You are on United States website. Change region to view location-specific content:
Global
English
Select another region
Choose region and language
- Americas
- Asia-Pacific
- Europe, Middle East and Africa
- Worldwide
Acronis Cyber Protection Solutions deliver outstanding defense in depth (DiD) threat protection via a set of smartly integrated technologies, each of which works to prevent possible threats along dedicated stages.
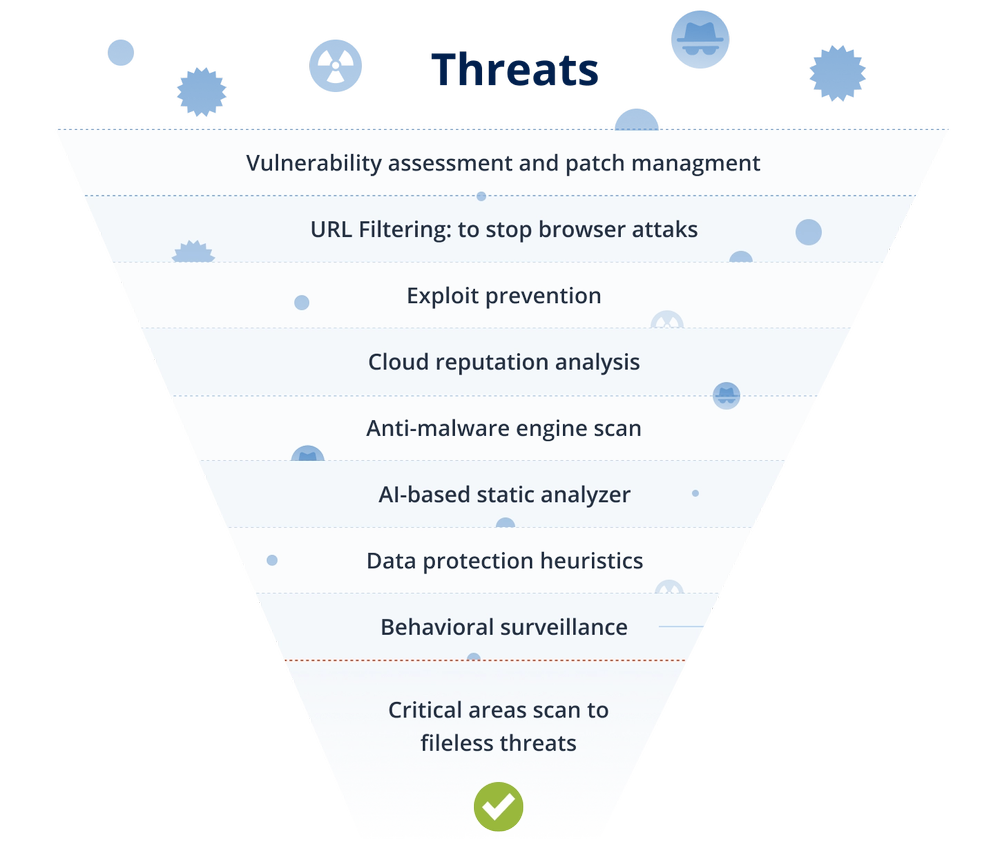
Understand how Acronis uses multiple defense layers to prevent, detect, and respond to modern cyber threats.
Sorry, your browser is not supported.
It seems that our new website is incompatible with your current browser's version. Don’t worry, this is easily fixed! To view our complete website, simply update your browser now or continue anyway.