Research by Kevin Reed, Acronis CISO; Alex Koshelev, Acronis Security Researcher; and Ravikant Tiwari, Acronis Senior Security Researcher
When a security manufacturer learns of critical vulnerabilities in their devices, there is an expectation they’ll act quickly to fix the problem. Yet August 2019 became the first of the many months when Acronis would patiently wait for an update (in vain, as it turns out) from one manufacturer in particular.
During a routine network security audit session last year, we uncovered several critical vulnerabilities in devices from GeoVision, the Taiwanese fingerprint scanner and surveillance tech manufacturer. We discovered the devices had a backdoor password with admin privileges, the reuse of cryptographic keys, and the disclosure of private keys.
Here is the timeline of our communication with GeoVision:
- August 2019 – Acronis initially contacted the manufacturer, sharing our findings
- September 2019 – We announced the beginning of the 90-day courtesy period
- December 2019 – We contacted the Singapore Computer Emergency Response Team (SingCERT) and informed them of findings. SingCERT and Taiwan’s TWCERT then requested that we postpone releasing our findings by a month.
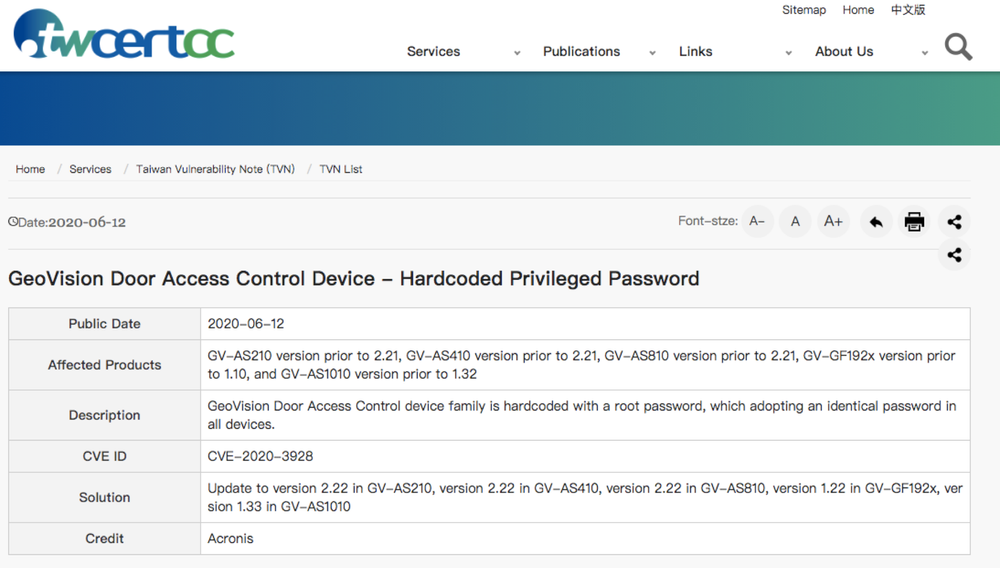
- June 2020 - Three vulnerabilities were reported as fixed, yet the most critical one seems to remain unfixed. GeoVision still as not responded or acknowledged the findings.
Status update: As of today, out of four critical vulnerabilities identified, only three have been reported as fixed by the manufacturer. Last week, TWCERT confirmed the availability of the new version (v. 1.22) – but we still see no firmware update released on GeoVision's website.
A good start for state-sponsored attackers
Acronis’ security team found four critical vulnerabilities in GeoVision's devices, including a backdoor password with admin privileges, the reuse of cryptographic keys, and the disclosure of private keys to everyone. All of these vulnerabilities could allow state-sponsored attackers to intercept potential traffic.
The three vulnerabilities with CVE IDs CVE-2020-3928, CVE-2020-3930, and CVE-2020-3929 appear in fingerprint scanners, access card scanners, and access management appliances across the whole world. We confirmed at least six device models are vulnerable.
Some of the potentially exploitable devices appear on Shodan, with clusters show up in Brazil, the U.S., Germany, Taiwan, and Japan. The device we ran a security audit on was from a Singapore-based company. You can see the discovered devices breakdown by country here on Shodan tracker.
Technical details of our findings
1. Undocumented hardcoded password in families of GeoVision support products
We were able to confirm that at least the following GeoVision product firmware contain a hardcoded root password:
- GV-AS210 (http://classic.geovision.com.tw/english/Prod_GVAS210.asp) versions 2.20, 2.21
- GV-AS410 (http://classic.geovision.com.tw/english/Prod_GVAS410.asp) versions 2.20, 2.21
- GV-AS810 (http://classic.geovision.com.tw/english/Prod_GVAS810.asp) version 2.20, 2.21
- GV-GF192x (http://www.geovision.com.tw/product/GV-GF1921%20GV-GF1922) version 1.10
- GV-AS1010 (http://www.geovision.com.tw/product/GV-AS1010) version 1.32
The password is not documented, exposing customers to an unknown risk. By default, ssh server is not running on the device, however there is a hidden URL in the device management interface [https://%3cip.of.the.device%3e/isshd.htm]. If this URL is accessed, Dropbear ssh will be started on port 8009.
Accessing this URL requires device password, but since the default password (admin:admin) is rarely changed in a typical setup, it is entirely possible to access the device with the root privileges.
