When Acronis True Image 2017 New Generation was introduced in January 2017, it marked a new level in data protection as the first backup product to deliver effective behavior-based protection from ransomware. Later that same year, with the release of Acronis True Image 2018, we enhanced our Acronis Active Protection set of technologies with artificial intelligence (AI) to deliver an additional layer of security to an already effective and award-winning anti-ransomware defense.
With the newly released Acronis True Image 2019, we’re bringing even more enhancements to our cyber protection and anti-ransomware technologies, making the product even more secure and user-friendly.
New Machine Learning models
As you may remember, Acronis uses AI and machine learning models to analyze stack traces in Windows processes, in case our behavioral heuristics need a “second opinion” to decide if a process is ransomware or not.
In Acronis True Image 2019, we’ve implemented a new model for stack trace analysis, based on the Gradient Boosting Tree technique. The idea is that the trees in this technique are not equally weighted depending on the situation in which different trees are used. While we previously didn’t analyze how often a particular stake frame appears in the stack, we now do – so we only take popular frames to learn from based on a special internal dictionary. Excluding rare frames from the learning process increases the overall accuracy while delivering other benefits.
This approach, for example, allows us to keep the same sized model (or even slightly less) while including much more data. By comparison, if we kept using the previous approach, our ML model would grow to dozens of megabytes – 10-times larger than it is now.
This innovative technique both boosts performance up to 150-200 percent compare to the previous approach and increases accuracy – allowing the new model to detect when a user receives an email attachment that claims to be a PDF, but in reality, it is malicious executable.
Protection of network attached storages and network shares
Most valuable data is stored locally, although many working files can also be found on network shares, in local folders with remote/shared access, and on network attached storages (NAS). Since many ransomware strains will try to attack networks shares in addition to local files, in Acronis True Image 2019 we extended the coverage of our anti-ransomware technology to include network shares and NAS devices.
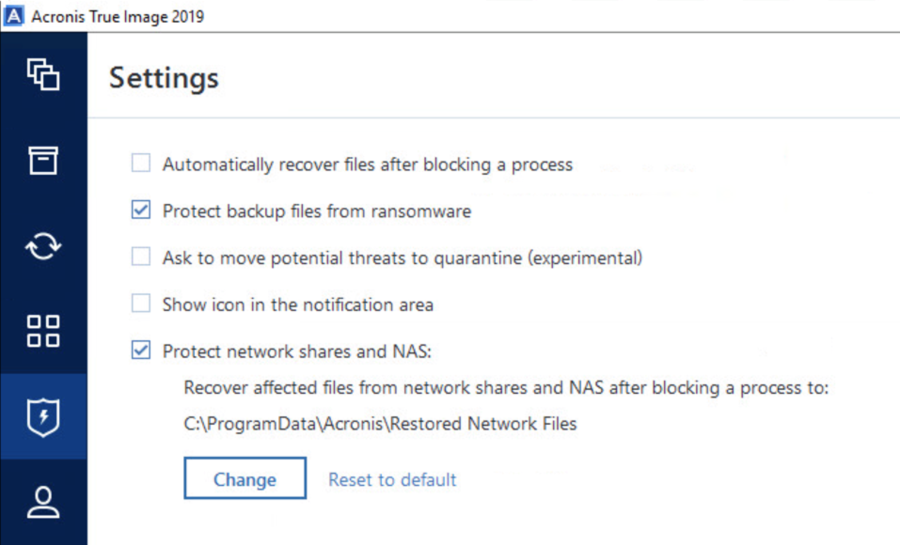
Acronis Active Protection will detect ransomware if it begins to encrypt files on network shares. Plus you can restore files to a local folder – either a default Acronis folder or another user-defined folder – to ensure you can recover encrypted files even if the attack causes volatile network availability. Users can switch the network shares protection off, but we strongly recommend keeping it enabled (as by default).
You can choose a folder to restore affected files from NAS or network share.
