a parameter (STARTUP_TYPE) that defines the persistence mechanism (e.g., registry-based startup). While this value is statically defined in the sample, its presence indicates the malware is designed with configurable deployment options, meaning different builds could easily switch persistence techniques without modifying core logic.
The most relevant configuration parameter is PASSWORD, which is used as a shared secret for multiple purposes:
- It acts as a static authentication token during the initial C2 handshake, allowing the server to validate incoming clients.
- It is used as a decryption key for downloaded payloads or modules, enabling the malware to securely receive and execute additional functionality at runtime.
Overall, the configuration structure shows that the malware is designed to be flexible and extensible, with support for dynamically delivered modules and adjustable behavior across different deployments.
The configuration structure is illustrated below:
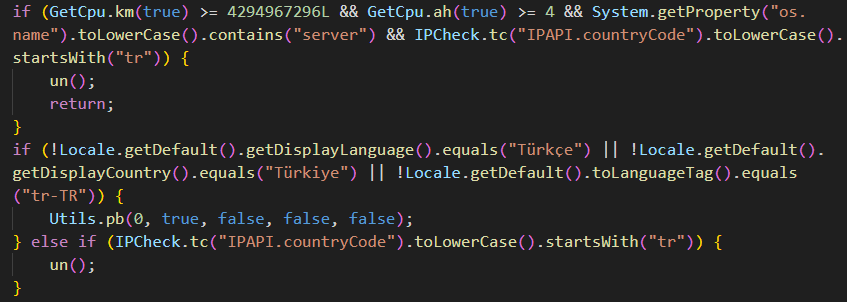
Geofencing
The malware implements multiple layers of geofencing and environment filtering to control where its malicious payload is executed. Initially, it checks the system’s locale, language and country settings, specifically requiring the environment to match Turkish language and region.
It also verifies the machine’s external geolocation via an IP lookup and proceeds only if the reported country code begins with “TR”. This layered geofencing approach helps the malware restrict execution to systems located in Turkey.
While this behavior contributes to anti-analysis and sandbox evasion, it also likely reflects intentional targeting of a specific geographic region. By limiting execution to Turkish environments, the operators can reduce exposure to international security researchers and automated analysis systems, which are often hosted outside the target region. Additionally, region-specific targeting may align with campaign objectives, such as focusing on local victims, language-specific lures or operational constraints (e.g., infrastructure, monetization channels or legal risk).
Overall, this geofencing mechanism suggests the malware is not opportunistic but instead part of a targeted campaign with a defined geographic scope, using location checks both to evade detection and to ensure it operates only in intended environments.
File encryption
If the infected system passes the geofencing checks, the malware first weakens the system’s defenses by executing a series of PowerShell and registry commands. These actions are designed to:
- Disable or weaken Microsoft Defender.
- Suppress security notifications.
- Remove recovery mechanisms such as Microsoft Volume Shadow Copy Service (VSS).
- Disable Windows Update.
- Hide ransomware protection features.
- Enumerate installed antivirus products.
- Interfere with endpoint protection integrations in Windows Explorer.
After these preparatory steps are completed, the malware proceeds to download a ransomware plugin specifically designed to work with this customized version of Adwind RAT. This module is also implemented in Java, and it is responsible for encrypting files across all available drives. The module relies exclusively on Tor for command-and-control (C2) communication and is capable not only of encrypting files but also of deleting and exfiltrating them. During the handshake with the C2 server, it uses the prefix JANAWARE, which is why we have dubbed it JanaWare ransomware.
