When it comes to backing up your data, you want to be in control. Most of us have heard that data can be leaked, accidentally or not, or unlawfully obtained by criminals that want to exploit it for their criminal purposes.
We at Acronis understand that you may and most likely have this concern, which is why we give you all the controls in hand and can assure you that our infrastructure for your data is very secure. Even if data is intercepted, we use mechanisms to render such attempts useless. This is mainly achieved using encryption.
What are 3 types of data security?
We live in a digital era where information effortlessly flows through networks and systems, so ensuring data security has become extremely important. The interconnected nature of our world brings both opportunities and risks, making it essential to safeguard information from threats like unauthorized access, cyberattacks, and data breaches. This article explores the three aspects of data security: hardware security, software security, and legal security. Together, these aspects form a defense strategy to protect data in our evolving technological environment.
- Hardware Security: Strengthening the Foundation
At the heart of any data security strategy is hardware security. It focuses on protecting the infrastructure that stores and processes sensitive data. While digital solutions often grab attention, securing the components is equally significant. Security protocols integrated into hardware components like servers, routers, and storage devices play a role in preventing unauthorized access and data breaches.
Data encryption is one of the methods used in hardware security. By encrypting data when its stored or transmitted, organizations can ensure that even if a breach occurs, stolen information remains incomprehensible to third parties. Encrypted data acts as a fortress, providing a layer of protection against potential threats.
Hardware based encryption solutions offer a layer of security by using chips to handle encryption processes, thus minimizing the impact on overall system performance.
- Software Security: Protecting Digital Assets
In addition to hardware security, software security acts as a shield to safeguard information from virtual threats. The software layer includes operating systems, applications, and security software that work together to detect and mitigate data breaches. Implementing security protocols in software helps identify vulnerabilities and potential exploits, reducing the risk of access.
Data security solutions like firewalls, intrusion detection systems, and antivirus software play a key role in establishing a defense against cyberattacks. These solutions monitor network traffic, detect activities, and prevent cybercriminals from accessing sensitive data. Additionally, regular software updates and patch management ensure the resolution of vulnerabilities, minimizing the risk of exploitation by malicious software.
- Legal Security: Navigating Regulatory Requirements
Nowadays, where privacy concerns are on the rise, legal security has become essential for protecting data. Regulatory frameworks, such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) impose obligations on organizations that handle information. Failing to comply with these rules can lead to consequences, highlighting the significance of ensuring protection in any data security plan.
Legal protection involves understanding and following laws related to data privacy as well as establishing comprehensive policies for managing data. These policies govern how sensitive information is collected, processed, and shared, guaranteeing the rights of individuals whose data is involved. Moreover, legal protection includes creating procedures for reporting data breaches and promptly informing the affected sides. This promotes transparency and accountability.
In today's world, safeguarding information requires an approach that covers hardware security, software security, and legal compliance. By implementing security measures, encrypting data, and adhering to legal obligations, organizations can develop a defense strategy that safeguards their most valuable asset, their information. As technology continues to advance, it remains crucial for businesses to remain vigilant and proactive in their approach to data security in order to build and maintain trust in an interconnected society.

The Importance of data security
In the evolving world we live in, safeguarding your data has become more crucial than ever before. With both businesses and individuals creating and exchanging a volume of information, it is imperative to prioritize its security. From protecting sensitive personal information to securing valuable corporate data, data security plays a pivotal role in maintaining trust, integrity, and continuity in a world driven by information.
Data security is not merely a buzzword, it stands as a cornerstone of responsible data management. With cyber threats evolving at an alarming rate, having a robust data security strategy in place is essential to safeguard against potential breaches and attacks. Organizations must be prepared to detect unknown attacks and vulnerabilities, ensuring that their systems and networks remain resilient even in the face of the most sophisticated threats.
One of the key techniques employed in data security is data masking. Data masking involves disguising original data with fictional, yet realistic, information. This technique serves a dual purpose: protecting sensitive data while allowing applications to function as usual. By employing data masking, organizations can confidently share their data with trusted partners or third parties without the risk of exposing critical information.
Securing data within an organization goes beyond mere protection against external threats. It encompasses controlling and regulating who has access to data within the organization itself. Managing user permissions, restricting unauthorized personnel from accessing data, and implementing stringent access controls are fundamental steps in ensuring that an organization's data remains secure from within.
