Authors:
Alexander Ivanyuk — Senior Director, Technology
Irina Artioli — Cyber Protection Evangelist
Candid Wüest — VP of Product Management
The Acronis Cyberthreats Update covers current cyberthreat activity and trends, as observed by Acronis analysts and sensors. Figures presented here were gathered in November of this year and reflect threats that we detected as well as news stories from the public domain. This report represents a global outlook and is based on more than one million unique endpoints distributed around the world.

Incidents of the month
Multiple threat actors, including affiliates of the notorious LockBit ransomware group, are actively exploiting a critical security vulnerability (CVE-2023-4966) in Citrix NetScaler application delivery control (ADC) and gateway appliances. This vulnerability, known as Citrix Bleed, allows adversaries to bypass password requirements and multifactor authentication, resulting in the unauthorized takeover of legitimate user sessions. The consequences are significant, granting malicious actors elevated permissions for credential harvesting, lateral movement and unauthorized access to data and resources.
This incident reminds us of the MOVEit attacks that led to more than 2,500 compromises. It underscores the ongoing risk associated with vulnerabilities in exposed services as an entry point for ransomware attacks. A 2023 Statista survey of cybersecurity professionals across global organizations further highlights the prevalence of such risks. According to the survey, 36% of organizations fell victim to ransomware attacks due to exploited vulnerabilities.
With the holiday season upon us, the number of social engineering scams is already starting to rise again. Emails with fake promotions, malicious online shops with fake goods, sellers requesting payment through unusual payment solutions and parcel delivery-notification phishing emails, are moving up in our telemetry ranking.
November malware detections
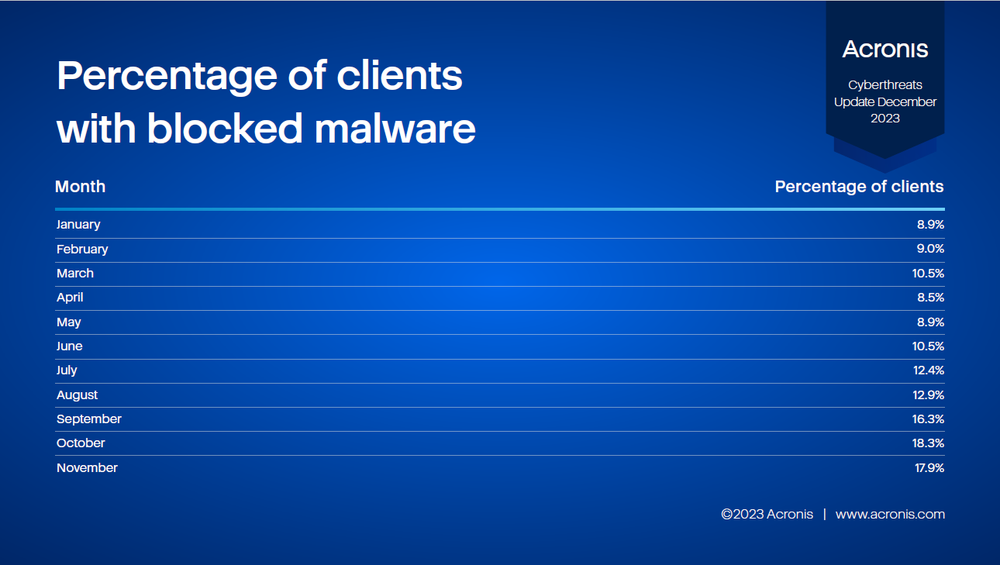
In November, Acronis blocked 1.5 million malware threats on endpoints, a decrease of 19% compared to October.
It’s important to stop malware early in the attack chain — for example, by blocking the malicious emails that deliver them. Nevertheless, many threats do still make it to the endpoint.
The following table shows the percentage of Acronis clients that had at least one malware threat blocked this month. This number has been hovering around 12% for the year so far.