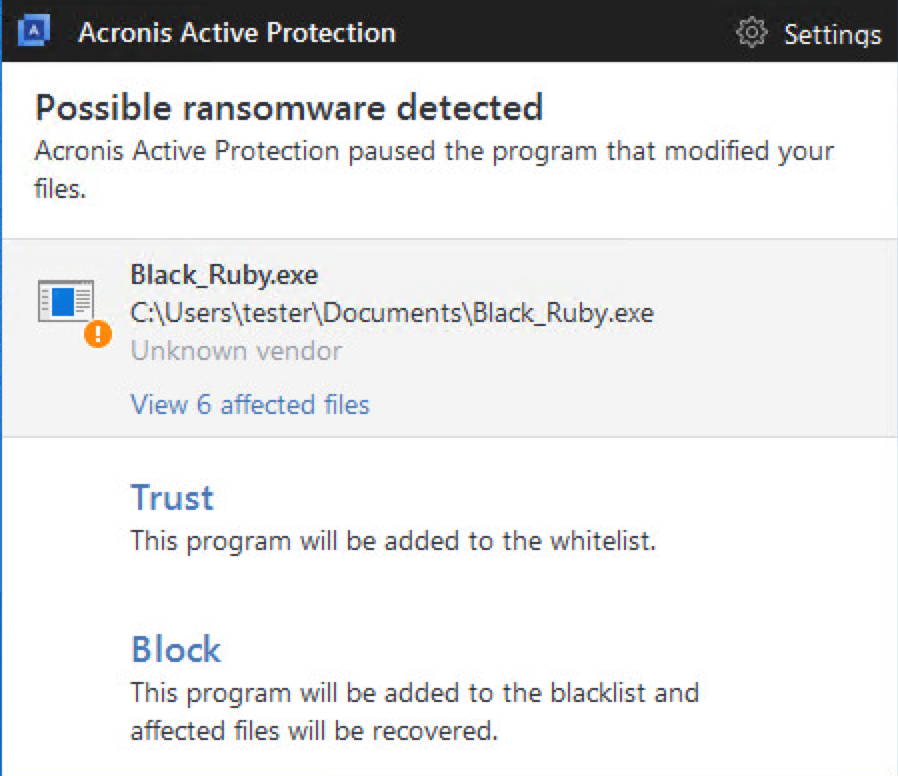
Black Ruby is one of the ransomware families that is capable of encrypting files on local shares.
Better usability and flexibility
We continue to improve the usability of our solution, responding to user suggestions on how we can make their experience better. One goal is to keep users better informed, which is why Acronis True Image 2019 provides information on sophisticated ransomware – such as attacks that use interpreters like PowerShell, WScript, Java, Python, Perl, Ruby, cmd.exe, etc., or run malicious dlls via rundll32.exe to perform the infection or other actions. There are plenty of ransomware families that use this technique, including Locky, Cerber, CryptoWall, Crypt0L0cker, CTB-Locker, RAA and many others.
Notifications now show you when a malicious dll or script (with a name) is using a legitimate interpreter in order to attack your data. This should help in cases when the user is not sure he should block the process or allow it to run.
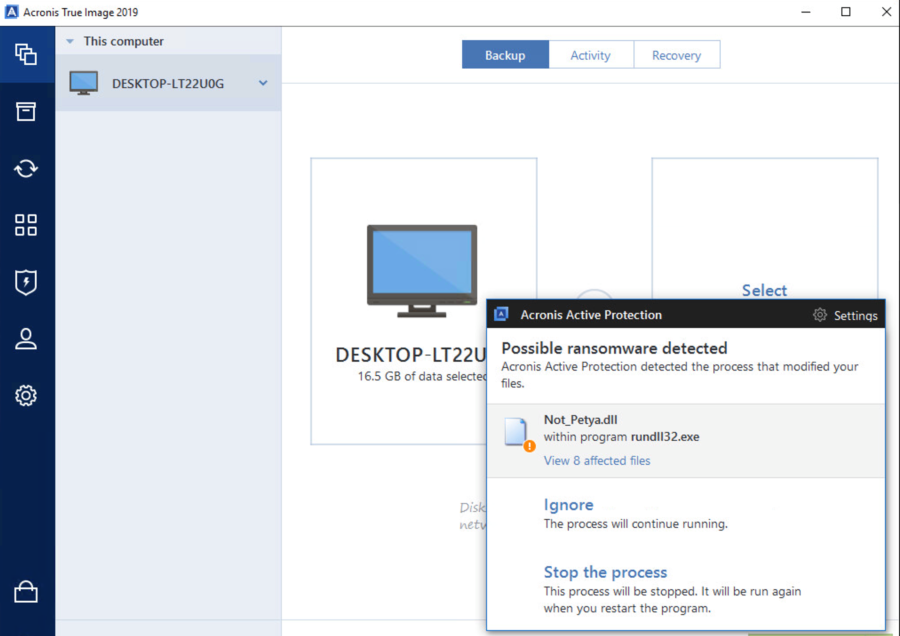
Now you will see a Not_Petya.dll warning instead of rundll32.exe
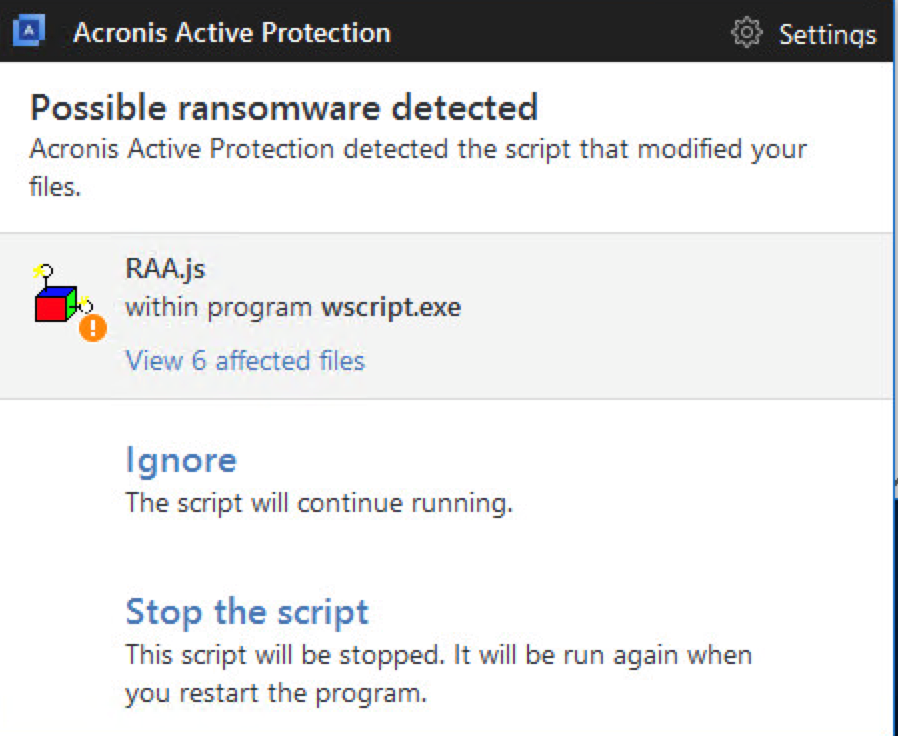
Malicious script executed through PowerShell also will be displayed properly.
Now, there’s also the ability to whitelist or blacklist a malicious process immediately after detection. Users also have more flexibility in controlling those processes, allowing them to modify files, to modify files and backups, or block them as before. Whereas Acronis True Image 2018 included Master Boot Record (MBR) protection as part of self-defense settings, now it is possible to control the self-defense capabilities and protection of MBR separately, giving users even more flexibility.
More security and convenience
In addition to these enhancements to the anti-ransomware capabilities, Acronis True Image 2019 includes a number of new features. Users can now use an external hard drive to create an Acronis Survival Kit, an all-in-one recovery tool that includes everything needed to restore your system, from boot media to all your backups. New event-based scheduling capturing your backups simple, since you can have the process begin automatically when you connect an external USB drive.
Mac users can now clone an active disk making the process of migrating to a faster Mac or one with larger disk easy. They also can enjoy faster recovery of virtual machines now that Acronis True Image 2019 uses the native Parallels Desktop 14 API to back them up.
Acronis True Image 2019 brings a lot of improvements in terms of security and ease-of-use. We encourage you to switch to the new version to enjoy a higher level of security and accessibility.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.




