Ransomware is very profitable for cybercriminals. The FBI estimates that the Sodinokibi group made around $1 million per month last year. The criminals behind Ryuk made even more: up to $3 million per month at the beginning. It’s not surprising, then, that ransomware activity is highly prevalent and many CISOs rate it as one of their top five risk scenarios.
The Acronis Cyber Protection Operation Center (CPOC) noticed a recent spike in globally blocked ransomware attacks: 20% in the second half of May. The activity has since dropped, but in June it remains elevated.
Initial access
Despite the constant menace, the methods of these criminals have changed slightly over the years, since defense methods have adapted. Targeted ransomware is still primarily distributed through spear-phishing emails. But especially now, with the increase of working from home, we have seen a growing interest in scanning for exposed and poorly secured services such as RDP and VPN servers. With the increase in ransomware-as-a-service offerings, we have also seen an increase in paid drops being used to gain initial access to corporate networks.
In addition, recent years have seen many attacks directed toward service providers as a kind of supply chain attack. Having access to the cloud infrastructure (or at least the consoles) of a service provider can multiply the reach for the attacker. Having access to such web consoles, including the ones from security and backup services can of course make the life of the attacker very easy. Misusing that access, they can try to disable security tools, delete backups, and even deploy their malware into the organization. That’s why it is vital to secure all service accounts with strong multi-factor authentication. For example, set up 2FA for all Acronis Cyber Protect Cloud accounts.
Lateral movement
When cybercriminals gain a foothold inside an organization they’ll often manually expand their influence with common tactics. The attackers adapt to whatever situation and resistance they encounter. Living-off-the-land techniques such as PowerShell, WMI, and PsExec are still popular choices, but some groups also make use of Cobalt Strike and other tools. Some groups attempt to attack password managers. Ragnar recently deployed a full VirtualBox image to hide its presence. The lateral spreading still mostly relies on privilege escalation or stolen passwords. Tools like Mimikatz and Bloodhound & Co. are utilized in the hunt for domain admin credentials. The actual ransomware payload is often deployed very late in the process.
Data exfiltration
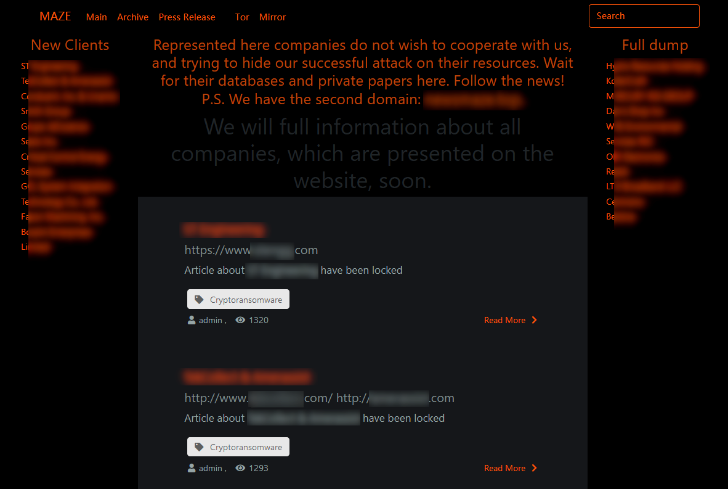
Since many companies have a working disaster recovery plan and don’t worry about losing their encrypted data much, attackers are increasingly shifting their focus towards stealing data. This move was pioneered by the Maze group in 2019, although other groups have stolen data before. Now many groups have followed, including Sodinokibi, Netfilm, Nemty, Netwalker, Ragnar, Psya, DoppelPaymer, CLOP, AKO, and Sekhmet.
The attackers sometimes exfiltrate tens of terabytes of data, which could be identified by the network monitoring team, if they’re looking. Often simple tools such as FTP, Putty, WinSCP, or PowerShell scripts are used to exfiltrate the data. In order to bypass DLP or network monitoring, encryption might be applied, like compressing the data in a password-protected archive before transferring. The attackers search for sensitive data and aren’t really interested in holiday photos, but rather go for financial documents, contracts, customer records, and legal documents. Anything that could inflict damage to the victim and would motivate them to pay the ransom demand. In particular leaked customer records could lead to privacy regulatory fines for the victim company, not to mention bad press and brand reputation damage.