Once file encryption is complete, the malicious Java application drops the ransom note in multiple folders, as observed in the Procmon capture logs:
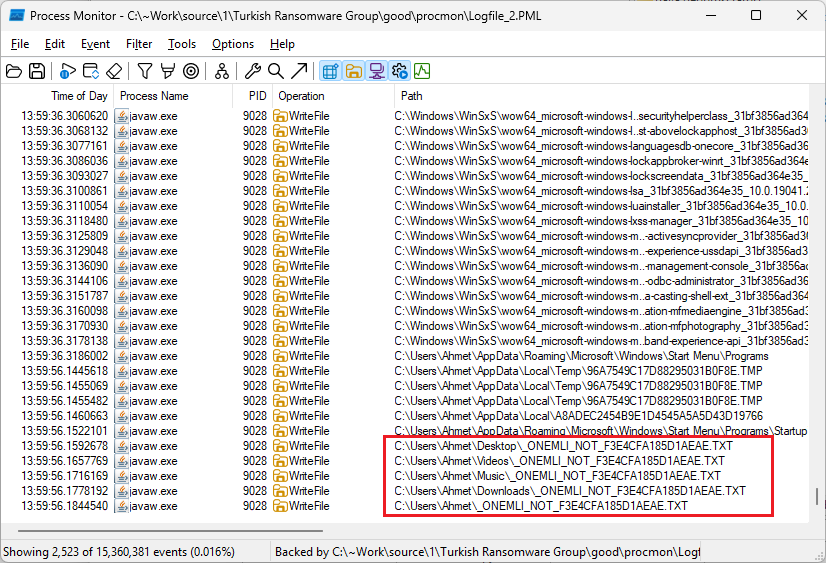
The filename is partially randomized, but a fixed component is configured within the malware itself. For example, in _ONEMLI_NOT_F3E4CFA185D1AEAE.TXT, the prefix _ONEMLI_NOT_ is defined in the malware code as shown below:
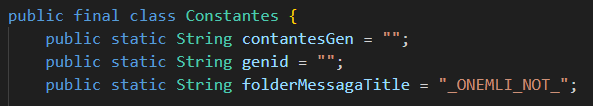
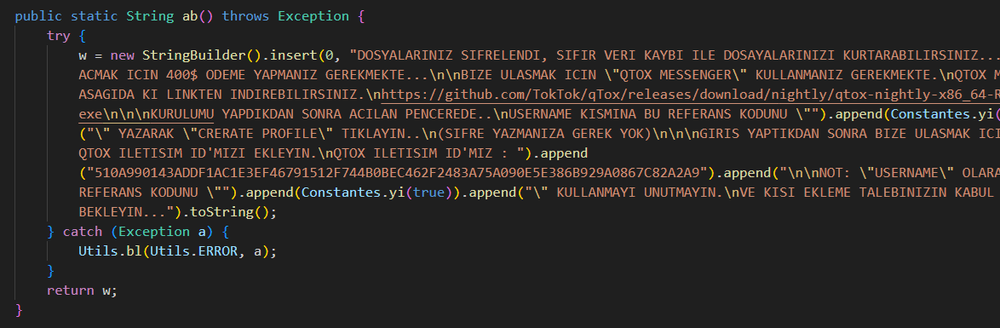
In Turkish, ONEMLI NOT translates to Important Note. The content of the ransom note is also embedded directly within the malware, further highlighting that this threat is specifically targeting Turkish users. For example, the malware contains the following Java method that constructs the note:
Based on static analysis of the Java classes, the ransomware employs AES encryption, with the encryption key transmitted to the C2 server over Tor. As a result, recovery of encrypted files is not feasible without access to the C2 infrastructure, which is highly unlikely.
Conclusion
The analysis presented in this report highlights a relatively low-profile but persistent ransomware operation that we refer to as JanaWare Ransomware. Unlike large-scale ransomware campaigns targeting enterprises, this operation appears to focus primarily on Turkish users and smaller organizations, combining geofencing, Turkish-language artifacts and modest ransom demands. The ransomware is delivered as a module for a customized version of Adwind RAT, allowing the operators to deploy it selectively after initial compromise.
Technically, the malware employs several measures to hinder detection and analysis, including heavy obfuscation, dynamic module loading and self-modifying binaries that generate unique hashes for each infection. Despite evidence suggesting the campaign has been active for several years, its regional focus and relatively small-scale operations likely helped it remain largely unnoticed. This case demonstrates how targeted, localized ransomware campaigns can quietly persist in the threat landscape.
Detection by Acronis
This threat has been detected and blocked by Acronis EDR / XDR:
IoCs
Samples
Command and control servers






