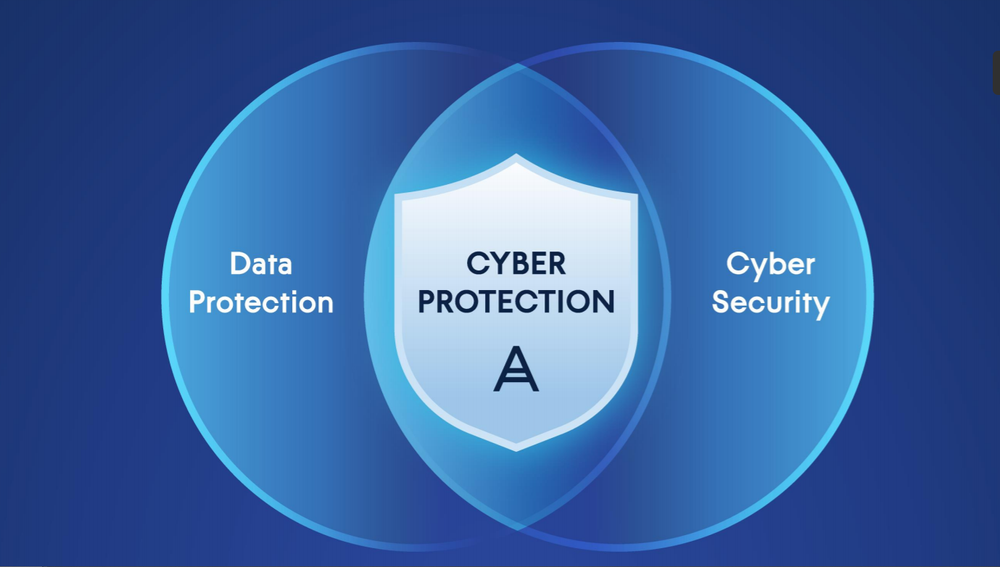
Cyber protection is the integration of data protection and cybersecurity — a necessity for safe business operations in the current cyberthreat landscape.
In the modern world, companies face a variety of threats to data and digital operations. These risks may be internal, caused by employees or contractors — or external, caused by cybercriminals, nation-states, or even your own customers. They may be deliberate acts of espionage, disruption, or theft — or accidental acts of negligence and human error. No matter the vector or motivation, cyberthreats can be absolutely devastating to organizations — and to the individuals they employ and serve.
It’s fair to say that data is now the world’s most valuable resource. It’s at the core of nearly all business operations and decision-making. And the growth of data is explosive, doubling in volume every two years. Effective cyber protection is increasingly necessary to safeguard organizations, people, and our society at large.
How is cyber protection different from cybersecurity?
Cybersecurity is the practice of defending your networks, systems, and applications from cyberattacks. Types of cybersecurity include, but aren’t limited to:
- Network security — securing internal networks against unauthorized access, with tools like remote access management and two-factor authentication (2FA)
- Application security — preventing data and code in business-critical software (both in use and in development) from being stolen or hijacked, such as with penetration testing and encryption
- User education — teaching employees and customers best practices for avoiding cyberthreats, such as malware and phishing attacks
Where cybersecurity and cyber protection differ is in their relationship to data. Cybersecurity does not focus on data protection itself, but rather on guarding the systems that make data access, storage, transfer, and authentication possible. If bypassed or disabled by unknown threats, cybersecurity solutions can’t do much to aid you with restoring data and systems in a timely fashion.
Cybersecurity is naturally an important part of staying protected online, but modern challenges in data protection have rendered this approach insufficient on its own — especially with an organization’s livelihood on the line. Rather, cybersecurity must be integrated with data protection to more fully cover workloads and to address new forms of malicious cyberattacks.
What cyber protection issues do businesses face?
The potential for data loss, leakage, corruption, manipulation, and theft has never been higher. Data is increasingly at the core of day-to-day business operations, and companies are generating staggering volumes of it — much of which is highly sensitive, and may contain personally-identifiable information about customers and employees.
Meanwhile, cybercriminals are using automation to create and iterate new cyberthreats with blinding speed. They’re even personalizing their attacks with information mined from corporate websites and social media networks, piquing their targets’ curiosity and enticing them to put their better judgment aside and open questionable hyperlinks or email attachments.