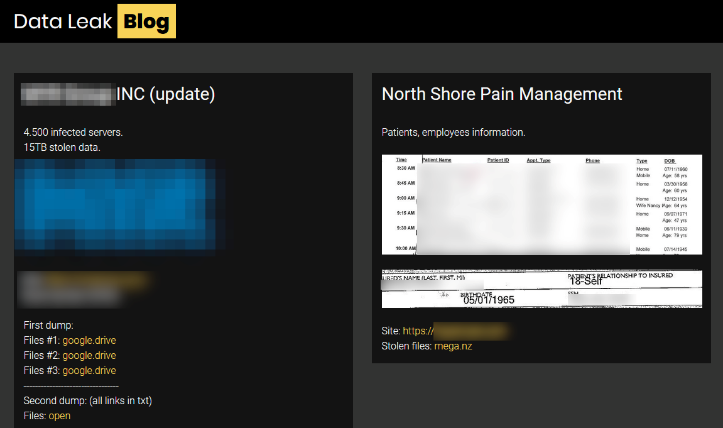
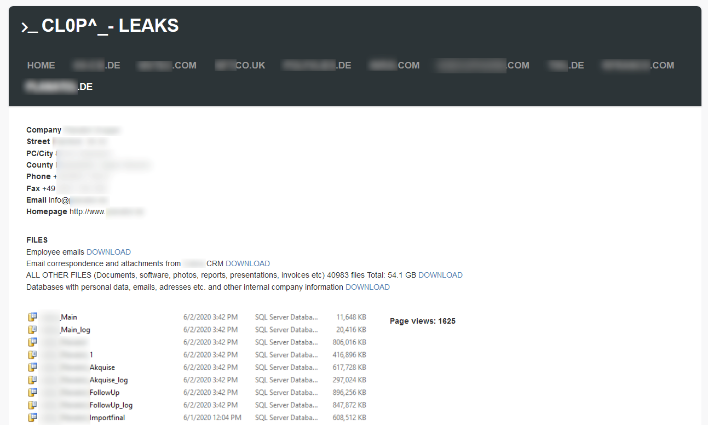
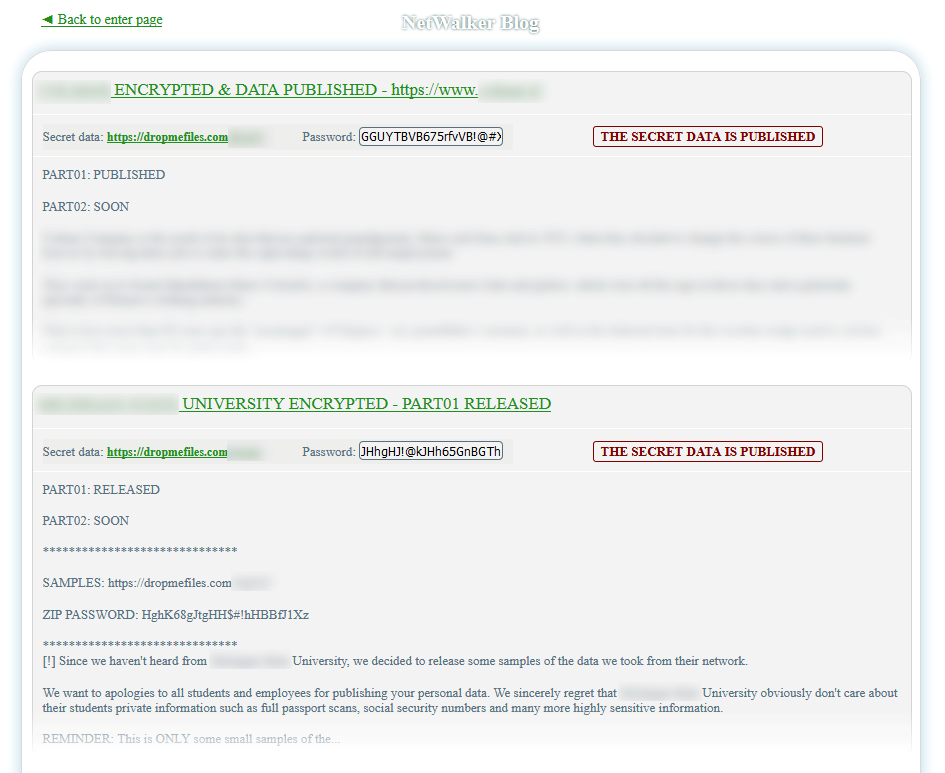
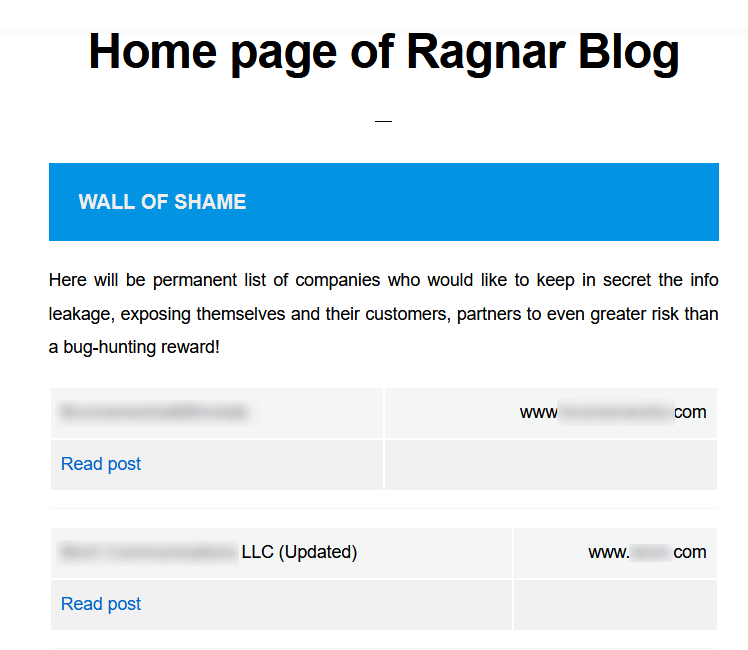
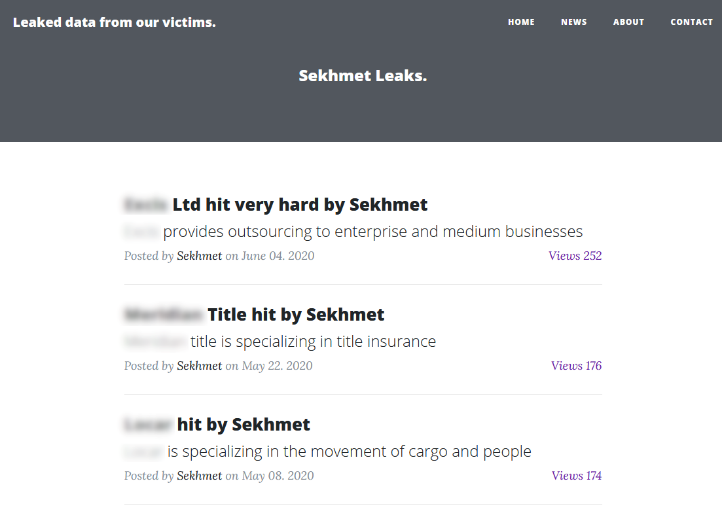
Attackers will then often release a few documents as a small teaser to prove that they do have the data. Some groups even publish the full data dumps on their website after the ultimatum expires. In order to expand the reach of these dumps, many leak sites have appeared in recent months, mostly on the TOR network. Some groups try to sell the data on underground sites as a way of making a profit. The Sodinokibi group recently introduced a public auction platform where they apparently sell the data to the highest bidder. The bidding starts at $50-100K depending on the available data. For example, 10,000 documents with cash-flow analysis, business distribution data, and scanned driver's licenses are available for $100,000. For a starting price of $50,000 they offer more than 20,000 documents and three databases full of accounting files and customer records. The leak sites vary from simple designs to more complex structures. All with the aim to directly or indirectly generate profit for the attackers. Over time these sites might get developed further if the business model pays out for the attackers.
Examples of data leak sites that are active today include:
Protection
In the past, there have been a handful of incidents where ransomware was used more as a diversion to distract from another attacker or to cover the tracks of an APT attack. But the majority of cases are all about making profits from your data. We can see a clear shift towards classic data breach attacks, away from encrypting all servers.
No matter what motive the attackers have, it’s clear that the era where backup alone was enough protection against ransomware attacks is long gone. Of course, you should still have a working backup and a tested disaster recovery plan – just like you wouldn’t remove the seat belts in your car either – but you need additional security measures in order to be fully protected. That said, each ransomware attack should be treated as a data breach investigation at the start.
Our Acronis Cyber Protect solution can proactively block any ransomware attack with its machine-learning-assisted heuristics and any files that were modified during any attack are immediately restored by the solution. In addition, its behavior-based detection engine blocks threats from propagating inside the corporate network, regardless of if they use fileless techniques or classic malware. The vulnerability assessment and patch management capabilities of Acronis Cyber Protect allow you to ensure that all your workloads are always up-to-date, in order to minimize the attack surfaces. Providing protection across multiple levels all from within one console.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 60+ countries. Acronis Cyber Platform is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.



