Over the last few years, Acronis has invested significantly in Acronis Cyber Protect Cloud. In 2020, Acronis first announced its Technology Ecosystem and made its API accessible to partners, allowing any independent software vendor (ISV) or managed service provider (MSP) to build an integration of their platform with Acronis or automate some routine operations. Today, Acronis has more than 200 integrations with industry leaders in RMM, PSA, security, remote desktop and other application categories — integrations MSPs use daily.
Today, we are proud to announce a new chapter in Acronis history with the release of Acronis CyberApp Standard, a unique development framework that provides a fully digital ISV and MSP experience to build an application on the Acronis platform.
What is CyberApp Standard?
The CyberApp Standard concept has been with Acronis for a while — it's the same framework that we use internally to bring new products to market. Now, ISVs and MSPs (Let's address this group as partners) can use this framework to build their own applications and bring new services to the Acronis platform, while benefiting from the platform’s capabilities: multitenancy, workload and user management, reporting, alerting and more.
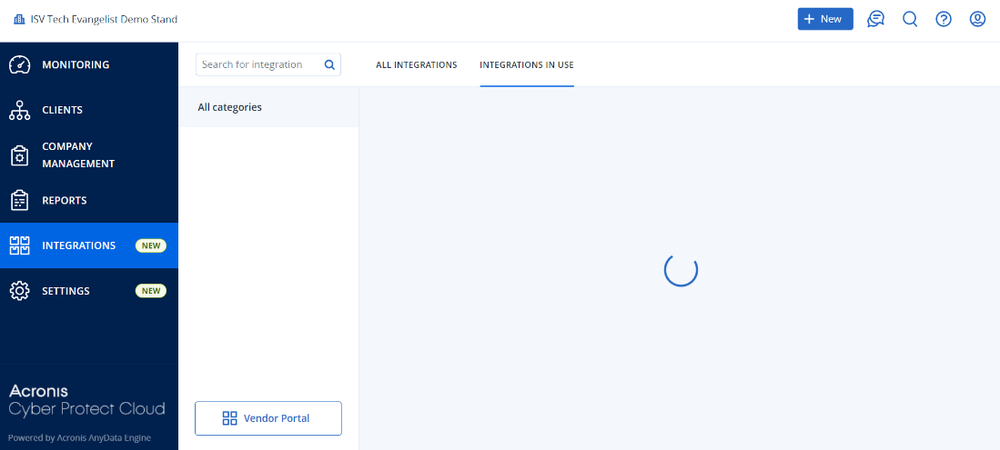
Our partners can now work with this framework in a straightforward way with the Acronis Vendor Portal, available in Acronis Cyber Protect Cloud. It’s a dedicated workplace for a partner to build, test, deploy and manage their integration with Acronis.
What is so unique about Acronis CyberApp Standard? A lot.
One-click signup
Getting started in the Vendor Portal requires just three steps:
1. Navigate to developer.acronis.com
2. Register
3. Activate your special Acronis Cyber Protect Cloud account
That’s it! Once you register, we will create a special sandbox tenant for you in Acronis Cyber Protect Cloud. You can use it for building and QA purposes. In the same tenant, in the Integrations tab, you will see the link to the Vendor Portal. It is your development environment connected to your tenant. When you’re building and testing your application, you will do it from your tenant.
Also, once you register on developer.acronis.com, you are automatically registered as a developer in the Acronis #CyberFit Technology Partner Program. The process is self-service and requires no additional steps or contact with us.
‘Hello world’ — Fast proof of concept
To understand what it is — to build a CyberApp — you can quickly create a prototype.
First, you need to create a partner tenant in Acronis Cyber Protect Cloud. Click New in the top right corner, select Partner and follow the on-screen guide.
Now, you can create an application.
In the Vendor Portal, click Create application, enter the CyberApp name and that’s it! You’ve just created your first CyberApp. Now you can open it and work with its main components. There are three:
· Application description — A representation of your application in Acronis Application catalog. Take a look at one of existing integrations as a reference at solutions.acronis.com Application version – An existing application that will be later deployed and embedded into the Acronis Cyber Protect Cloud platform.
