As Diamond sponsors for the Black Hat 2021 conference, Acronis sent Acronis’ VP of Cyber Protection Research Candid Wuest and Cybersecurity Analyst Topher Tebow to attend sessions, answer questions, and gather as many insights as possible.
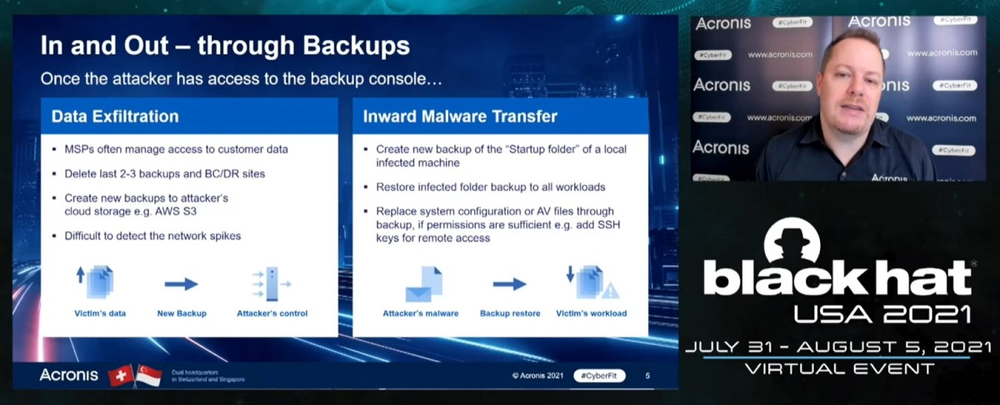
Candid also presented a session, Ransomware Attacks Against MSPs – A Nightmare for SMBs, and attendees who were not able to join at the time should take advantage of the replay option.
We asked the pair to report back on their impressions for Day 1.
Cybersecurity needs an attitude adjustment
In attending different sessions during Day 1 of Black Hat 2021, both Candid and Topher said there was still some old-school thinking on display that really needs to be replaced given the current threat landscape.
Reacting to the keynote from Matt Tait, Candid said, “The keynote was good, highlighting the issues with vulnerabilities. For example, researchers often still don’t publish their findings because they fear legal actions by the companies. But that makes it bad for everyone. Yes, bug bounties are important, but the overall attitude should change as well.”
By being more open in the discussion about their experiences, their findings, and the strategies that work for them, cybersecurity pros can go a long way to getting in front of today’s fast-moving threats.
Topher echoed the need for a change in attitude. “The cybersecurity industry as a whole needs a massive mental shift if we are going to stay relevant. We need to get back to being a step ahead of the adversaries. It’s not 1998 anymore, and it’s time for old mentalities to be taken out with the trash. This goes for all aspects of the business, not just procedural, or in the tools we use – but right down to our hiring practices and company cultures. We need to rethink and reevaluate everything we thought to be true up to this point.”
Ransomware still dominates
Unsurprisingly, there was a lot of discussion regarding ransomware, mainly around how to detect it early and how to recover.
“In the wake of this year’s ransomware attacks, companies are running scared,” said Topher. “The saying ‘It’s not if you are attacked, but when,’ used to be thrown around and laughed about – and now it’s said with a certain heaviness. The good news is that we’re already seeing companies taking the potential of attacks more seriously, and beginning to look at how they can improve their security posture.”
In his keynote, Tait outlined the scale of some of the recent attacks. After discussing the use of supply chains, he noted that government agencies won’t be able to protect against them in the future, it’s up to platform vendors.
Candid seconded an observation from Fortinet’s Derek Manky, who was speaking at the Dark Reading news desk. “The guidance normally is that companies should not pay the ransom,” said Candid, “but if they are actually faced with the decision, the discussion might be different. That is why it is important to prevent these attacks, and why it is increasingly important to openly discuss the threat and its impact.”
“An ounce of prevention…”
The theme of prevention was another topic that both Acronis experts noted from their Black Hat experience.
Candid observed that the Next-Gen DFIR Mass Exploits and Supplier Compromise session was useful. “They walked through some recent cases like SolarWinds, Kaseya, and the Microsoft Exchange vulnerability. They provided good tips on how to handle such attacks.”
Specifically, the advice was to conduct threat hunting to know what’s going on in your network, as well as train and prepare before an incident occurs.
Unfortunately, he added that many of the sponsored sessions focused on what organizations should do after a breach is detected, which only covers half of the issue – and presents a conundrum for cybersecurity pros.
“On one hand, that means that these speakers all expect a breach will happen and not be detected in time,” and are offering solutions to help. But he added, “on the other hand, it also means that all the technologies that have been applied during the past few years didn’t work to protect us.”
While it’s true that no solution can stop 100% of attacks 100% of the time – making it important to know how to respond – it seems a greater focus needs to go into effectively preventing attacks from succeeding in the first place.
Favorites of the day
Since not everyone can get to Black Hat 2021, Topher and Candid shared a few thoughts on their favorite sessions from Day 1.
Candid’s highlights included Darktraces sponsored session AI Red Team and Attack Path Modeling. “This session was an interesting intro to the topic: Showing that AI could well be used for automation of penetration testing. Often the discussion is more about adversarial AI – breaking and manipulating an AI model – which is a tricky field, as it's not so easy to patch an AI model if a serious flaw is found. We probably will see more and more attacks against AI/ML and of course attackers using AI/ML for their own benefit.”
Another session he enjoyed was Smashing the ML Stack for Fun and Lawsuits. “They looked at what safeguards are in place in ML models to prevent attackers from looking into them. These roadblocks will not keep attackers out – they can still reverse engineer it – but it can provide a legal basis that allows companies to sue someone who tries to steal and copy the ML models. This could be for IP and trade secrets. It’s an interesting question: How do you protect the knowledge that you put into ML models?”
“Personally, one of my favorite talks today was The Ripple Effect: Building a Diverse Security Research Team,” said Topher. “Oryan De Paz and Omer Yair discussed how they went from an all-male team to a team that was 50% women, and the lessons they learned along the way. One point that really hit hard is that the goal is not to have a 50/50 split between men and women, but simply to have an atmosphere of inclusivity. This even goes beyond gender and racial equality, but also to the skills across the team.”
Topher explained that they encouraged recruiting for the long run: Finding great employees who have a lot to learn because your team will ultimately be stronger for it and with less attrition.
“Just because somebody doesn’t have a cybersecurity background doesn’t mean they won’t be a perfect fit for a cybersecurity team. If they have skills that translate well, it just might be worth giving them a shot. Of course, the atmosphere they are hired into is just as important, keeping judgment at bay, and giving everyone the freedom to learn and grow – no matter what their experience is or how long they have been with the company."
Final thought
Now into Day 2 of Black Hat 2021, both Candid and Topher are looking forward to the sessions they’re joining today and those that they’ll be able to watch on-demand later.
While the ability to watch sessions later is a definite plus, both of them said the online experience of this year’s conference lacked some of that unplanned knowledge sharing that happens attending a conference in-person. Both are looking forward to connecting with their peers face-to-face soon.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.



