You are on United States website. Change region to view location-specific content:
Global
English
Select another region
Choose region and language
- Americas
- Asia-Pacific
- Europe, Middle East and Africa
- Worldwide
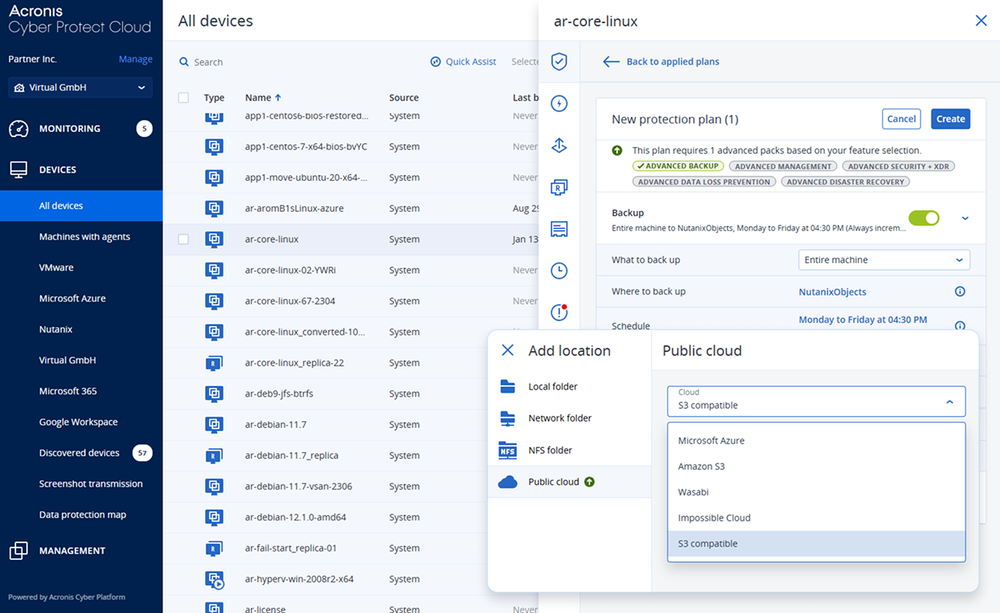
Acronis delivers a modern backup service built for MSPs. It protects every workload, integrates with security and disaster recovery, and helps you reduce downtime for every customer. All from one platform designed to simplify operations and increase recurring revenue.
Acronis Cyber Protect Cloud helps MSPs offer more value with less operational effort
For MSPs
For their end customers
Acronis Cyber Protect Cloud combines backup with security and management in a single, multi-tenant platform aligned to the NIST cyber security framework
Operational benefits for MSPs
Security and compliance aspects
With Acronis Cyber Protect Cloud, MSPs can standardize on one platform to deliver secure backup, fast recovery and broader cyber resilience services to every customer, regardless of their mix of on-prem, virtual, SaaS or public cloud workloads.

















Looking for help?
Sorry, your browser is not supported.
It seems that our new website is incompatible with your current browser's version. Don’t worry, this is easily fixed! To view our complete website, simply update your browser now or continue anyway.