· Deployments — A list of your applications that you deployed to your sandbox.
Now, how can we get hands-on experience without building a full application? Follow these steps:
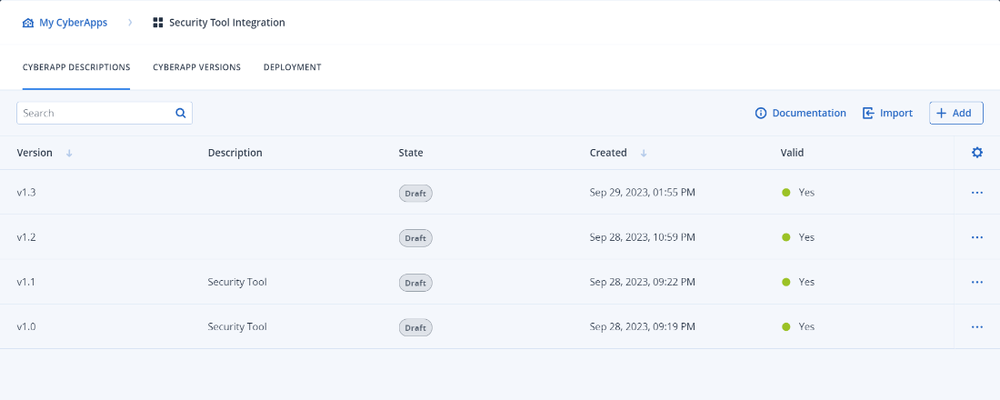
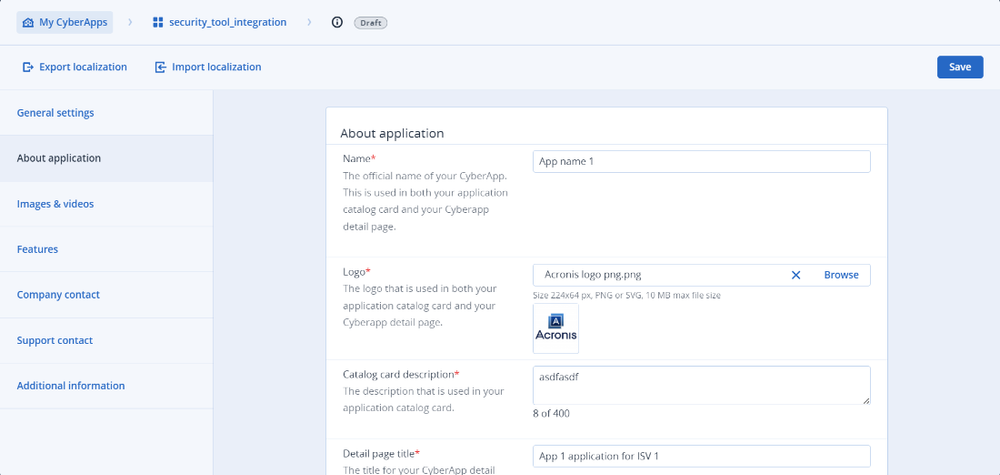
1. Create your application description. You will see a lot of fields, but to create a test deployment, you will have to fill in these fields and save.
2. Open Application Versions and create a new one. You will need to fill in the version number and API callback handler and select a category. Save the application version.
3. Open the Deployment section. In the dropdown, please select Deploy to test environment and select the application version and description that you just created.