Protecting business-critical data is key, but actually doing so is a considerable task. Organizations face three primary issues in managing their digital operations:
Security
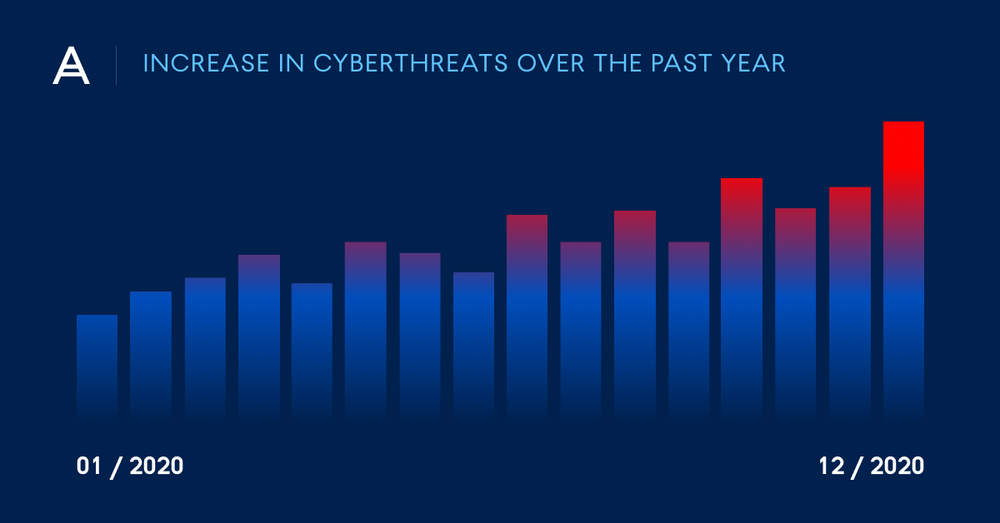
Cyber threats already pose an enormous challenge for businesses, and as operations continue to shift towards digital-first models, there’s every indication that these threats will continue to rise. Ransomware alone is responsible for tens of billions of dollars in annual damages worldwide. That growth is powered by tech-savvy cyber criminals.
The same cutting-edge technologies used by legitimate companies are also being exploited by criminal gangs and even rogue nations. Drawing on artificial intelligence and huge amounts of computational power, malicious actors are industrializing their malware capabilities — outpacing the effectiveness of many traditional anti malware solutions, and making zero-day attacks more damaging.
Cyber criminals operate with a wide and growing variety of tactics. Some will attempt to lock up data and demand a ransom for its restoration — and, increasingly, will exfiltrate sensitive information for public release if their demands are not met. Others target weaknesses in regular business processes to interrupt services or discretely siphon funds. They may target your software vendors, hoping to compromise scores of downstream businesses with a single blow. Often, they’ll go after data backups directly to increase the impact of their attacks and the leverage they hold over victims.
In this evolving threat landscape, companies need cyber protection solutions that can safeguard large stores of critical data across increasingly complex infrastructures, while keeping up with ever-changing hazards — and that can verify the authenticity of their backups.
Complexity
Between mobile devices and the internet of things (IoT), computing is shifting closer to the data’s origin point. Companies demand lower latency, faster response times, and continued availability of services even with intermittent connectivity. Soon, as few as 1% of devices may be located in actual data centers — while smart appliances, home automation systems, and wearables handle a larger portion of processing needs.
But while decentralization allows these in-demand benefits, it also adds incredible complexity to the task of data protection. Rather than managing and protecting a centralized data center — with standardized, familiar equipment — IT pros must now find a way to safeguard every device and endpoint that accesses and stores their company’s data. Fail to do so, and a successful cyberattack against some other brand’s internet-connected refrigerator could put your operations at risk.
Cyber Protection Cost
Between the global shift to online operations and the need to safeguard colossal data stores across a wide variety of devices, the cyberthreat attack surface is larger than ever. Protecting business-critical data effectively requires many different capabilities. Some businesses use different solutions for each of these needs — one product for antivirus, another for data backup, perhaps some paid add-ons for patch management or URL filtering. But covering every risk factor can get expensive, and this multi-product web of complexity is itself a risk factor.
As more and more solutions are added to an organization’s protection plan, technicians must devote an increasing amount of time just to staying on top of what is and isn’t secured. Finding products that safeguard your entire attack surface can be tricky — especially if you have multiple types of hardware and operating systems to protect — and newly-installed updates to one solution may introduce incompatibilities with others.
When a business has to spend too much time and energy managing their security solutions, they’re not enjoying the full value or effectiveness of the protection they’ve paid for.
What are the five vectors of cyber protection?
It’s clear that — in the modern cyberthreat landscape — businesses need solutions that provide more than just data backup or antivirus protection. They need data to be available at any time, from any location. They need control over who can view and access that data, keeping sensitive information out of the wrong hands. They need it to be secured against cyberthreats, and against natural disasters or other events that could cause data loss and interrupt business continuity. And when they restore data from backups, businesses need to know that it hasn’t been modified or corrupted by nefarious actors.
