Acronis Cyber Protect v16 helps reduce the total cost of ownership (TCO) for cyber protection solutions through several key features:
• Comprehensive Workload Support: With support for over 20 different workloads, including on-premises, cloud, and SaaS platforms, Acronis Cyber Protect v16 allows enterprises to streamline their data protection efforts across diverse IT environments. This extensive support facilitates vendor consolidation, simplifying management, and ensuring that all aspects of the enterprise IT infrastructure are comprehensively protected.
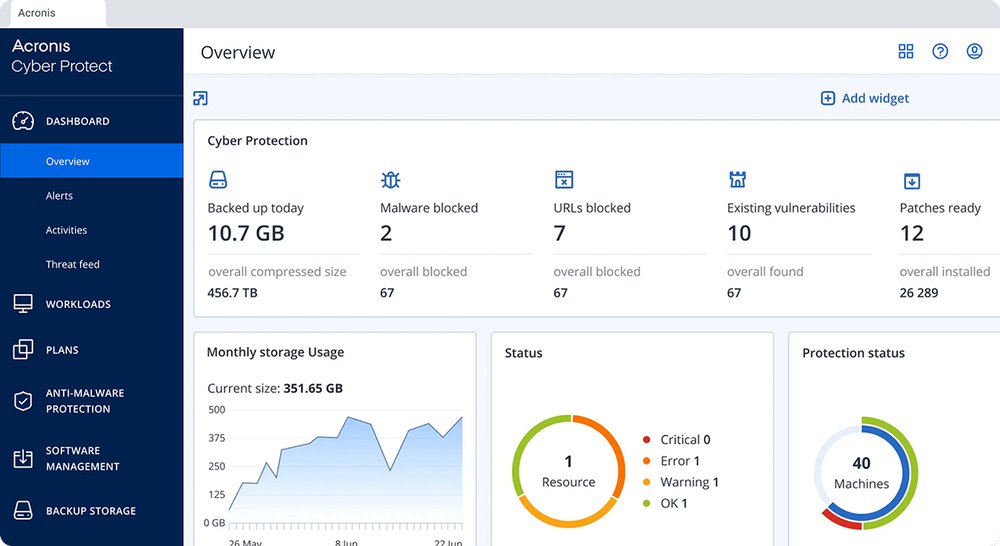
• Streamlined Management: The centralized management console simplifies the oversight of data protection and cybersecurity across the enterprise, thereby saving administrative time and reducing operational costs.• One-click Recovery: The one-click recovery feature empowers users to restore systems independently, reducing the burden on IT staff and minimizing downtime, which can be costly for businesses.
• Automated Processes: With automated features like patch management and vulnerability assessments, routine tasks are handled efficiently, allowing IT teams to focus on more strategic initiatives rather than time-consuming maintenance.
• Resource Efficiency: Acronis Cyber Protect v16 is designed to minimize the impact on system resources, ensuring that protection operations don't interfere with productivity and do not require additional investment in hardware.
• Proactive Protection: Advanced AI and ML technologies help prevent cyber incidents before they occur, reducing the potential costs associated with data breaches, ransomware recovery, and system remediation.
• Compatibility with Legacy Systems: The ability to support and recover older systems with bare-metal recovery means that organizations can extend the life of their existing infrastructure without incurring costs for immediate upgrades.
• Data Sovereignty and Compliance: The built-in compliance and data sovereignty features help avoid fines and penalties associated with non-compliance, which can add up significantly for enterprises operating in multiple jurisdictions.
By focusing on these areas, Acronis Cyber Protect v16 allows enterprises to manage cyber protection more efficiently, both operationally and financially, leading to a lower TCO.