In light of the unfortunate and devastating spread of the COVID-19 pandemic – and the spike in cyberattacks in its wake – the need for cyber protection is even clearer. That need is particularly acute for the people and companies who had fallen behind in the cybersecurity race due to budget constraints or lack of attention.
Now that individuals are deeply stressed, cybercriminals are using every angle of attack, including playing on the natural fear of COVID-19 and the desperate search for information. In the last two weeks, Acronis has seen a significant increase in cryptojacking, while ransomware attacks are growing rapidly as well.
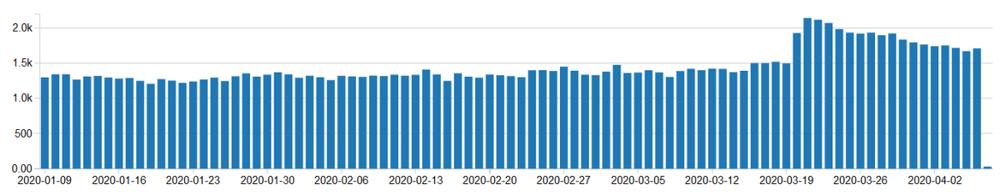
The number of users affected by cryptojackers grew significantly in the last couple of weeks.
Exploiting work-from-home tools
Now that employees from so many organizations are working remotely, a unique aspect of these new attacks is that criminals are targeting a variety of remote work tools, including the popular teleconferencing platform Zoom.
As more and more users must rely on these tools, they are getting things like fake Zoom invitations that are socially engineered to trick novice users into installing cryptojackers, ransomware, Trojans, and other types of unwanted software on their system.
Europol’s European Cybercrime Centre issued a report about the changes in cybercriminal tactics during the COVID-19 pandemic, and they draw the same conclusion as Acronis:
- The pandemic has multiplied the ransomware attacks against certain institutions
- There is a clear connection between the pandemic and efforts to exploit children who are not in schools and instead are spending more unsupervised time online
While Europol fights a wide range of COVID-19-related scams – they recently arrested a man for a coronavirus email scam peddling masks and sanitizers – the fight is far from over. The number of malicious COVID-19-themed domains registrations may have stabilized, but there are still many fake and infected websites out there that use the topic to extort credentials or spread malware.
Lack of security of work-from-home staff
The fact that many people now have to work from home on their own computers brings another security disaster. Not only do those home machines often lack effective cyber protection, many do not regularly apply the latest security patches for their operating system and popular third-party software, which leaves their machines vulnerable to attack.
Covering these vulnerability and patch management issues on the edge is a headache for admins or technicians that provide the IT support to help small businesses survive during this emergency.
The upcoming launch of Acronis Cyber Protect Cloud (part of our Acronis Cyber Cloud service provider platform) actually solves this issue. It delivers vulnerability assessment and patch management functionality that supports a lot of popular third-party software in addition to all Windows OS apps. More than that, the embedded remote desktop functionality enables admins who work with Acronis Cyber Protect to solve any issues remotely – saving time, nerves, and people's health as we minimize our contact with others to stop the spread of the coronavirus.
REMINDER FOR MSPs: Acronis COVID-19 response programs
As global business adjusts to the remote-work environment during the COVID-19 pandemic, clients are counting on service providers to help them adapt. Acronis has put special measures in place so service providers can ensure that their clients have the tools and resources needed to be both productive and protected.
- We are offering service providers Acronis Cyber Files Cloud – our secure, enterprise-grade file sync and share solution – free until July 31, 2020 to enable their clients to quickly and easily transition to a secure remote work environment.
- For new customers added by a service provider partner after March 18, Acronis will not charge the net new end customer consumption of Acronis Cyber Backup Cloud – our business cyber protection solution – between March 18 and July 31, 2020. This will enable clients to strengthen their protection posture even though they did not budget for it.
Details of these response programs can be found here.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.




