Acronis protects South Korean civil society groups
Detecting New SuperBear Trojan delivered via targeted spear phishing.

- DescriptionResearchers have discovered a recent phishing attack, likely targeting South Korean civil society groups that has unveiled a remote access trojan (RAT) called SuperBear.
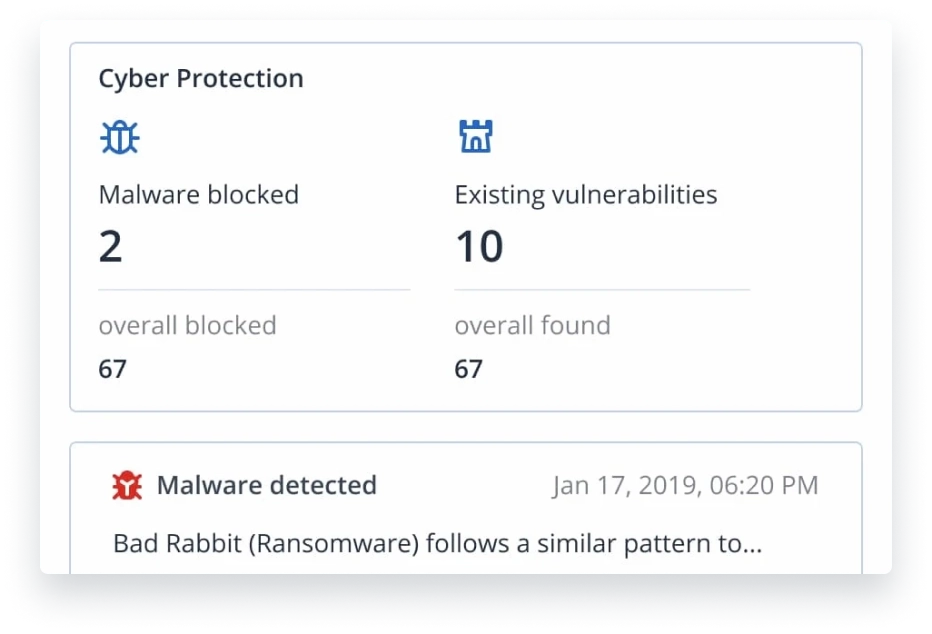
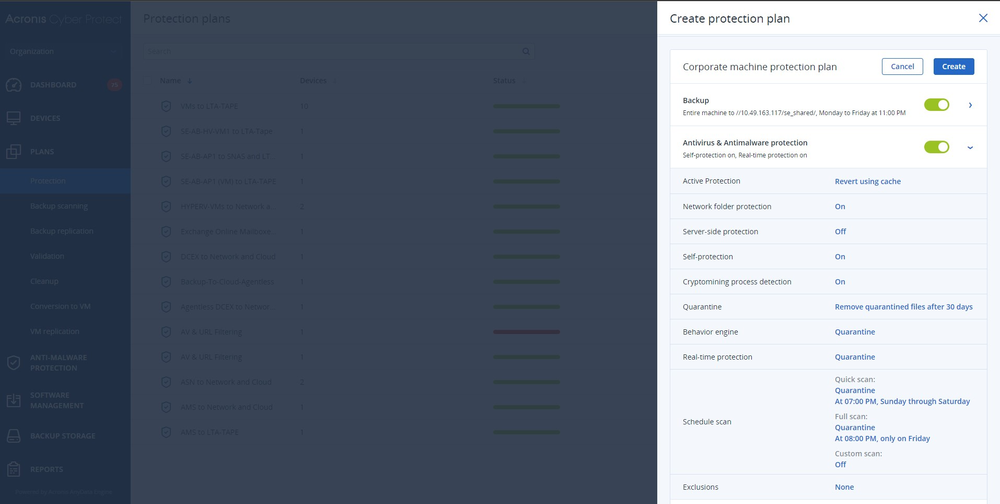
- Key challengesThe attack leverages previously unseen RAT that can bypass endpoint defenses that don’t leverage complex behavioral based detect – such as antivirus solutions.
- RisksThe SuperBear trojan communicates with a remote server for data exfiltration which can pose severe risks for organizations’ data alongside financial ones such as regulatory fines related to sensitive data leakage.
