It is a known fact that cybercriminals love to hijack global news headlines in order to spread their scams and increase their profits. We have seen this scare tactic reaching a new moral low recently when attackers threatened to deliberately infect people with the coronavirus.
The ethics and morals of cybercriminals are of course questionable. Recently some ransomware groups like Maze and DoppelPaymer promised that they would refrain from attacking healthcare organizations during the COVID-19 pandemic. This was far from a solid cease-fire and there have already been ransomware incidents by other groups, like Netwalker Ransomware, which clearly is not showing any signs of reluctance.
Coronavirus update of old attack scheme
The dynamic nature of cyberthreats means that attackers quickly adapt to new themes and techniques in order to maximize their profits. One of the most recent scams that got updated for the pandemic theme is the so-called sextortion scam emails.
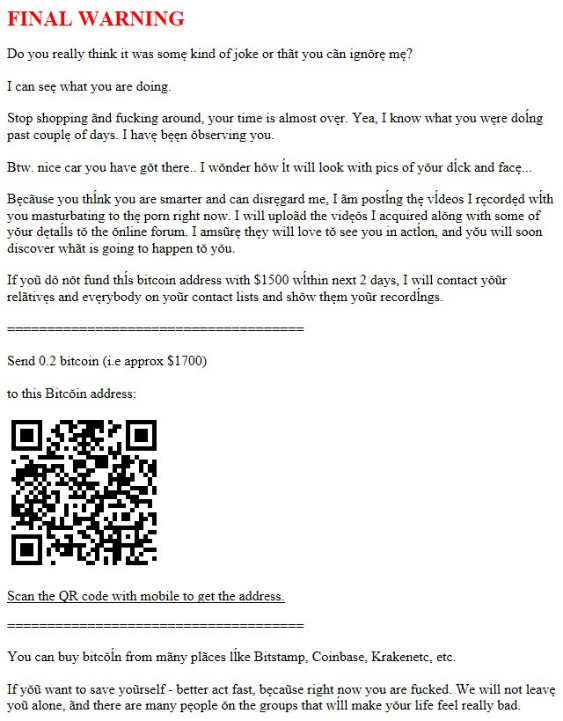
The classic variant of this scam claims that the criminals have compromised a user’s email account and now have full access over their digital life. The scammer claims that with this access they recorded a webcam video of the user visiting erotic web sites – followed-up by a typical blackmail approach, where the victim is asked to transfer bitcoins or the embarrassing video would be published to the internet.
Although such an attack would definitely be plausible, the attacker actually never compromised the user’s account: they just pretend. They convince the user by displaying an old password, one which was acquired from a past data breach that has been made public. From these available sources, they have access to email addresses and passwords, which helps in making a very convincing scam email.
Unfortunately, many people are still falling for this deception. The example of a sextortion attack shown below convinced eight people within four days to make a bitcoin payment. This accumulated 1.28 bitcoins for the cybercriminals, which is currently worth more than $10,000.
With thousands of such emails being circulated, you can imagine the possible profits for the attackers.
The new sextortion scam emails
We came across a new variation of these sextortion scams. The cybercriminals still use a previously leaked password as a convincing element, but instead of threatening to release a recorded video, they threaten the life of the user. The cybercriminals claim to know the exact location and daily routines of the victim. They further declare that they "… could even infect your whole family with the CoronaVirus…". To stop them from doing so, they demand that $4,000 in bitcoins be transferred.
It’s not the first time that scammers threaten the life of the user. In the past, we had seen examples where they threatened to send hooligans to beat the people up – but the COVID-19 threat brings it to a new level.
Fortunately, this is just a scam and we are not aware of any real-life incidents of this happening.
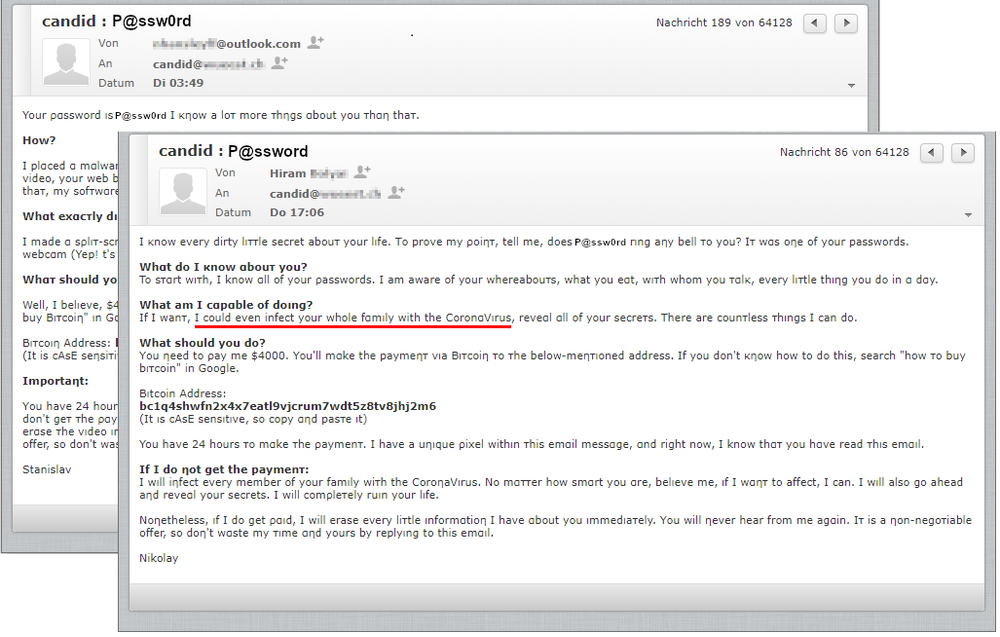
Most of these emails are sent from random spoofed email addresses or real email accounts that have been compromised where you might even know the person. Of course, the message itself should be a clear indication that it is a scam and that you can simply delete the email.
Unfortunately, the list of COVID-19 themed scams and malware grows every day. There are plenty of other COVID-19 themed email scams making their rounds at the moment. For example, we have seen charity scams that pretend to gather donations for the WHO and other scams making use of the work-from-home situation by posing as the IT department to get the user to install malicious software.
How to protect against scam emails
- Do not panic. Do not get scared by the crooks. They do not know you, nor do they have access to your computer. It is a classic scare technique. Try to ignore it, even if it sounds disturbing.
- Do not pay. Once you’ve paid money, you will not get it back. Instead, you might be attacked more frequently since you’ve shown the attacker that you are a profitable target.
- Use strong passwords. Use unique strong passwords for different services. If possible, enable multi-factor authentication in order to increase security. A password manager can help you remember all these different passwords.
- Awareness-training programs. As an organization, you should implement an awareness-training program for your employees. Also, make sure that your employees know how to report such scam emails to your IT department.
- Update all relevant systems. Ensure that all your systems are up-to-date and that you are using a comprehensive security solution that can automatically protect you from the newest cyberattacks.
Get your organization #CyberFit
Finally, consider upgrading your traditional backup regimen to cyber protection, which combines data protection with cybersecurity featuring behavioral endpoint anti-malware. This will provide you with a safety net against the most destructive and pervasive types of malware that commonly use email as an attack vector, such as ransomware. If someone in your organization falls for an email scam, coronavirus-themed or not, these defensive measures can save you from days or weeks of costly, business-threatening data loss and downtime.
Acronis can help. For more information on Acronis Security Services including Acronis Security Awareness training, visit us here. For more information on Acronis Cyber Backup with built-in, AI-enabled anti-ransomware, visit us here.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.



