You are on United States website. Change region to view location-specific content:
Global
English
Select another region
Choose region and language
- Americas
- Asia-Pacific
- Europe, Middle East and Africa
- Worldwide
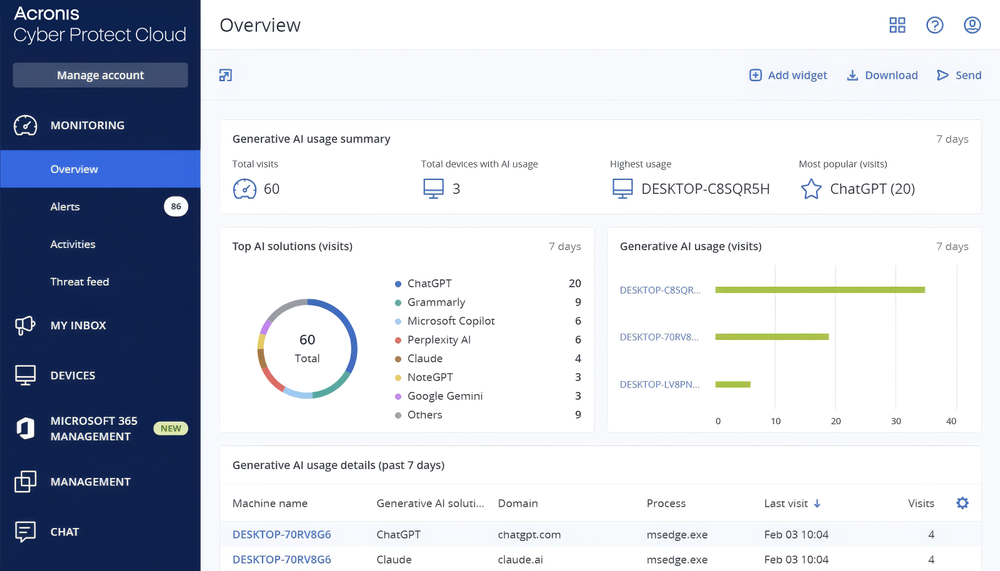
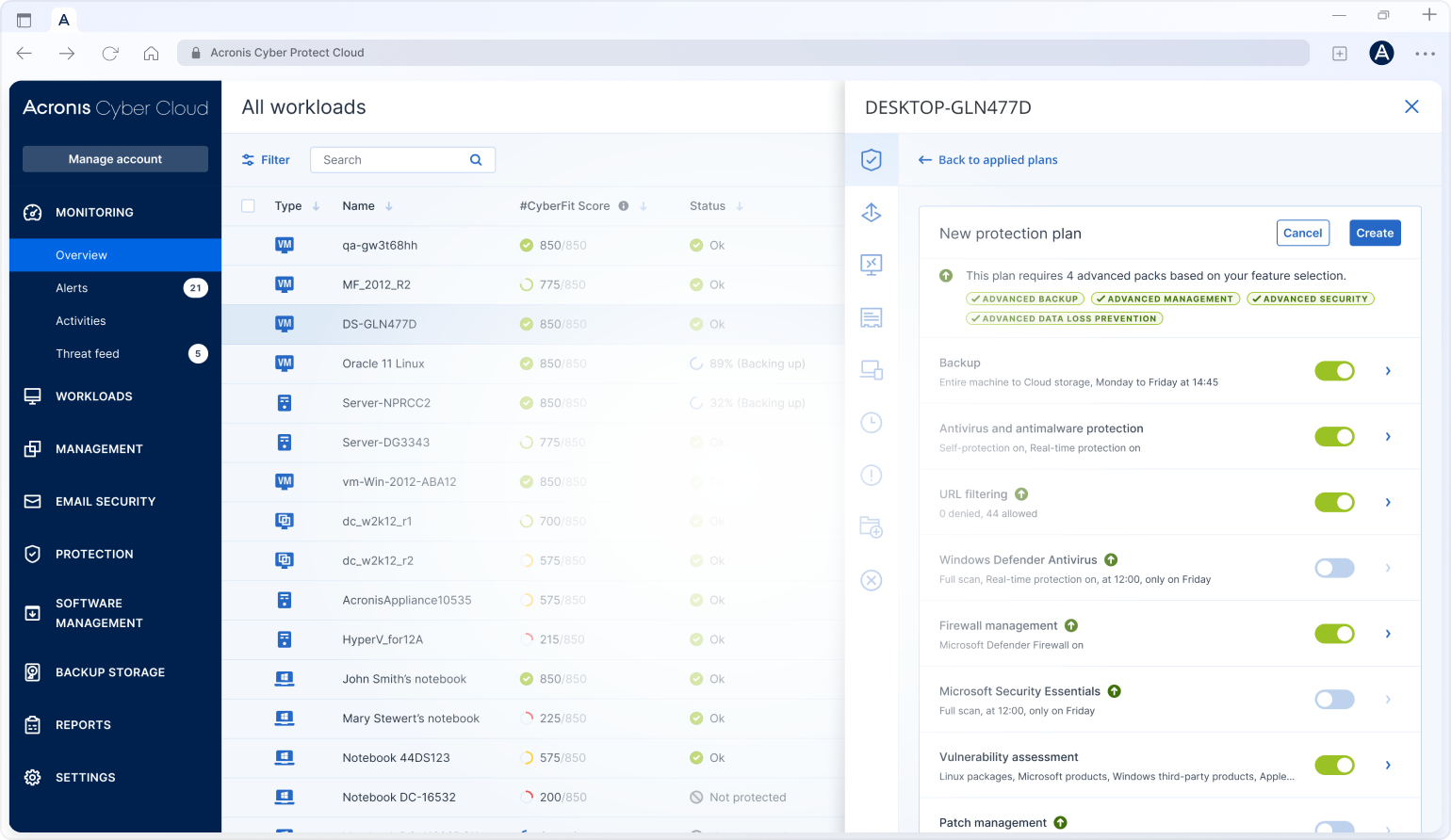
Businesses want the benefits of AI, but not the risk. They already use AI tools for research, writing, coding, and customer communication but often