2. Shared cryptographic keys
We were able to confirm that at least the following GeoVision product firmware contain hardcoded, commonly shared cryptographic private keys for ssh and https:
- GV-AS210 (http://classic.geovision.com.tw/english/Prod_GVAS210.asp) versions 2.20, 2.21
- GV-AS410 (http://classic.geovision.com.tw/english/Prod_GVAS410.asp) versions 2.20, 2.21
- GV-AS810 (http://classic.geovision.com.tw/english/Prod_GVAS810.asp) version 2.20, 2.21
- GV-GF192x (http://www.geovision.com.tw/product/GV-GF1921%20GV-GF1922) version 1.10
- GV-AS1010 (http://www.geovision.com.tw/product/GV-AS1010) version 1.32
Exposing private keys opens the way for man-in-the-middle attacks.
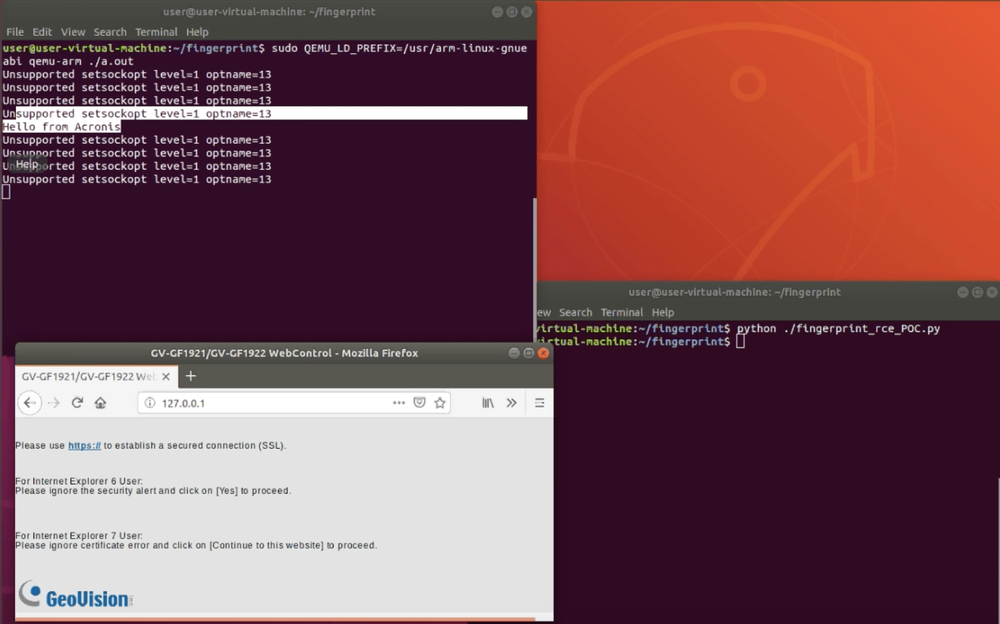
3. Buffer overflow vulnerability leading to unauthenticated remote command execution
We were able to confirm this finding in GV-GF192x (http://www.geovision.com.tw/product/GV-GF1921%20GV-GF1922) version 1.10 firmware, although we have high confidence that this vulnerability is present in other Geovision products as well.
The vulnerable program is /usr/bin/port80 in the firmware (SHA256: 5B531E50CFA347BBE3B9C667F8D802CDECC6B1CD270719DAC5ECE4CE33696D3A). We provided PoC code and demo video for this vulnerability to SingCERT.
This vulnerability allows attackers to run unauthorized code on the devices and requires no prior authentication.
4. Information disclosure vulnerability
We were able to confirm this finding in GV-GF192x GF192x (http://www.geovision.com.tw/product/GV-GF1921%20GV-GF1922) version 1.10 firmware, although we have high confidence that this vulnerability is present in other GeoVision products as well.
System logs are available without authentication at [http://%3cip.of.the.device%3e/messages.txt] and at [http://%3cip.of.the.device%3e/messages.old.txt], which enables attackers to read system logs, which helps with further attack planning.
What this means for end-users
As of this post, we have yet to hear whether GeoVision has released an update on the last and most critical vulnerability – the buffer overflow zero-day wormable vulnerability. With a 10/10 CVSS rating, it allows malicious actors to reprogram the device's protocols and commands.
When exploited, this vulnerability lets attackers overrun the memory buffer used for the "Host" header. The overflow enables the memory structure responsible for memory management to be overwritten. By overwriting the pointers in this structure, attackers can redirect program execution to their own code, performing different commands.
“Host: “ + free_space + pointer_to_new_heap(only first free bytes!) + “\r\n” + our_list_of_chunks + free_space.
In free space we can place our shellcode(I used the second free_space). The part (“Host: “ + free_space + pointer_to_new_heap(only first free bytes!)) will be placed into g_Host buffer and the pointer to chunks list will be rewriting.
Using these vulnerabilities, attackers could remotely open doors without the keycards, install Trojans on those devices, establish their persistence on the network, spy on internal users, and steal fingerprints and other data – all without ever being detected.
How critical is this vulnerability? Well, fingerprint data could be used to enter your home and unlock personal devices. Photos can be easily be reused by malicious actors for identity theft based on biometric data. Attackers could also sell access to any doors protected by these devices, offering a free entry to one's home or place of work.
Security technology products with this kind of critical vulnerability don’t actually deliver the security they promise.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 60+ countries. Acronis Cyber Platform is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.