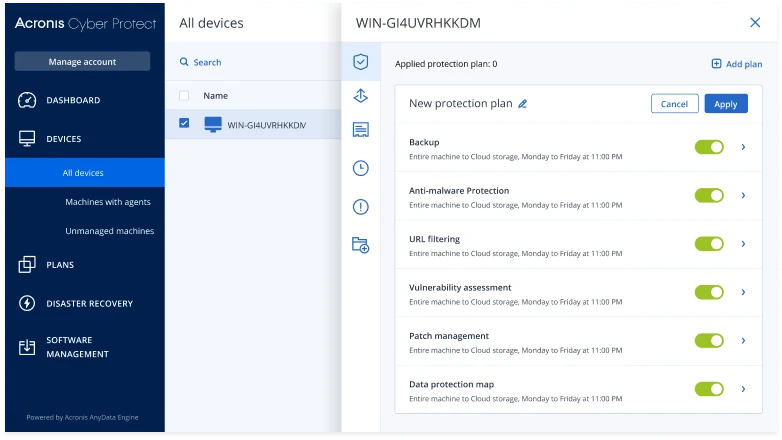
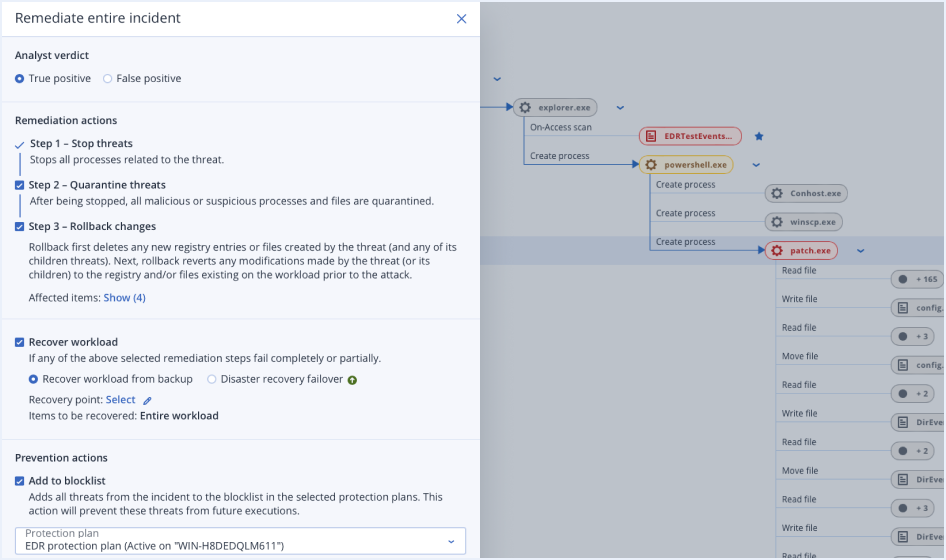
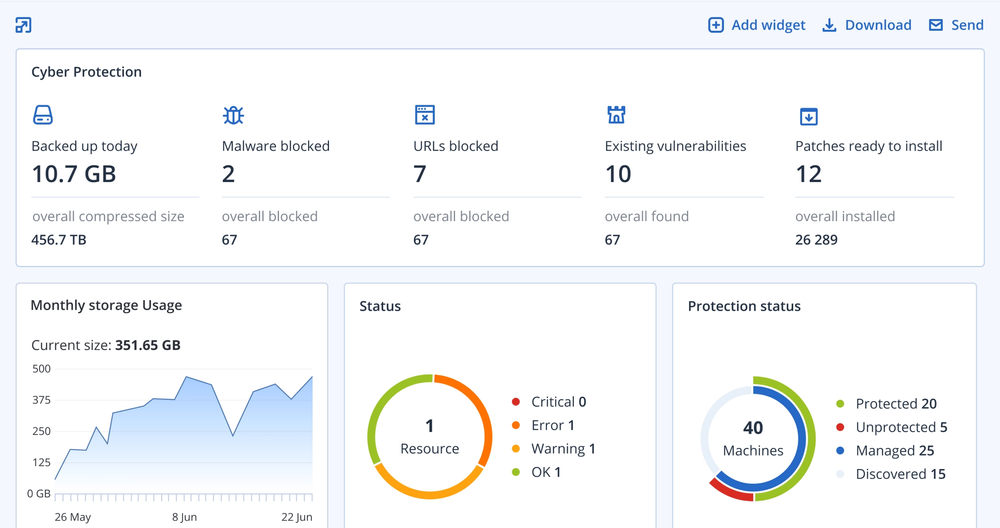
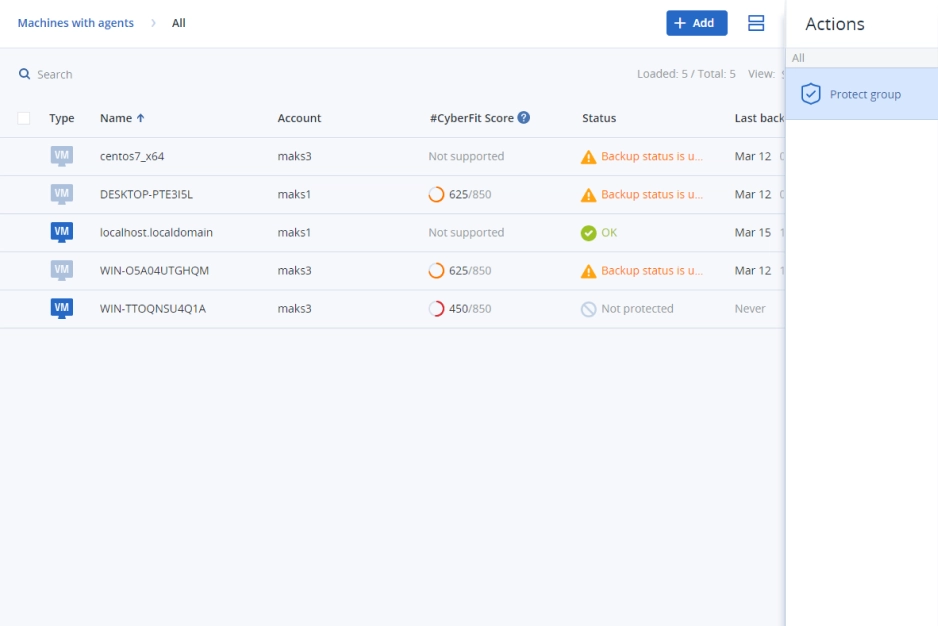
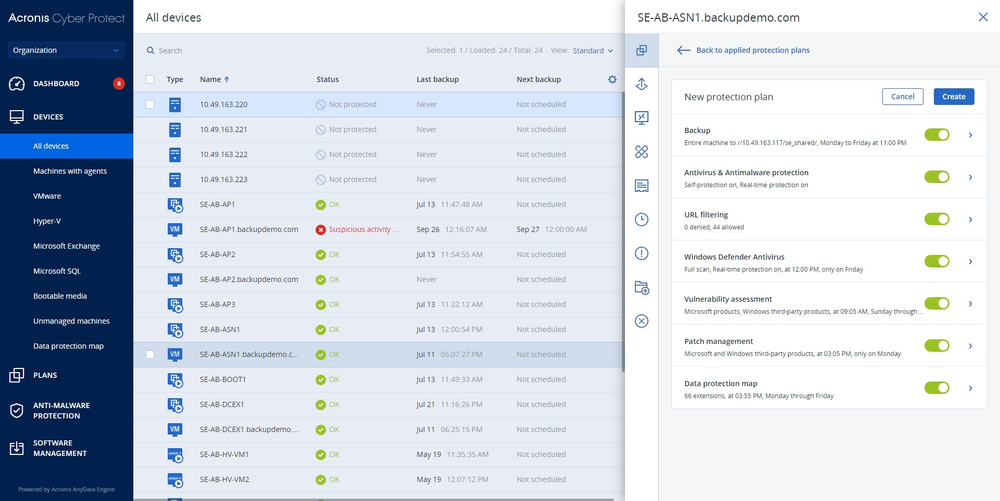
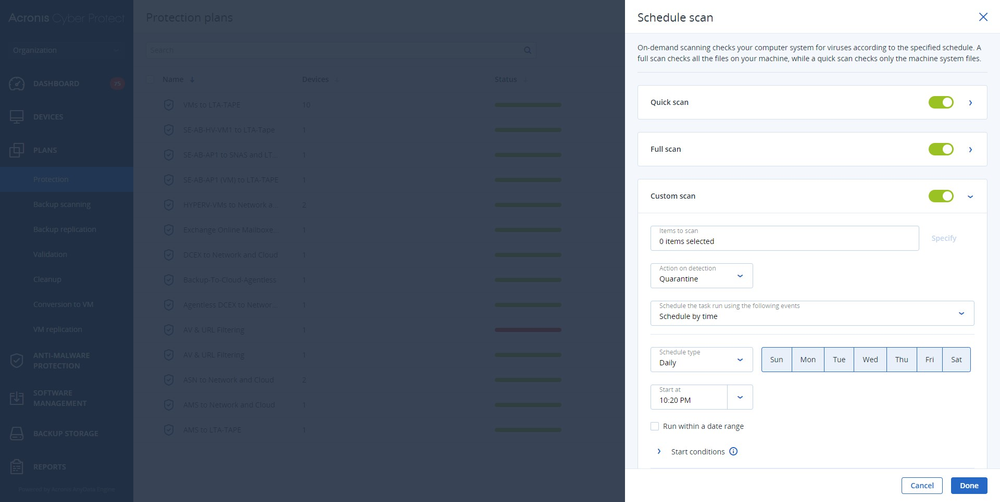
- Our solutionAcronis EDR continuously monitors endpoint activity and can identify suspicious behavior associated with SuperBear's distribution vectors. Acronis EDR can flag suspicious activities and subsequent data exfiltration attempts and provide early detection of the threat, mitigating the risk for users.