without control or visibility. This creates shadow AI, data exposure, and compliance gaps. Now MSPs can change that. Deliver secure AI productivity as managed services, fully integrated into the platform you already operate, with governance, visibility, and protection built in.
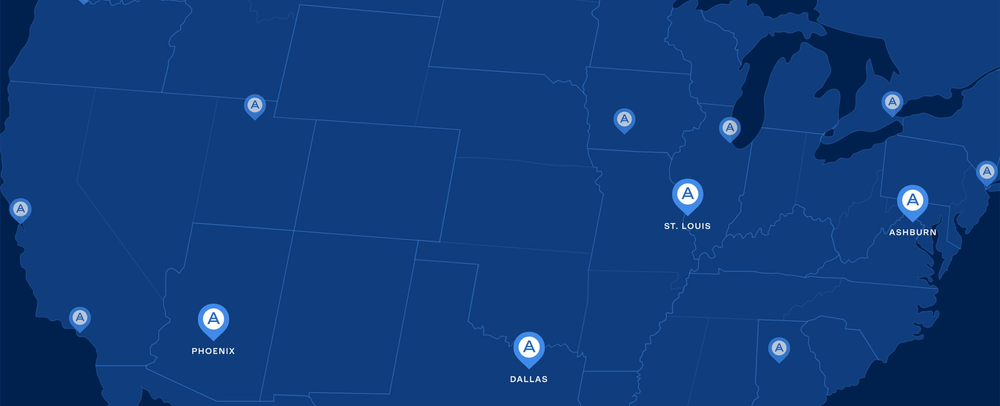
We provide robust and efficient data protection with data centers in Dallas, Ashburn, Phoenix & St Louis and over 50 DCs globally





