
Recently, Acronis announced the sunsetting of Acronis Cyber Backup and incorporated the features in that solution into one of Acronis’ starship solutions, Acronis Cyber Protect. To better understand why Acronis made this move, read on and learn all about backup and the importance of integration with cybersecurity to ensure complete protection and security of your business’ systems and data.
What is a computer backup?
A computer backup is the process of making exact copies of your production systems and / or data at a given point in time. Some computer backup systems provide full-image backups that include the operating system (OS), data and applications, while other systems only back up your documents, files and folders. When you perform an initial backup, the software copies your entire system or data. Subsequent backups are typically incremental or differential backups that only capture the changes since the last backup, which saves both time and storage space. All of these features will be discussed in more detail later in this article.
Backup data from a computer hard drive can generally be saved to any one of a number of media, including:
- Network storage devices such as NAS (Network Attached Storage), SAN (Storage Area Network) or simple network share
- Other local hard drives
- External storage devices such as a USB flash drive or USB hard drive
- Online or cloud storage accounts
- Another hard drive partition (a disk partition is a separate and distinct section on the same hard drive)

To be effective, a backup must be repeated to preserve or record any changes to the data since the last backup was created. There are many backup solutions that automate the backup, including the ability to schedule ongoing backups to keep the backed-up data current. We will discuss how these ongoing backups are created later in this article.
Why do businesses need to back up their data?
Your business depends on the availability and integrity of your data, but what happens if an event — such as a flood, fire, accidental data deletion, cyberattack, hardware / software failure, or any type of disaster — compromises, steals or deletes your data? Without a computer backup, your business can be “dead in the water.”
By backing up your computers following the 3-2-1 backup rule, your business can recover from any event.
The 3-2-1 backup rule
The 3-2-1 backup rule stipulates that every business should maintain three copies of their data (one production copy and two backups), across two types of media, with one backup stored offsite, such as in the cloud.
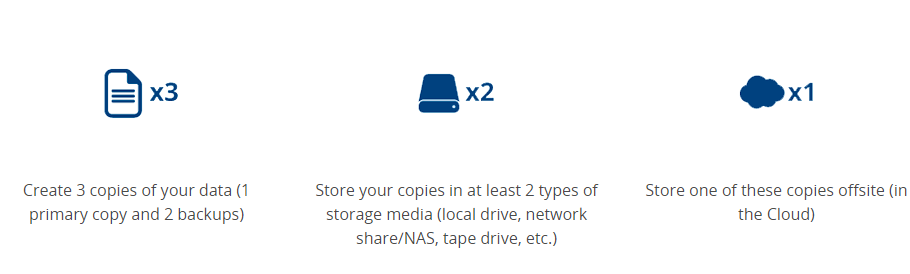
- Create 3 copies of your data (1 primary copy and 2 backups)
- Store your copies in at least 2 types of storage media (local drive, network share/NAS, tape drive, etc.)
- Store one of these copies offsite (in the Cloud)
Local backup vs. cloud backup
A local backup is any backup that is stored in the same physical location as your business’ computers or IT center. It is important to keep a local backup for the quick recovery of selected files and folders. Sometimes a user may inadvertently delete a file and may need to recover just that one file fast. Having a local backup on hand is the fastest way to accomplish this.
A cloud backup is any backup that is stored in a public or private cloud. A cloud backup is important for two reasons:
- If your IT center is destroyed by a disaster, there is a good chance that your local backups are destroyed as well. Fortunately, a backup in the cloud will be immune to local disasters if you maintain your backups in a cloud data center that is located at least 100 miles from where you store your local backups.
- If your business suffers a cyberattack, the chances are good that your local backups are compromised as well. Storing a backup copy in the cloud ensures the backup is protected against attacks.
Hybrid backup
Hybrid backup is a feature of backup software that lets you back up to a local device and also to servers or data centers that are located in a different geography or in the cloud. A solution that offers hybrid backup is the easiest way for a business to follow the 3-2-1 backup rule.
