Phishing attacks, which involve criminals posing as legitimate contacts use emails and instant messaging to trick victims into providing valuable information like login credentials and banking or credit card details, is a major challenge for organizations ... and it’s on the rise.
Last year, Verizon’s Data Breach Investigations Report concluded that phishing was the number one attack vector used in successful data breaches. Their report also revealed that 94% of malware was delivered via email, with phishing emails being the most prevalent type used. Meanwhile, other research from 2019 showed that spear-phishing emails, which target specific individuals or organizations (rather than “casting a wide net”) are used by nearly 65% of all known groups carrying out targeted cyberattacks.
Unfortunately, phishing attempts are on the rise. The Anti-Phishing Working Group’s (APWG) Phishing Activity Trends Report for Q1 2020 notes that phishing attacks rose to the highest level since 2016, with more than 60,000 phishing sites being reported in March alone.
As a member of APWG, Acronis can confirm that we’ve seen an uptick as well and Acronis employees of all levels receive well-crafted phishing emails every day. Let’s look at one of the latest examples.
Real phishing email received by an Acronis c-level executive
Recently one of Acronis’ top managers found the phishing email pictured below in his inbox. For a security professional or someone in the cybersecurity industry, the attempt is relatively easy to recognize. Yet this example shows how employees who are not as well-trained regarding security might easily fall victim to this kind of attack, leading to compromise and data loss, unless a strong cybersecurity product is running on their machines.
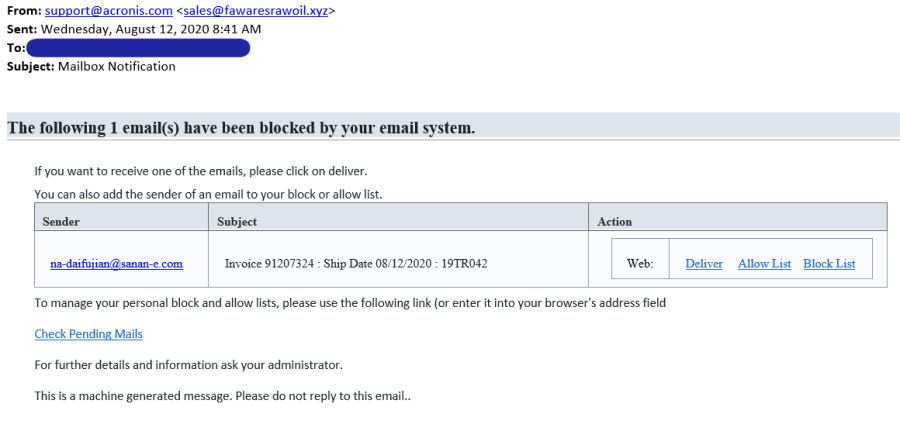
As we can see, email seems to be originated from Acronis support. If you do not check the actual email address of the sender and your email client does not show it by default, you might fall into this trap.
Since the employee who received this email works with invoices on a daily basis, it appears that the cybercriminals who sent the email likely conducted some social reconnaissance before sending it. Even if they didn’t do that research, however, a lot of employees can be responsible for invoices, so reason and theme of email can be an effective ploy. The bad guys will play on common experiences and fears because they might get a hit if the organization’s spam filter or email AV makes a mistake and lets the message through. Last but not least, we see several malicious links included in the email. If you do not check them and blindly click, they will bring you to malicious websites.
As stated above, this example is relatively easy to spot – but what if the criminals behind this attack used more sophisticated techniques like zombie phishing? Zombie phishing is the nasty trick of hijacking the business account of someone in your company or at one of your partners, finding some relevant email thread, and then continuing the conversation with an email that delivers malware or malicious links. Since it comes from an actual colleague’s address – from a personal contact like your boss – it’s hard to do something about it unless you have proper security in place.
Another trick that is typically used in more sophisticated attacks is the usage of shortened URLs, like the ones made with Bitly. You can’t check the actual address by hovering your cursor over the link and these URLs may not yet be added to anti-phishing databases.
Safety through web filtering
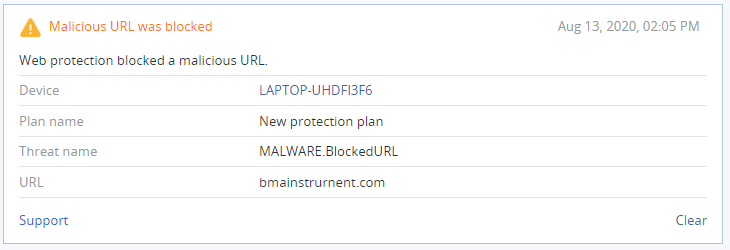
Given these challenges, your machine needs to be protected by URL filtering, which is also called web filtering or web antivirus. It is not sufficient protection on its own but, as a part of a multilayered defense, it does a good job of stopping these kinds of attacks.
Acronis Web Security delivers URL analysis and filtering functionality from our cloud reputation base (Acronis Cloud Brain). Local detection rules for malicious and phishing URLs are also kept in our Acronis Cyber Protection Solutions, ensuring protection even when there are internet connection disruptions.
Acronis URL filtering is enhanced with payload analysis and a machine learning model, which analyzes the link itself and the page’s structure. As a result, it can:
- Stop silent drive-by downloads and intercept HTTP/HTTPS requests
- Protect against any phishing sites and block sites that distribute malware
- Identify scams and infections using themes that leverage actual threats, such as COVID-19
- Integrate intelligence from industry partners into Acronis’ signature- and AI-based detection
The machines of all Acronis employees are protected by the URL filtering integrated into Acronis Cyber Protect, which is why the phishing attempt against our executive was immediately detected and blocked.
Final thought
Clearly the threat of phishing in all of its forms is not going away anytime soon, and the rising number of attacks should concern organizations of any size. Thankfully, there are strategies and solutions that will minimize or effectively eliminate the risk you face.
Read more about Acronis’ multilayered protection in the following whitepaper, or consider trying Acronis Cyber Protect for yourself to ensure the URL filtering that stopped the attack against our executive protects your executive – and all of your employees.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 20,000 service providers to protect over 750,000 businesses.