Database security, a subset of data security, focuses specifically on safeguarding the integrity and availability of databases. This includes implementing authentication mechanisms, encryption, and auditing procedures to ensure that data stored within various databases is protected against unauthorized access and manipulation.
Data security risks are multifaceted and can lead to dire consequences if left unaddressed. From financial losses to reputational damage, the fallout from a data breach can be devastating. A strong data security policy is the backbone of risk mitigation. Such policies outline guidelines and protocols for data handling, storage, and access, ensuring that every member of the organization understands their role in upholding data security.
Data loss is a nightmare scenario that organizations strive to avoid. Once data is lost, it can lead to irreversible setbacks and even business closures. Implementing robust data security measures, including regular data backups and disaster recovery plans, can provide a safety net against data loss events, allowing organizations to quickly recover and resume operations.
Data security is not just a technicality, it is the linchpin that holds together modern information-driven ecosystems. From protecting sensitive customer information to securing a company's proprietary data, for sure this leads to the conclusion that data security is crucial for maintaining trust, ensuring compliance, and mitigating risks. As cyber threats continue to evolve, organizations must prioritize data security, adopting comprehensive strategies that encompass detecting unknown attacks, employing data masking techniques, and adhering to stringent data security policies. By doing so, organizations can fortify their digital presence and navigate the intricate landscape of the digital age with confidence and resilience.
Data security important benefits
The threat of data theft is ever present in today's reality. Malicious attacks with intent are constantly seeking opportunities to infiltrate systems and steal information for their own benefit. Implementing data security strategies effectively mitigates the risks associated with thefts. By implementing practices like encryption, organizations can render stolen data useless to individuals and ensure the protection of sensitive information even in the event of data breach.
At the forefront, data security is important for the prevention of data loss. In an era where data is often considered the lifeblood of organizations, losing valuable information can be catastrophic. Data loss prevention mechanisms, integrated into comprehensive data security frameworks, act as a safety net against accidental deletions, hardware failures, or other unforeseen incidents that could potentially lead to irreplaceable data disappearing forever.
The specter of data theft looms large in today's digital landscape. Malicious actors with ill intentions continuously seek opportunities to infiltrate systems and steal data for their personal gain. Implementing stringent data security strategies effectively mitigates the risks associated with data theft. By employing best practices, such as encryption, organizations can render stolen data useless to unauthorized individuals, safeguarding sensitive information even in the event of a breach.
Secure data, in essence, translates to peace of mind for individuals and businesses alike. Knowing that robust data security measures are in place alleviates concerns about unauthorized access and potential data breaches. Employees, customers, and partners can trust that their valuable data is protected, fostering a sense of confidence and loyalty in the organization.
One of the best practices in data security is controlling access to sensitive data. By implementing strict access controls and authorization mechanisms, organizations ensure that only authorized personnel can access valuable data. Multi-factor authentication adds an extra layer of security, requiring users to provide multiple forms of verification before gaining access, further reducing the risk of unauthorized access to sensitive data.
A company's security policies play a role in establishing a foundation for data security. Defined and consistently enforced security policies set expectations for employees and stakeholders regarding how they handle, access, and protect sensitive information. These policies guide employees in making decisions, ensuring that data security remains a priority across all levels of the organization.
Data security strategies encompass a range of techniques and practices that work together harmoniously to create a defense, against threats. By adopting these strategies, organizations can proactively identify vulnerabilities, address weaknesses, and stay ahead in an evolving digital landscape.
The benefits of prioritizing data security extend beyond technology related aspects. Ensuring the security of your data is crucial in order to avoid data loss, prevent data theft, and build trust with stakeholders in an organization.
To establish a foundation for data security, it is important to follow best practices like managing data access and implementing multi factor authentication. By integrating these strategies into an organization's security framework and consistently upholding company policies, businesses can safeguard data, inspire confidence, and successfully navigate the era.
Is data security same as cyber security?
The significance of safeguarding data cannot be overstated. In our digital world, where individuals and businesses generate, share, and store large amounts of data, the need to protect it from various cyber threats becomes a top priority. While terms like "data security" and "cyber security" are often used interchangeably, they hold different meanings. Let's explore these concepts in depth to understand the nuances that set them apart.
At first glance, data security and cyber security might appear synonymous, as both aim to protect assets from breaches. However, they encompass aspects within the realm of information technology.