What data should be backed up and at what frequency?
Every business should be backing up all critical data files that change frequently. These include:
- Customer information
- Point-of-sale files (e.g., credit card transactions)
- Invoicing, billings, accounts receivables and payables
- Personnel files and payroll information
- Text documents, spreadsheets, databases
- Emails, calendars, schedules, distribution lists
- Collaboration tools software such as Jira, Asana, etc.
- All line-of-business applications
Disk-image backups
While there are many solutions that back up mission-critical data, few solutions offer the ability to back up an entire computer — the operating system (OS), applications and data. The advantage of a full-disk image backup is that you can save complete images to a variety of backup targets including local disk, network storage, tape and cloud, and have the ability to recover the complete image or selected files, folders and applications. You can then recover an entire PC in minutes to the same location, to dissimilar hardware, or to a virtual desktop.
It is recommended that a business back up at least once a week, but preferably once every day ― depending on your recovery point objectives (RPOs) and recovery time objectives (RTOs).
What are RTO and RPO when talking about backup?
Once you decide on what systems and / or data to back up, you need to decide how often to back up and define a backup schedule. Your employees are constantly changing data. If an event such as a disaster happens, all the data created since the latest backup to the moment of failure will be lost. This period is called the Recovery Point Objective (RPO) — the maximum period of time that you are willing to lose data because of an event.
A shorter RPO means losing less data, but it requires more backups, more storage capacity, and more computing and network resources for a backup to run. A longer RPO is more affordable, but it could mean losing more data.
Many small and medium-sized businesses (SMBs) usually agree on an RPO of 24 hours, which means your business needs to back up daily. With modern backup solutions, you can implement RPOs in as short a time as a few minutes. You can also have tiered RPOs — shorter RPOs for critical systems, and longer RPOs for secondary systems.
Recovery time objective (RTO) describes how fast your business can recover from a disaster — from the moment the disaster happens until the moment your business returns to normal operations. When your systems are down, your business loses money, and you need to recover fast to minimize losses. This entices every business to agree on a shorter RTO. However, a shorter RTO requires faster storage, networks and technologies — so it’s more expensive. For many companies, an RTO of a few hours is the norm.
What are the 3 types of backup
There are three types of data backup that vendor solutions offer to ensure the best backup / recovery speeds and the best storage utilization.
Full backups copy everything you want to protect, and you want to perform a full backup the first time you back up a system. Full backups take time, which is why software providers offer other types of data backup.
Differential backups back up only the files that changed since the last full backup. For example, let’s assume you do a full back up on Monday. On Tuesday, you back up only the files that changed since Monday. On Wednesday, you back up only the files that changed since Monday and so on, until the next full backup.
Differential backups are faster than full backups because you are backing up a smaller volume of data. However, the volume of data grows with each differential backup until the next full back up. While differential backups are more flexible than full backups, they are cumbersome to do more than once a day.
Incremental backups also back up only the changed data, but they only back up the data that has changed since the last full or incremental backup.
If you do an incremental backup on Tuesday, you only back up the data that changed since the incremental backup on Monday. The result: much smaller and faster backups. With incremental backups, the shorter the time between backups, the less volume there is to back up. In fact, with modern data protection software like Acronis Cyber Protect, the backup volumes are so small and the backup so fast, you can back up every hour, or even more frequently.
While incremental backups give much greater flexibility and granularity, they take longer to restore because the backup has to be reconstructed from the last full backup and all the incremental backups since.
Why is data backup important?
Every day, cybercriminals are launching more sophisticated, clever attacks using automation and artificial intelligence (AI). Now, they can scale their attacks with less effort, which is why the industry is now seeing upwards of 500,000 new threats every day. As cyberattacks are now one of the main reasons businesses lose their data, Acronis has supercharged their cyber protection solution to enable its customers to require only one license, one agent and one management console to preserve data with backups, as well as the security of that data with cybersecurity features such as anti-malware and antivirus, fail-safe patching, forensic backup and more.