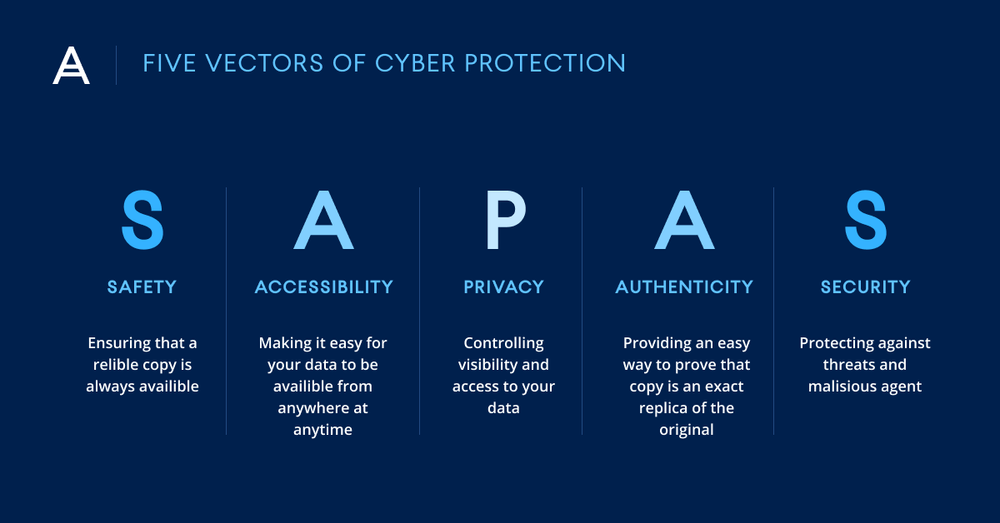
To meet these needs, Acronis develops solutions that address all of the five vectors of cyber protection, also known by the acronym SAPAS:
Safety — Ensuring that a reliable copy of your data is always available Accessibility — Ensuring that data is available from any physical location, at any time Privacy — Ensuring full control and transparency over who can view and access your data Authenticity — Ensuring that backed-up data is an exact, unmodified replica of the original data Security — Ensuring that data, apps, and systems are protected against cyberthreats
Meeting the five vectors of cyber protection is technically possible with disparate solutions, but this approach tends to be expensive and tough to manage. Relying on separate tools for needs like backup, antimalware, remote management, and disaster recovery requires IT technicians to learn and maintain each of these solutions. Companies with multiple device and OS types to secure may struggle to keep capabilities aligned, creating gaps in workload protection. And having multiple agents running can overload systems, while each product update threatens to cause incompatibilities.
All-in-one cyber protection solutions by Acronis
Business continuity interruptions — even brief ones — are expensive due to missed transaction opportunities and lost productivity, while data breaches can incur steep regulatory fines and result in loss of private information and trade secrets. Both situations threaten to dramatically harm your reputation. Organizations that rely on legacy IT solutions are putting sensitive information — and even their very survival — at severe risk.
Acronis is able to address these concerns with integrated solutions that enable comprehensive cyber protection — because they’re built to address the five vectors of cyber protection at every step, from the underlying infrastructure to the cloud-based delivery platform:
- Acronis Cyber Protect Cloud — a platform that enables service providers to deliver cyber protection in an easy, efficient and secure way. With one solution, users gain access to backup, cloud disaster recovery and DraaS (disaster recovery as a service), ransomware protection, file sync and share, and blockchain-based file notarization and e-signature services, all managed from a single console.
- Acronis Cyber Protect — a single solution integrating backup with next-generation, AI-based antimalware and protection management. The integration of multiple protection technologies not only increases reliability — it also decreases the time required to learn, deploy, and maintain new capabilities. With Acronis Cyber Protect, users enjoy complete cyber protection against modern threats.
- Acronis True Image — the only personal solution that delivers easy, efficient, and secure cyber protection with a unique integration of reliable backup and cutting-edge antimalware technologies — safeguarding data against all modern threats. Reduce the complexity and cost of safeguarding data, so you’ll never have to worry about disruptions to your digital life.
Only integrated cyber protection solutions can provide effective security for entire modern workloads across multiple domains — and keep up with the risk presented by evolving, cutting-edge cyberthreats. This unified approach allows Acronis to deliver easy, efficient, and secure cyber protection for organizations and businesses of any size.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 20,000 service providers to protect over 750,000 businesses.