You are on United States website. Change region to view location-specific content:
Global
English
Select another region
Choose region and language
- Americas
- Asia-Pacific
- Europe, Middle East and Africa
- Worldwide


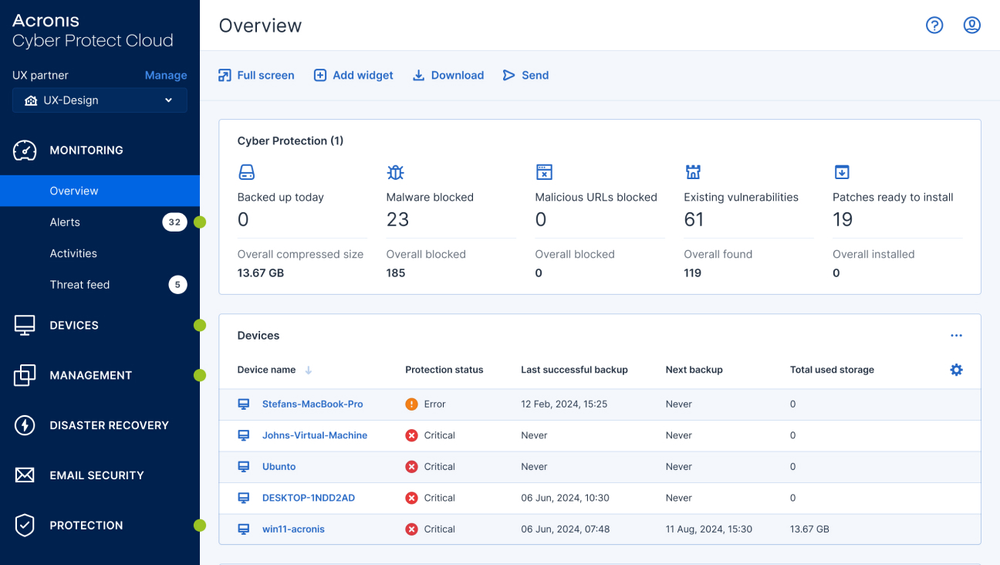
















Acronis EDR integrates with Microsoft Defender Antivirus to boost protection, reduce risk, and simplify operations for service providers. It adds AI-guided contextual analysis, detection, and automatable response — like rollback, recovery, patching, and isolation—without replacing Defender. With centralized visibility, multi-tenant management, and outsourcing options via Acronis MDR, MSPs and MSSPs can deliver enterprise-grade protection at SMB-friendly costs.
Consolidating tools and centralizing service management is easier and more accessible than ever. Expand your cybersecurity capabilities, offer complete endpoint protection and provide true business resilience for your clients and their data in the face of modern cyberthreats with Acronis EDR.
Behavior-based detection | |||
Anti-ransomware protection with automatic rollback | |||
Vulnerability assessments | |||
Device control | |||
File- and system-level backup | |||
Inventory collection (with Management) | |||
Patch management (with Management) | |||
#CyberFit Score (security posture evaluation) | |||
Remote connection (with Management) | |||
Remediation including full reimaging | |||
Business continuity (with Disaster Recovery) | |||
GenAI Protection: Usage monitoring | |||
Augmenting Microsoft Defender AV | |||
URL filtering | |||
Exploit prevention | |||
Real-time threat intelligence feed | |||
Automated, tunable allowlisting based on profiling | |||
Forensic data collection | |||
Event monitoring | |||
Automated event correlation | |||
Prioritization of suspicious activities | |||
AI-generated incident summaries | |||
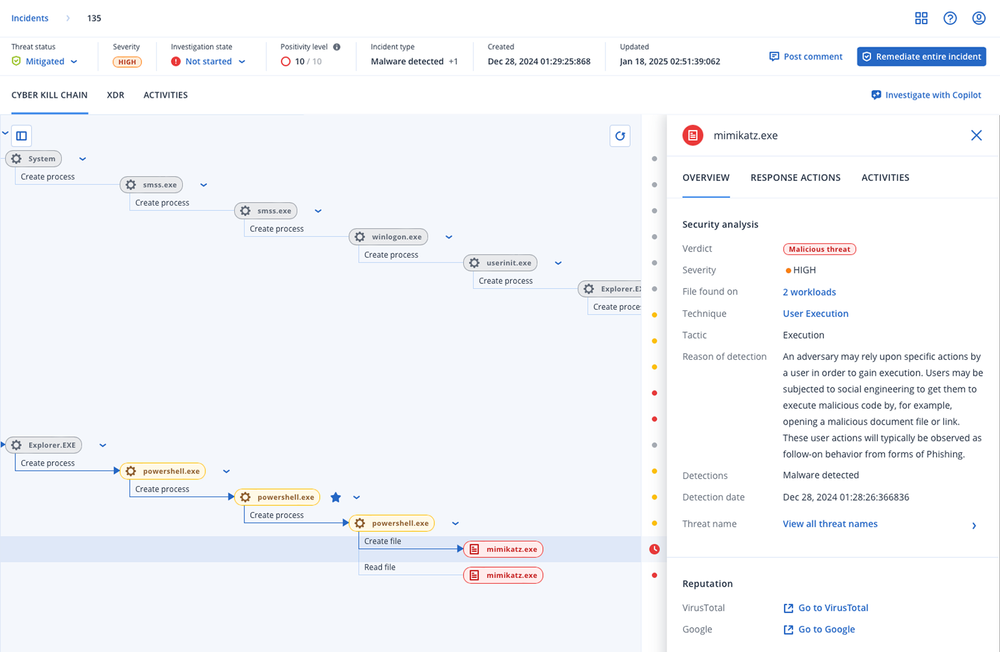
Automated MITRE ATT&CK® attack chain visualization and interpretation | |||
Single-click response to incidents | |||
Full threat containment including endpoint quarantine and isolation | |||
Intelligent search for IoCs including emerging threats | |||
Attack-specific rollback | |||
Integration with Email Security (email telemetry) | |||
Integration with Entra ID (identity telemetry) | |||
Integration with Collaboration Security (Microsoft 365 apps telemetry) | |||
Delete malicious email attachment or URLs | |||
Search for malicious attachments across mailboxes | |||
Block malicious email address | |||
Terminate all user sessions | |||
Force user account password reset on next login | |||
Suspend user account | |||
MDR service | |||
Public API for EDR |

Acronis operates a global network of cloud data centers designed to deliver a high level of safety, security, and accessibility.
Looking for help?
Sorry, your browser is not supported.
It seems that our new website is incompatible with your current browser's version. Don’t worry, this is easily fixed! To view our complete website, simply update your browser now or continue anyway.