
Acronis Active Protection is an advanced technology that uses sophisticated analysis to monitor and stop erratic processes on your system. If ransomware somehow manages to get through your anti-virus and starts to encrypt files, Acronis Active Protection will detect the encryption and immediately halt it – automatically restoring the files to the most recently backed up version.
While performing well in independent testing and earning accolades from the media, Acronis has worked diligently to make it even better. The result is an improved version that incorporates machine learning and artificial intelligence technologies.
Why machine learning?
Machine learning is often associated with big data, referring to the analysis of enormous volumes of data to produce some actionable results. The larger the data, the better the result as machine learning based on the amount of data and the algorithms chosen.
So how does Acronis machine learning work? The first step is a stack trace analysis. A stack trace is a report of the active stack frames at a certain point in time during the execution of a program. When a program is run, memory is often dynamically allocated in two places: the stack and the heap. Memory is contiguously allocated on a stack, but not on a heap – as indicated by their names.
Put simply, it is possible to detect code injections from ransomware using process stack trace analysis based on machine learning approach.
Real-life scenario
Acronis compiled massive volumes of data by taking clean Windows systems that run scores of legitimate processes. Then, we obtained millions of legitimate stack traces of these processes and, using decision tree learning, built different models of “good” behavior. We also took malicious stack traces from various sources to provide bad examples.
Based on these millions of learning samples, patterns are developed. Using decision tree learning, we move from observations about an item to conclusions about the item's target value. The goal is to create a model that predicts the value of a target variable based on several input variables. Acronis experts use decision tree because we shouldn’t affect the performance of the client machine while collecting and sending the data and this algorithm allow us to achieve this goal.
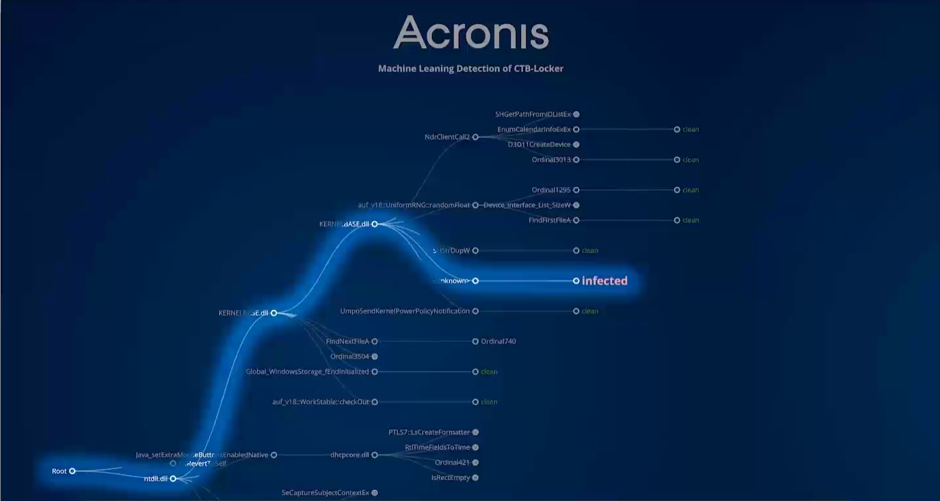
So when Machine Learning is activated in the actual product? As we already said, Acronis Active Protection is based on behavioral heuristics. In version 2.0 we added several new heuristics which are looking for legitimate processes. If Active Protection notices something strange is going on with a legitimate process, it takes a stack trace and sends it to our Machine Learning module, where the behavior is compared with existing models of clean and infected stack traces to determine if it’s a threat or not. If the behavior is confirmed to be malicious, the user gets an alert suggesting that he should block the ransomware-like process. As a result, Machine Learning also reduces any potential false positives as it acts like second authority for heuristics to make a final decision.
Example of Machine Learning-based detection of infamous ransomware family CTB-Locker.
New level of anti-ransomware defense
With Machine Learning leading the way, all of these technologies bring Acronis Active Protection to a whole new level, especially when it comes to zero-day threats. It creates a model of which processes are legitimate, so even if bad guys find a new vulnerability or way to infiltrate the system, Machine Learning will detect the ransomware’s processes and put a stop to them.
Machine learning models can be used to analyze scripts, and we are already working in this direction. NioGuard Security Lab performed a test that showed that most anti-virus solutions are unable to detect a script-based attack. Acronis Active Protection already performs much better compared to most other anti-malware solutions, but we are aiming to make our anti-ransomware technologies even better.
READ MORE:
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.