Here are just a few examples of recent data breaches that have affected even the largest of corporations.
- Tech giant Microsoft and secure identity platform Okta have become the latest victims of the Lapsus$ extortion gang, with Microsoft being only minimally affected, while hundreds of Okta customers were adversely affected by the breach.
- A new MacOS malware called Gimmick has been discovered being used by the Chinese APT group Storm Cloud.
- Attackers claim to have breached TransUnion South Africa with 'Password' password and stolen 4TB of data.
- Italian railway operator Trenitalia has had its ticket sales and internal applications disrupted by a ransomware attack, in which the attacker has demanded a 5 million USD ransom that will double to 10 million USD after three days.
- Threat actors are abusing the popular Chocolatey Windows package manager in a new phishing campaign to install new 'Serpent' backdoor malware on systems of French government agencies and large construction firms.
Why did Acronis Cyber Backup become a part of Acronis Cyber Protect
As Acronis has evolved from a backup and disaster recovery software provider to a data protection software provider, it was obvious that Acronis needed to offer its customers a richer set of features integrated into one solution to ensure that their systems, applications and data are protected from any event, including cyberattacks. This is why Acronis combined the backup capabilities of Acronis Cyber Backup into Acronis Cyber Protect.
Features of Acronis Cyber Backup
The following features that were supported by Acronis Cyber Backup are now incorporated into Acronis Cyber Protect:
- File and disk-image backup
- Continuous data protection
- Flexible backup and storage options
- Acronis Universal Restore, which provides the ability to restore to bare-metal physical, virtual or cloud environments
- Any-to-any migration
- Acronis Instant Restore, which reduces recovery times and provides best-in-industry recovery time objectives (RTOs)
- Variable block-size duplication to minimize storage space
- Drive health monitoring
- Support for 20+ platforms
The evolution of legacy backup
Even in the early days before the printing press and computers, learned people were concerned about preserving copies of important scrolls, manuscripts and books. To ensure that the history, stories and intelligence captured in early documents survived, scribes, theologians and record-keepers spent their lives manually copying important texts. And this kind of “backup” has come a long way since the introduction of computers. Here is a short history of its evolution.
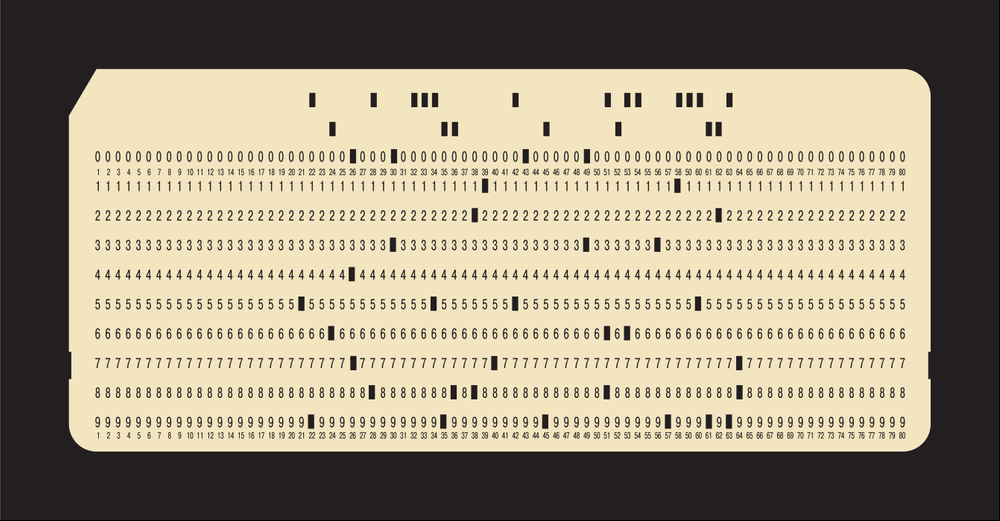
Punch cards
Initially, computers used punch cards to back up computer commands. In fact, punch cards were first used in the 1880 census to compile census data. This technology survived until the late 1980s. At that point, punch cards were replaced by more cost-efficient magnetic disk storage.