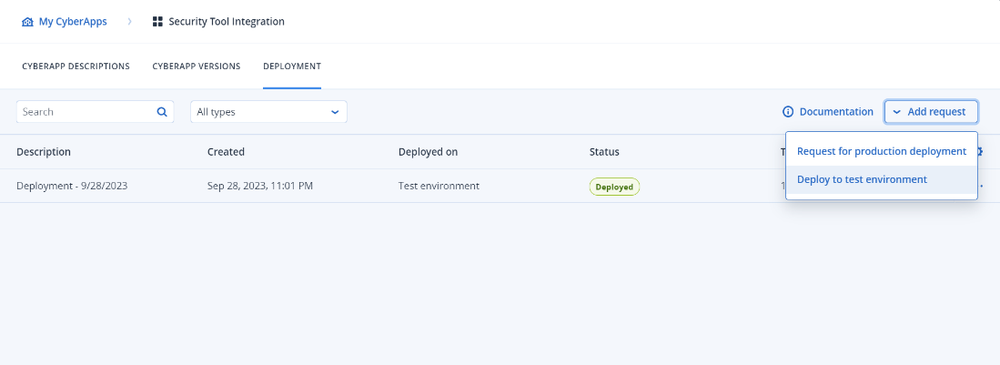
Done! In a few seconds, your application will be deployed to your partner environment.
Now, login to your partner tenant — to which you deployed your application — and you will see the application tile. This is how you can quickly test the technology and understand how to work with the Vendor Portal.
Building an application
Now that you understand how to work with Acronis CyberApp Standard, you can proceed to building your application. This process can be divided into eight intuitive steps:
1. Identify your integration scenarios: For simplicity, we have precreated several integration scenarios based on your solution type.
2. Create a connection setup form: This is a form that MSPs see when they enable the integration.
3. Create and configure all necessary platform-extension points in the Vendor Portal.
4. Create a callback handler in your cloud service. It’s a special set of callbacks that are required to run synchronous operations in your service; for example, ‘add user’, ‘reset password’ or ‘scan a device’.
5. Create a connector for synchronization of such data as alerts from your service to Acronis.
6. Deploy your application to your sandbox and test it.
7. Fill in a full application description — or review it.
8. Request deployment to production.
Acronis R&D, product management and solution marketing will see your request, review it and approve publication. At any time, you can send your business- or marketing-related questions to tpp@acronis.com
Unique integration scenarios with Acronis CyberApp Standard
Acronis CyberApp Standard provides unique depth of integration for technology partners. What do developers usually expect in terms of integration capabilities? These remote monitoring scenarios might immediately come to mind: agent deployments, agent status checks, preconfigured command execution and device-view customization with additional columns in the list of managed devices relevant to your product or service. With CyberApp, you can build much more.
Out-of-the-box scenarios supported on the platform level
One of the most complex scenarios that any vendor confronts is tenant or site mapping, such as when an MSP needs to connect customer instances in platform A to similar instances in platform B. With Acronis CyberApp, we have done this for you.
When you build an application, you don’t need to create an interface and implement the whole tenant-mapping logic. In Acronis CyberApp, you need to support several standard callbacks — we’ve taken care of this. The tenant-mapping interface, logic and error handling is available for MSPs out of the box.
Wide range of integration and platform extension points
With Acronis CyberApp Standard, you can achieve a similar integration depth of your application — just like Acronis’ own services. Here are the kinds of data and objects you would be able to bring for service providers:
1. Alerts from your service — Will be shown in the same alerts list, next to Acronis’ own alerts.
2. Workloads — In case you have a workload or endpoint agent, you can add it to the list of Acronis workloads and define what kind of information they should bring — from agent versions to workload statuses.
3. Workload actions — Particular actions that you specify and that the MSP can execute for a particular device.
4. Widgets – You can add a widget in the Acronis monitoring section, or you can expand existing Acronis widgets with your data.
5. Reports – Very similar to widgets.
By now, you should have already formed your opinion about our new development framework — Acronis CyberApp Standard. It is easy to use, low code and doesn’t demand a certain technology stack on your side. Unlike any other MSP platform, Acronis provides a fully digital experience for you to build, test, deploy and update your application. Acronis automatically enrolls you into our dedicated Technology Partner Program and fuels your go to market.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 60+ countries. Acronis Cyber Platform is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.