Deploy in minutes
Deliver services

Shadow AI ➔ Managed AI
Businesses want the benefits of AI, but not the risk. Be ready to help, with AI Protection and enterprise-ready GenAI capabilities, managed by MSPs.
Cloud-native architecture by design
21,000+
Service providers
150+
Countries
5 million+
Workloads protected
50+
Global data centers

Latest on threats to managed IT service provider community

Acronis' Threat Research Unit discovered a rare in-the-wild example of a FileFix attack — a new variant of the now infamous ClickFix attack vector.
Consistently recognized by leading industry analysts for its innovative and effective cyber protection capabilities
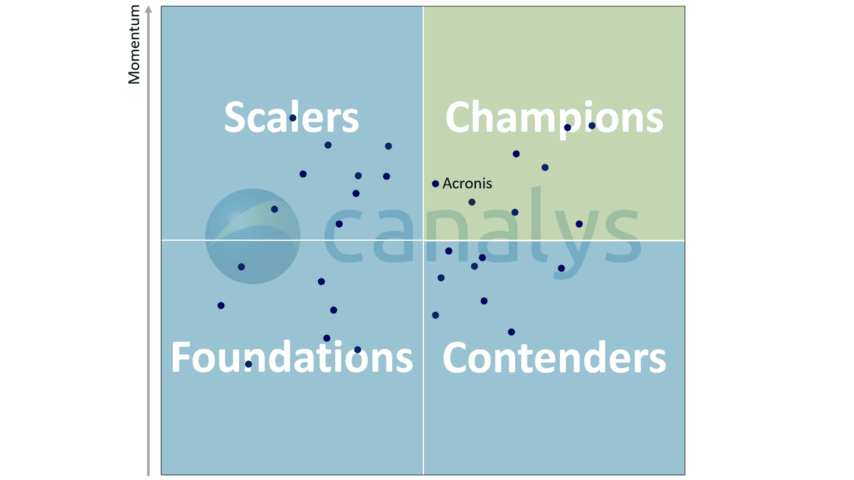
Global Canalys Cybersecurity Leadership Matrix 2025 identifies Acronis as a Champion
Canalys has named Acronis as a Champion in the Cybersecurity Leadership Matrix, citing Acronis' MSP-first approach and overall ease of doing business.
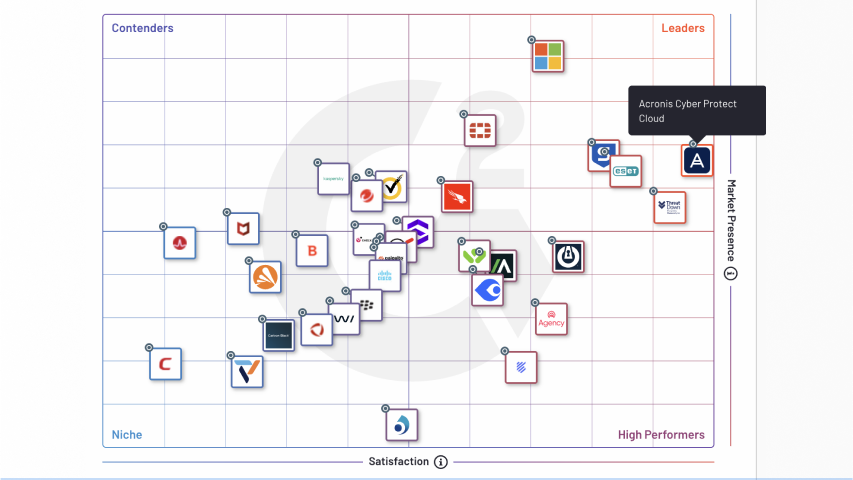
Acronis earns top placement in the G2 Spring 2025 Grid® Report for Endpoint Protection Suites
Acronis has been recognized in the G2 Spring 2025 Grid® Report for Endpoint Protection Suites, reaffirming our commitment to delivering industry-leading cyber protection.
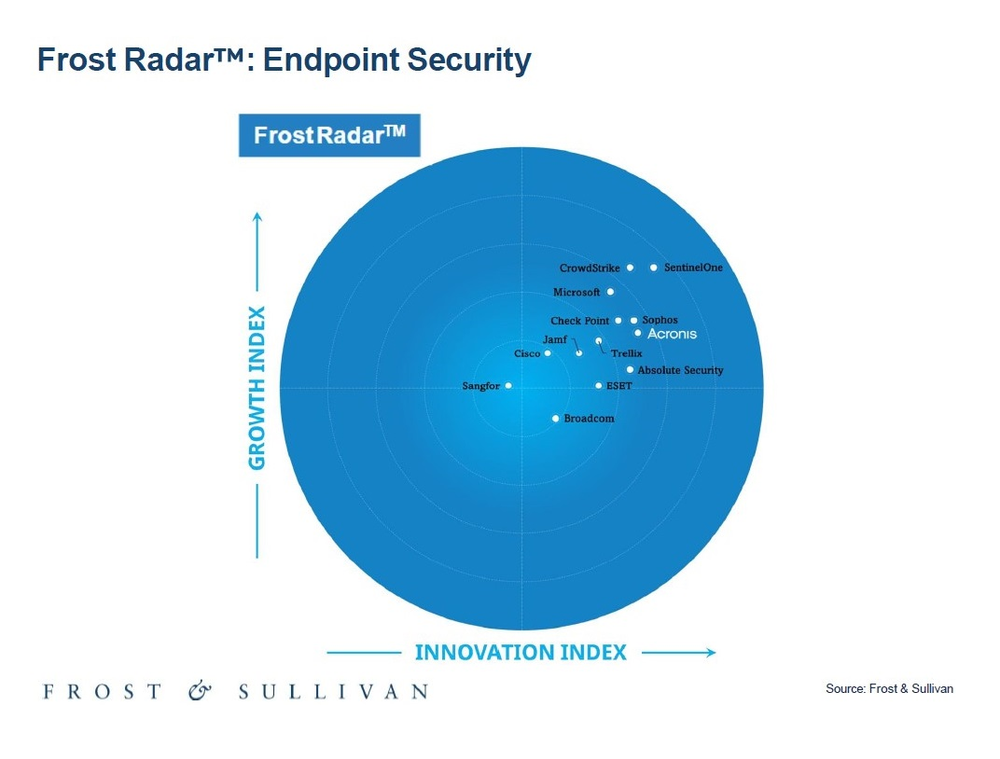
Frost & Sullivan names Acronis a Leader in its 2025 Endpoint Security Radar
The Frost Radar™: Endpoint Security report explores how Acronis is shaping the future of endpoint security and provides insights into the leading solutions in the endpoint security market.
Success journey with Acronis

Managed Service Provider training and certifications
Educational pathways tailored for every learner. Acronis offers different training and certification programs to help individuals and managed service provider (MSPs) enhance their cybersecurity skills and knowledge.
We have students from 112 countries. Our trainers deliver trainings worldwide, in any time zone, and in 8 languages:
Sorry, your browser is not supported.
It seems that our new website is incompatible with your current browser's version. Don’t worry, this is easily fixed! To view our complete website, simply update your browser now or continue anyway.