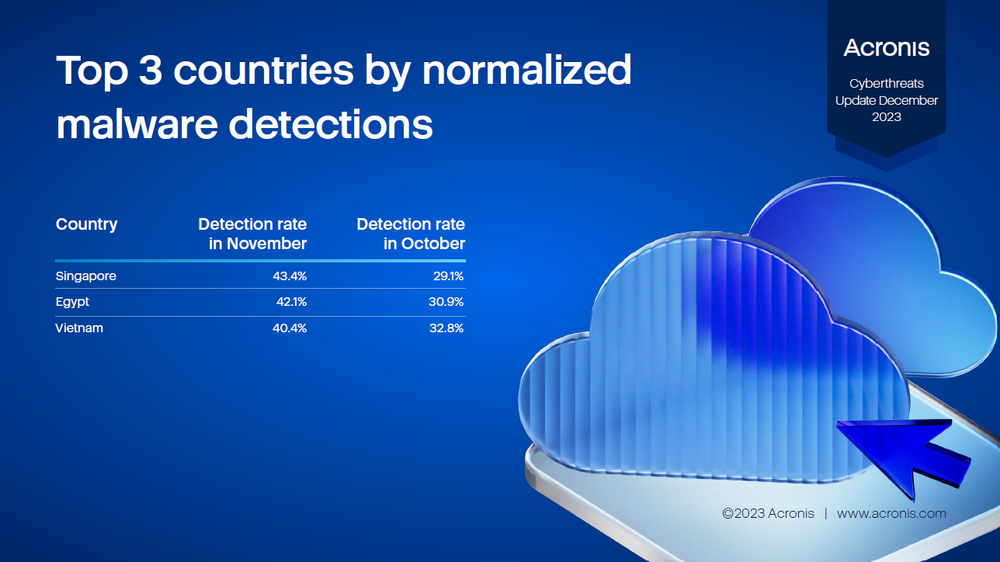
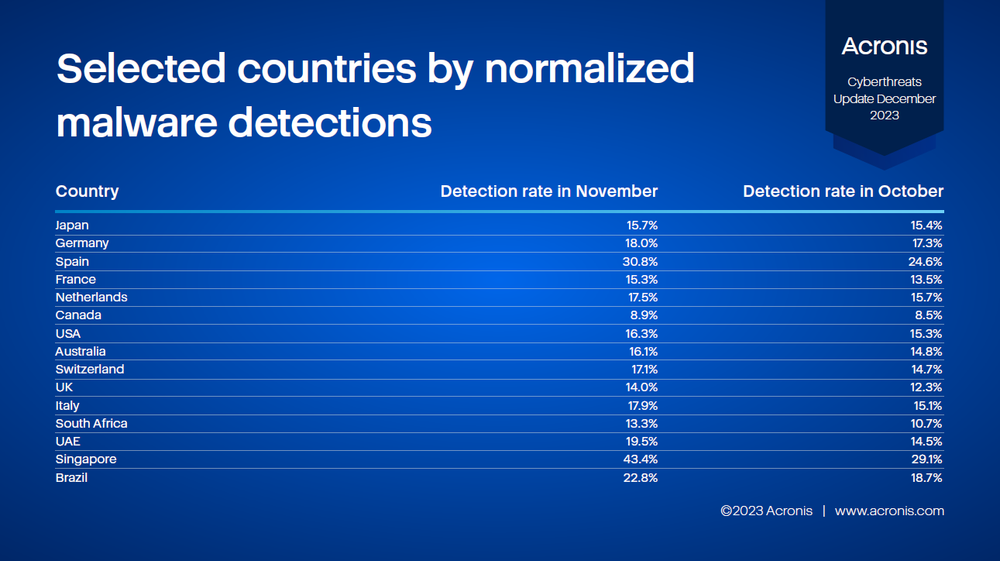
The following table shows the normalized percentage of clients with at least one malware detection in the given month. The higher the percentage, the higher the risk of a workload in that country being attacked by malware.
Protection
The aforementioned threats can be detected and mitigated with solutions from Acronis.
Acronis Cyber Protect protects against both known and never-before-seen threats through a multilayered protection approach. This includes behavior-based detection, AI/ML-trained detections and anti-ransomware heuristics, which can detect and block encryption attempts and roll back any tampered files automatically without any user interaction. Additional advanced email security and URL filtering can help you protect against the social engineering threats of the holiday season.
Advanced Security + Endpoint Detection and Response (EDR) for Acronis Cyber Protect Cloud brings the visibility needed to understand attacks, while simplifying the context for administrators and enabling efficient remediation of any threats.
Learn more about Acronis’ approach to cyber protection.