Backup and antimalware are two essentials parts of the typical endpoint security posture. While scanning for malware is usually performed before backing up, it is still possible for malware to make its way to a backup image – either because the detection capabilities of the average antimalware solution are lacking or the backup was created before doing an antimalware scan.
Full scanning of large archives requires considerable time and computational resources, which are often not available or not an efficient use of the time and resources. Scanning archives becomes especially critical if the archives are in cloud storage because the speed of accessing a cloud-based archive may be significantly slower than that of a local storage device (depending on the speed of the network or communication channel being used, and/or how heavily the channel is loaded).
If any problems arise – such as a virus or malicious file is found in the archive – the archive is considered infected and damaged and may not be suitable for use in a system recovery or file and data extraction.
To avoid restoring data that is infected, the usual practice is to periodically scan archives in storage with antivirus scanners – especially when new slices are added to the archive or before restoring the data. Yet there are no solutions currently available that scan arbitrary time points in an archive, so solutions must scan the entire archive.
If determined to be damaged or infected, data in archives cannot be repaired.
Acronis technology solves these issues
Acronis Cyber Protect delivers scanning of full-disk backups at a centralized location to find potential vulnerabilities and malware infections – ensuring users have malware-free backups for their restores. The centralized location can be in the Acronis cloud or on an on-premises server, and support for Amazon, Google, Microsoft, or any other popular cloud storage and environment is planned.
Acronis engineers made it possible to search for malware not only in one big backup but also in archived slices. We can mount the first slice of a plurality of slices in a backup archive, wherein the first slice is an image of original user data. Acronis technology can then detect a modified block of the mounted slice, identify files in the mounted first slice that correspond to the modified block, and scan specific files for viruses and other malicious software. The approach also allows Acronis to generate a cured slice that consists of user data from the mounted first slice without malicious files. Scanning in centralized locations this way enables Acronis Cyber Protect to:
- Reduce loads of client endpoints
- Restore only clean data
- Increase the likelihood of rootkit and bootkit detections, which are not easily detected during the first on-access or on-demand scans
Having that capability means that not only can an admin conduct a regular backup scan, but each of his clients' backup increments can be scanned for malware in a centralized location.
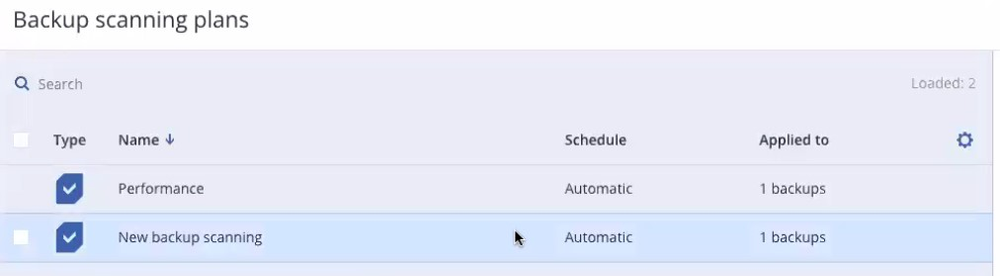
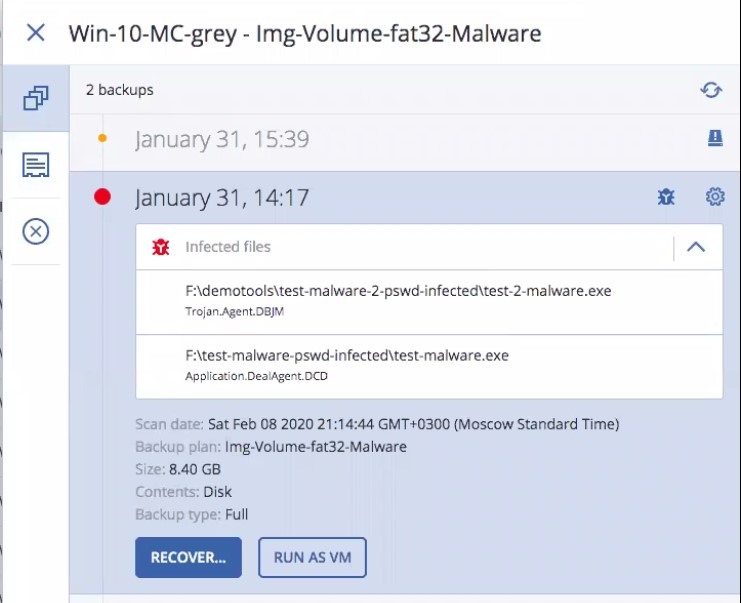
Later, the admin not only has points of recovery but “safe recovery points” where no malware was detected are indicated, as are unsafe slices with malware.
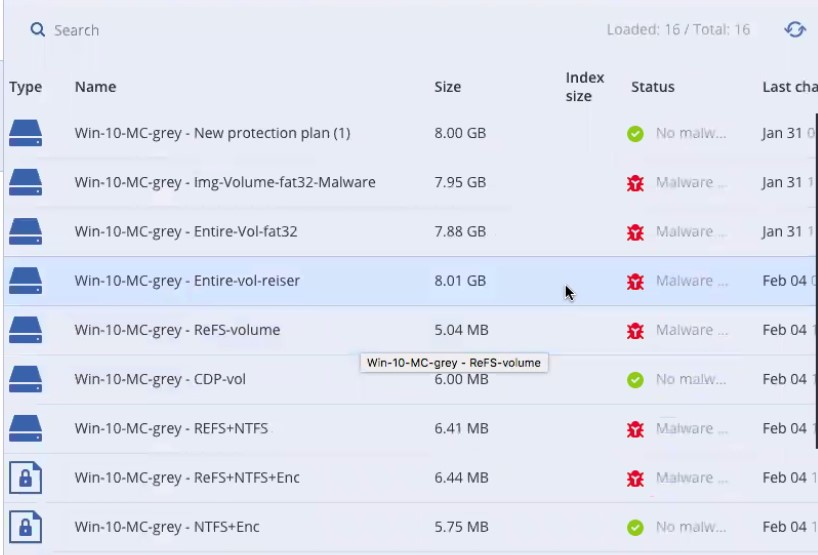
Using the Acronis Cyber Protect management console, an admin can see in detail what infected files were found and when – and then delete the malware out of those backup slices and restore a clean copy of data. Acronis’ backup scans use the latest definitions, so even if unknown malware was not detected initially, it will be detected during the next full scan of the backup.
Acronis’ technology can currently scan full disk or volume backups with increments, although file backups are not yet supported.
Final thought
While other products can only mount a backup image and scan the entire image, Acronis Cyber Protect is much more efficient by quickly scanning new slices after a scan of an initial slice. That means malware scans are several times faster than the competition (depending on the size of the volume image and the competitor’s scan engine performance). Acronis’ technology also uses advances of its Archive 3 storage format API and NTFS file system capabilities, which is another reason why operations are highly optimized and deliver such high performance.
For additional information about Acronis Cyber Protect’s ability to scan backups for malware, please refer to the whitepaper on Acronis: Backup Scan for Malware.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.