Data security primarily focuses on safeguarding the organization's data itself, including information, intellectual property rights, and sensitive records that form the foundation of any organization. It involves implementing measures to control and restrict access to this data, ensuring that only authorized individuals can gain access.
Techniques, such as data discovery and classification help identify information, such as personally identifiable details (PII), enabling organizations to implement appropriate security measures. Access control mechanisms and encryption plays a key role in data security by allowing authorized parties to interact with the data while ensuring its protection even if intercepted.
However, it's important to note that cyber security encompasses a wider scope than data security. It involves protecting systems, networks, and digital assets from a variety of threats. While data security focuses on safeguarding the information itself, cyber security is concerned with creating a safety and protected environment for that data. This includes measures to defend against cyberattacks, malware, viruses, and other malicious activities that can compromise the integrity, availability, and confidentiality of systems.
A great example of a solution within the realm of cyber security is Cloud Access Security Brokers (CASBs). CASBs provide visibility and control over data as it moves between an organizations on premises infrastructure and cloud services. By enforcing security policies and monitoring cloud based activities, CASBs help prevent access and data leakage.
Insider threats are concerns in both data security and cyber security. These refer to the risks posed by individuals within an organization who have access to information. Effective strategies for data security include measures to detect and prevent insider threats, ensuring that employees with access do not misuse or leak data.
Key management and software testing play major roles in both data security and cyber security well. Key management ensures the generation, distribution, and storage of encryption keys to enhance data protection.
Rigorous testing of software is pivotal in identifying vulnerabilities and weaknesses that could potentially be exploited by cybercriminals. This helps ensure that unauthorized access to systems and data is prevented.
To conclude, while both data security and cyber security share goals and principles, they focus on aspects of information protection. Data security primarily involves safeguarding the data itself using techniques like access control and encryption. On the other hand, cyber security encompasses a range of measures aimed at protecting systems, networks, and digital assets from various types of cyber threats. Both are essential for maintaining the integrity, availability, and confidentiality of information while creating a protected digital environment for individuals and organizations.
What are the 4 key issues in data security?
Protecting sensitive data from a myriad of threats has become a critical imperative, shaping the way businesses operate and individuals interact online. Among the multifaceted landscape of data security, four key issues stand out as pivotal challenges that demand careful consideration and proactive measures. Let's delve into these issues and uncover their significance in maintaining the integrity and confidentiality of valuable data.
- Accidental Exposure: In the fast-paced world of digital communication and collaboration, accidental exposure of sensitive data is a prevalent concern. Human error, often stemming from an unintentional click or oversight, can lead to the unintended sharing of confidential information. Such incidents not only compromise data integrity, but can also result in legal and regulatory ramifications. Addressing accidental exposure requires a combination of robust access management, employee training, and data classification practices to ensure that individuals are aware of the sensitivity of the information they handle and how to manage it securely.
- Phishing and Other Social Engineering Attacks: Cybercriminals have perfected the art of manipulating human psychology through tactics like phishing and social engineering attacks. These techniques trick individuals into divulging sensitive information or granting unauthorized access to systems and networks. Phishing emails, for example, often appear legitimate and can easily deceive unsuspecting users. Combating these threats necessitates not only technical measures but also comprehensive education and awareness campaigns. Teaching individuals to recognize red flags and fostering a culture of skepticism is crucial to thwarting these deceptive attacks.
- Insider Threats: The specter of insider threats looms large in the realm of data security. While external threats often grab the headlines, individuals within an organization with privileged access can pose a significant risk. Insiders, whether intentionally or unintentionally, may misuse their access to gain unauthorized entry or expose sensitive data. Privileged access management (PAM) solutions play a pivotal role in mitigating this risk by closely monitoring and controlling the activities of privileged users. Effective PAM ensures that access is granted only on a need-to-know basis, reducing the likelihood of internal breaches.
- Ransomware: Ransomware attacks have become a pervasive and damaging threat to data security. In a ransomware attack, cybercriminals gain access to a victim's systems and encrypt their data, demanding payment for its release. Organizations are then faced with a difficult choice to pay the ransom or risk losing valuable data. Preventing ransomware requires a combination of robust access management, data backup strategies, and security patches. Regular data backups, stored in secure and isolated locations, can serve as a lifeline, enabling organizations to restore their data and operations in the event of an attack.