Magnetic disk and tape
Magnetic drums were first used in World War II by the U.S. Navy, but this technology was followed and replaced by magnetic tapes. One roll of magnetic tape could store as much data as 10,000 punch cards. And it was able to be rewritten so you could rewrite new data over old data. This transformed the way data was backed up and businesses both large and small were using magnetic tape for backups.
One shortcoming of magnetic tape was that information had to be stored sequentially, making it very difficult to recover specific files. You had to find the exact spot on the tape where the files were located in order to retrieve them.
Floppy disks, CDs, DVDs
Forty years after magnetic tape was first invented, floppy disks came on the scene, followed shortly thereafter by CDs, SD cards, CD Roms, and DVDs in the 1990s. This media became very popular because users could easily share data from computer to computer. However, one thing this medium had in common with its predecessors was that the backups were stored in the same place as the computers, taking up a lot of physical storage space and increasing the risk of data loss in the event a disaster impacted the business facility or IT data center.

Hard drives
Hard drives were first introduced in the mid 1960s, but were not perfected until 30 years later. Today, at-home users and businesses use hard drives for storage backup; but with the advent of big data, hard drives were expensive to scale up. Businesses also had to maintain the hard drives off-site in the event of a disaster.
The cloud
Finally, cloud technology was introduced in the 2000s, which again revolutionized data backup. The cloud offers off-site storage, is cost effective, can easily scale up to meet the demands of explosive data growth, and allows users to access data from anywhere, anytime.
Integration of backup and cybersecurity
With the advancement of cloud technology and volume of cyberthreats continuously growing and impacting businesses, modern backup software providers, like Acronis, realized that they needed to do more to protect their customers’ data. While backup and disaster recovery continue to be critical to ensure business continuity, Acronis enhanced their solutions with cybersecurity features to detect and stop cyberthreats including malware, phishing emails, ransomware attacks, etc., and enable businesses to provide complete cyber protection in a constantly evolving threat landscape.
The bottom line: Acronis integrated the features of Acronis Cyber Backup into a single solution that combines backup, disaster recovery and cybersecurity — Acronis Cyber Protect!
Backup is not enough — Your business needs a complete cyber protection solution
IT managers are often frustrated by the effort it takes to keep corporate data safe. Acronis Cyber Protect eliminates the need to manage multiple costly and complicated solutions and enables you to deliver better protection with less effort.
Acronis Cyber Protect integrates best-of-breed backup, advanced anti-malware and endpoint protection management into a single solution. Integration and automation provide unmatched protection ― increasing productivity while decreasing TCO. The solution offers one agent, one management interface, one license ― removing complexity and risks associated with non-integrated solutions.
The integration of multiple protection technologies into one solution not only increases reliability ― it also decreases the time required to learn, deploy and maintain solutions. With Acronis Cyber Protect, you get one integrated solution that delivers complete protection from today’s threats ― helping you to streamline management, cut unnecessary administrative time and lower your total cost of ownership (TCO).
Acronis Cyber Protect provides businesses with:
- Business cybersecurity and endpoint protection management, vulnerability assessments and patch management, remote desktop, and drive health
- Full-stack, next-generation machine intelligence (MI)-based protection against malware, including URL filtering and automated backup scanning
- Fast and reliable recovery of your apps, systems, and data on any device, from any incident
Acronis Cyber Protect has been awarded for its 100% detection rate; 0% false positives; and 100% high performance (VB100, AV-TEST, AV-Comparatives).
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.



