Ransomware continues its reign as one of the most pervasive malware threats to assail businesses, government institutions and consumers in 2019, with new variants appearing almost daily. One particularly nasty new strain of ransomware, dubbed RobbinHood [sic], recently locked up critical IT systems and brought down corresponding public services in two North American cities: Greenville, NC and Baltimore, MD.
Government intelligence organizations confirm a recent trend of ransomware gangsters actively targeting regional and local governments as easy pickings. That’s because cities, counties and states are more likely to pay large extortion fees quickly to unlock their data and get constituent services back online with as little downtime as possible.
Additional examples of attacks on local government and municipal targets are plentiful, including Washington, PA; Stuart, FL; Imperial County, CA; Garfield County, UT; Albany, NY; Amarillo, TX; Del Rio, TX; Jackson County, GA; Leominster, MA; Cleveland (OH) Airport; Augusta (GA) City Center; and the School System of Taos, NM.
In fact, the notorious ransomware attack on the City of Atlanta, GA in 2018 still ranks among the costliest on a government target, with the city’s cleanup expenses eventually reaching $17 million.
Details about RobbinHood ransomware
The RobbinHood variant uses a few novel tactics to ratchet up the nastiness.
Unlike many virulent ransomware strains, it does not spread via worm capabilities, but carefully targets individual machines. Once it manages to infect a target (the actual attack vector remains a mystery for the moment), it shuts down nearly 200 different Windows services that are associated with antivirus, databases, mail services and other processes – anything that could keep a file open and prevent its encryption.
After locking the target’s files, RobbinHood presents a ransom note demanding payment of tens of thousands of dollars in return for the key to unlock them. To encourage swift payment, a late fee of $10,000 per day is added to the ransom starting four days after the attack.
Ransomware risks loss of reputation
Another wrinkle is an implied promise to keep the incident secret: the ransom note asserts that the attackers behind the RobbinHood strain care about the victim’s privacy and so promise to delete the victim’s IP addresses and encryption keys once the payment is made. This messaging is clearly designed to encourage victims to believe that quick payment will spare them the public embarrassment of having to disclose a security breach, and perhaps the need to pay regulatory fines for compliance violations.
The criminals behind RobbinHood seem to be playing on the fears that government officials have about what may happen to them if news of the attack is made public. Based on what’s happening in the private sector, that’s likely a strong motivation for public sector leaders.
Stopping RobbinHood ransomware
At the moment there is no way to reverse the effects of a successful RobbinHood attack without paying the ransom – and even then ransomware decryption keys only work about 50% of the time. The better approach is for organizations to be proactive in their protection strategy – taking precautions that will stop this and future ransomware strains that have yet to be seen.
If your organization is scrambling for a defense against ransomware threats like RobbinHood, Acronis can help. That’s because the company’s unique approach delivers easy-to-use and reliable cyber protection solutions for individuals, businesses and governmental agencies.
Keeping data, apps and systems secure
Acronis designs each of its solutions to address the Five Vectors of Cyber Protection – ensuring the safety, accessibility, privacy, authenticity and security of data (also called SAPAS).
In order to provide the security needed against the ever-evolving online threats cybercriminals are creating, Acronis integrates the industry’s first AI-powered anti-malware defense into its enterprise-grade Acronis Backup, used by businesses and government institutions, as well as its consumer product, Acronis True Image.
Called Acronis Active Protection, the built-in anti-ransomware software uses artificial intelligence and machine learning to automatically detect, terminate, and repair the damage from thousands of ransomware variants, including RobbinHood. And because its detection method is behavioral, it is more effective at stopping zero-day (previously unknown) ransomware attacks than signature-based anti-virus solutions. In fact, it successfully stopped 400,000 ransomware attacks last year.
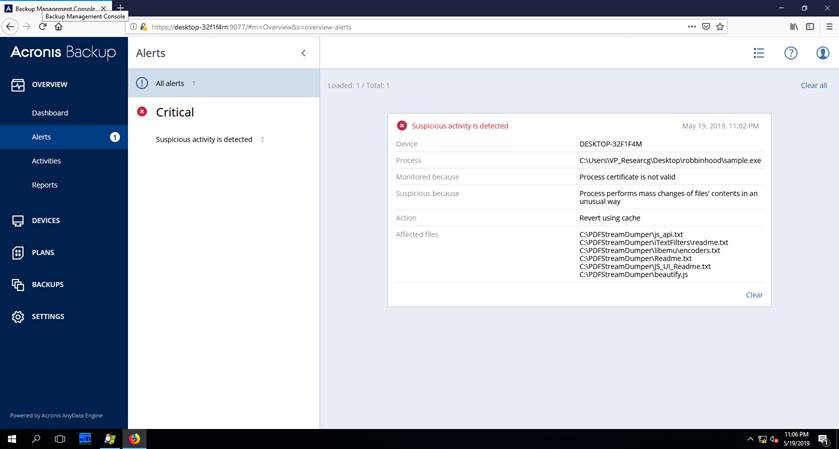
(Full disclosure: RobbinHood seems to have bragging rights on one tiny score. While Acronis Active Protection successfully detected and terminated the attack, RobbinHood managed to shut down the Acronis alerting function. This means that the RobbinHood infection was successfully stopped, but that fact went unnoticed until Acronis backup logs were examined later. That’s a minor issue we will fix in a forthcoming release.)
Final thought
RobbinHood may be today’s malicious headline-grabber, but cybercriminals are constantly developing new ransomware variants to evade user defenses. Conventional anti-virus solutions may catch some older strains, but it is increasingly clear that such signature-based countermeasures are losing the race.
Regular patching of operating systems and applications – along with a rigorous, frequent backup regimen – can help mitigate the effects of an attack to some extent. For a proactive cyber protection stance, however, organizations need to stay ahead of ransomware attacks by adopting AI- and ML-enabled behavioral defenses that identify threats by their actions, not their appearance.
Your best defense against RobbinHood ransomware and whatever new versions are eventually thrown your way is Acronis Active Protection.
To try it yourself, get a complimentary 30-day trial of either Acronis Backup or Acronis True Image. Or if you're already a user, just remember that while Acronis Active Protection is active by default in Acronis True Image, for those businesses using Acronis Backup, you need to enable the feature.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.