The process of securing data is complex and ever-evolving. Accidental exposure, phishing attacks, insider threats, and ransomware are four key issues that demand attention and proactive measures. A comprehensive data security strategy should encompass elements of access management, data classification, employee training, privileged access management, data backup, and more. By addressing these challenges head-on, organizations can navigate the digital realm with confidence, safeguard sensitive information, and maintain trust in an age where data security is paramount.
How do you ensure data security?
The prevalence of data breaches and cyber threats underscores the critical need to safeguard sensitive information from unauthorized access and potential misuse. Employing robust data security measures is not only a matter of compliance, but also a means of upholding trust, safeguarding reputation, and maintaining operational integrity. Let's explore the key strategies and best practices to ensure data security in a rapidly evolving digital landscape.
1. Access Control and Authorization: Effective access control lies at the heart of data security. Organizations must meticulously manage and restrict access to data warehouses and other repositories, ensuring that only authorized users can interact with sensitive information. Implementing the principle of least privilege, which grants individuals the minimal access necessary for their roles, minimizes the risk of data exposure or unauthorized manipulation of sensitive data. Robust authentication methods, such as multi-factor authentication, further bolster access control and prevent unauthorized entry.
2. Data Classification and Encryption: Structured data, including personally identifiable information (PII), demands special attention. Employing data classification frameworks allows organizations to categorize data based on its level of sensitivity. By identifying sensitive data, organizations can apply appropriate encryption measures to protect it from unauthorized access, both within and beyond data warehouses. Encryption ensures that even if data is breached, it remains indecipherable to unauthorized parties.
3. Cloud Security and Mobile Devices: As data storage and processing increasingly migrate to the cloud, cloud security becomes a crucial aspect of data protection. Cloud service providers offer advanced security measures, but organizations must also take responsibility for securing their data within the cloud environment. Additionally, the widespread use of personal and mobile devices requires organizations to establish stringent security protocols to prevent data exposure or breaches through these personal devices.
4. Physical Access and Security Audits: Physical access to data warehouses or storage facilities is another vector of concern. Organizations should establish stringent physical security measures to prevent unauthorized personnel from gaining access to critical data repositories. Regular security audits and assessments ensure that data security measures remain effective and up to date, identifying potential vulnerabilities before they can be exploited.
5. Employee Training and Insider Threats: Many data breaches are caused by non-malicious human error that results in the exposure of sensitive data or information. Employee training programs should emphasize the importance of data security, educating staff about best practices, recognize phishing attempts, and understand the implications of data breaches. Establishing a culture of vigilance and accountability among employees can significantly mitigate the risk of inadvertent data exposure or unauthorized access.
6. Data Privacy Regulations and Compliance: Data privacy regulations, such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), impose stringent requirements on data protection. Adhering to these regulations not only ensures legal compliance but also sets a strong foundation for data security practices. Organizations must familiarize themselves with the specific requirements of these regulations and implement the necessary measures to safeguard data privacy.
7. Data Analysis and Deletion: The lifecycle of data should be carefully managed. Unnecessary retention of data increases the risk of exposure. Regularly analyzing data usage patterns and deleting data that no longer serves a purpose reduces the potential attack surface. Data deletion should be carried out following proper protocols to prevent data recovery.
In summary, ensuring data security is a multifaceted endeavor that requires a combination of technical measures, stringent protocols, and a vigilant organizational culture. By implementing access control, encryption, cloud security solutions, and physical security measures, organizations can protect sensitive information from unauthorized access and potential breaches.
Employee training, compliance with data privacy regulations, and data analysis further contribute to a comprehensive data security strategy. In the digital realm where the risk of data breaches looms large, prioritizing data security is not only prudent but essential for maintaining trust, safeguarding reputation, and thriving in a data-driven world.
Encrypt everything
You may have heard of encryption in relation to your other devices or web-related activities. For example, https allows access to sensitive websites, like when you access your email or your bank website. Encryption is one of the founding pillars of data security. However, it needs to be applied properly, with all data-protection scenarios in mind.
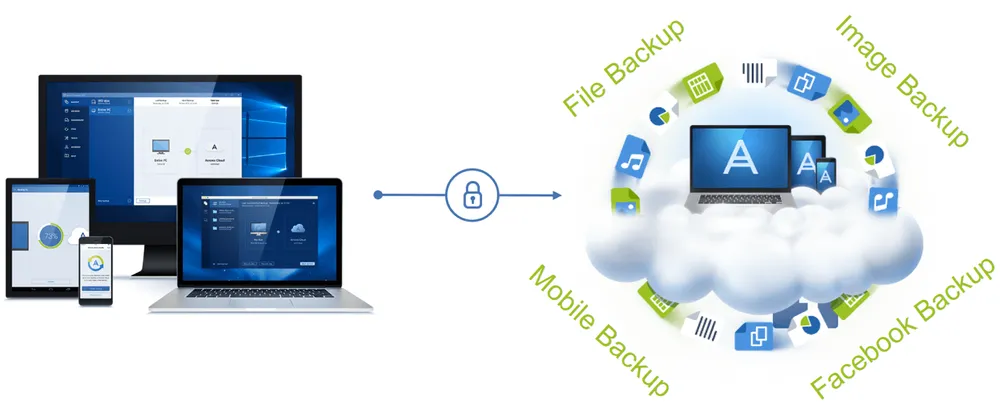
All types of data backups are secured and protected with Acronis True Image!
First, we need to be sure that local backups can be secured from unauthorized access in case someone gains access to your desktop, laptop, or mobile device. By using the industry-grade AES-256 algorithm, you can be sure that your data is safe. It is very hard to decrypt data secured by this algorithm. AES-256 is not that fast in terms of time and performance during the encryption process, so you may consider using shorter key lengths (AES-256 means that the encryption key length is 256 bits), like 128 or 192 bits, in order to improve performance when protecting data that is not that sensitive.
Users can set the encryption algorithm and password that are used for encryption, and the Acronis agent handles key creation. The password and decryption key you assign for backup can't be retrieved, so you need to memorize them. This is actually done on purpose, as this is a proper security approach. In case of a targeted or malware attack, your password won't be found in the agent or program files, and thus there will be no way to decrypt the backup file(s).
Technologically, the password is also converted through an algorithm into the actual encryption key, so it's really secure. You, of course, can set different passwords for each backup plan (that means that each backup will be encrypted using a different encryption key).
Secondly, the same goes for cloud storage: you better store backups in an encrypted format. Some of us are cautious about our data being stored in the cloud somewhere. There is still an issue of trust, especially after some major security breaches in recent years, like with PSN or iCloud. We at Acronis understand that this is why we give our users an option to store data on the Acronis Cloud in encrypted form. To encrypt and decrypt your data, the program needs the password that you specify when you configure the online backup. The process and approach is the same as with a local backup – you need to memorize your password. Alternatively, you can use password manager software, which will do it for you.
Thirdly, what else do we need to backup and care about? Facebook, our online social life. That is why we recently added the option of Facebook backup encryption as well. This backup can be located in the cloud, but we can encrypt data on the fly during backup creation, thus minimizing any possible data breach.
Ensure that your data goes to secured cloud storage, via a secure channel
We have already covered that all data needs to be encrypted, no matter where it is stored – locally or in the cloud. But it's also very important to eliminate the chance of data interception on its way to the cloud. This means that the channel to the cloud needs to be secured via SSL, which is how Acronis products talk to Acronis Cloud.
Acronis Cloud, on the other hand, consists of many data centers distributed across the globe, and they are very well secured against various types of attacks. Physical security is ensured via high fences, 24/7 security personnel, and video surveillance with ninety-day archiving. Biometric scans and a proximity key card are required for access. Acronis data centers are equipped with UPS and backup diesel generators and are designed to ensure constant power availability for up to forty-eight hours to sustain an undefined power outage. In addition, there are redundant HVAC, network, and UPS systems. The Tier-IV data centers do not interrupt availability for any planned activity and can sustain at least one worst-case scenario unplanned event and experience no critical impact. With over ninety-nine percent availability, Tier-IV is the highest availability level for any data center on the planet.
Acronis data centers are also SSAE 18 certified. SSAE 18 is a framework for a data center organization to have an outside entity examine their internal controls. Compliance-sensitive companies, such as publicly traded enterprises, financial firms, and healthcare organizations, often require SSAE 18 certification.
Acronis helps you control access to your data
In summary, with Acronis products, you can be sure that your data won't be accessed by someone who shouldn't have access to it. You can encrypt data on the device and send it in encrypted form to the cloud by using a secured, encrypted channel. This data in the cloud will be additionally secured through a strict data center security policy.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.



