Acronis is recognized by
Why Acronis Cyber Protect Cloud
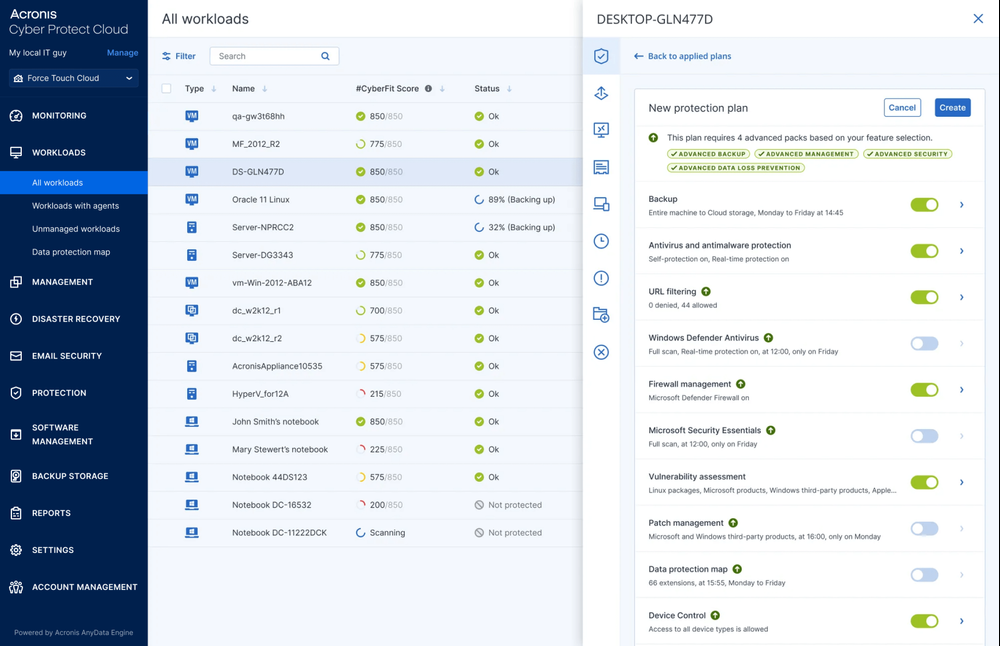
Increased Control
Reduce complexity and control the services you deliver for your customers: security, backup, disaster recovery, endpoint management, automation. All with the flick of a switch
Vendor Consolidation
Managing multiple vendors leads to increased costs, greater risk, and added operational overhead. Consolidate your vendors and increase efficiency of service delivery to your clients.
Centralized Management & Monitoring
Efficiently manage and monitor your clients through a single console, giving you better and more effective control over their cyber protection.
World Class Partner Support
Drive your business with pre-packaged marketing campaigns, training, and other resources, available through the Acronis Partner Portal.
Reduced Training Time
By delivering client services through a single console, you can reduce training time for new technicians by up to 50%, and allow them to focus more time on driving business.
Liberty Technology switches from Cisco Secure Endpoint to Acronis
“Acronis has drastically cut the time it takes to complete tickets. Remediation is quicker, and we no longer need multiple techs to investigate the same cyberevent because Acronis EDR shows me exactly how it got there within the kill chain.”
Unique capabilities designed for modern cyber protection
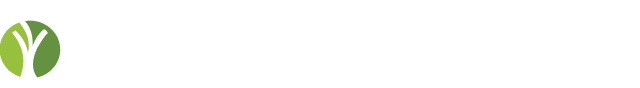
View all featuresAnti-malware
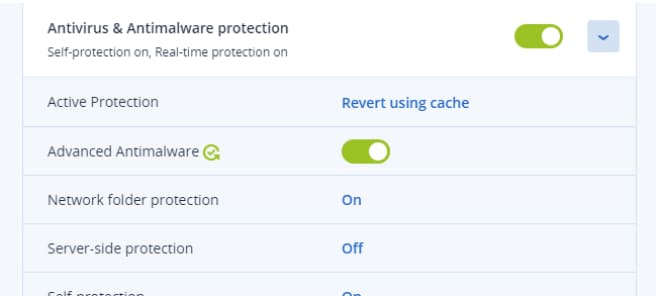
Proactively protect your clients’ systems from advanced cyberattacks in real-time with AI-based static and behavioral heuristic antivirus, anti-malware, and anti-ransomware technologies.
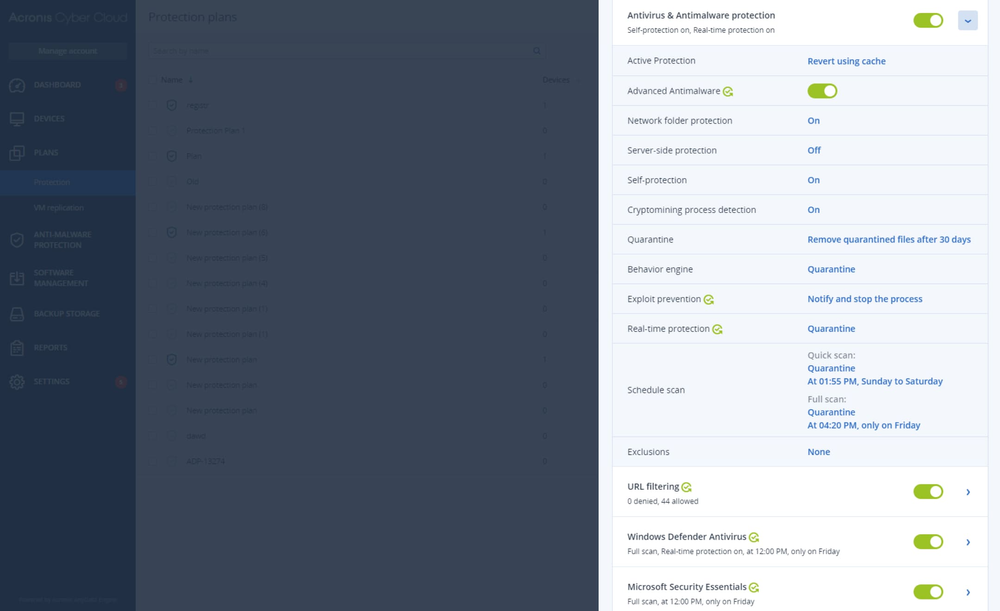
Fail-safe patching
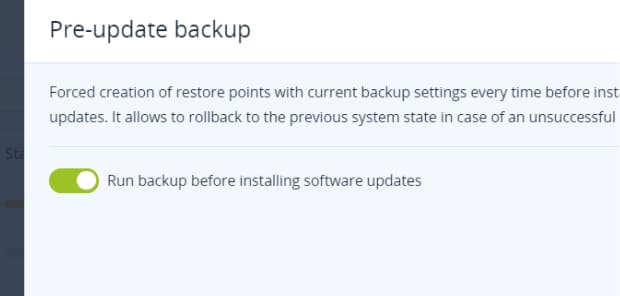
Eliminate the risk of bad patches rendering a system unusable. Before a patch is applied, an image backup is automatically created, enabling you to easily restore to a working state.
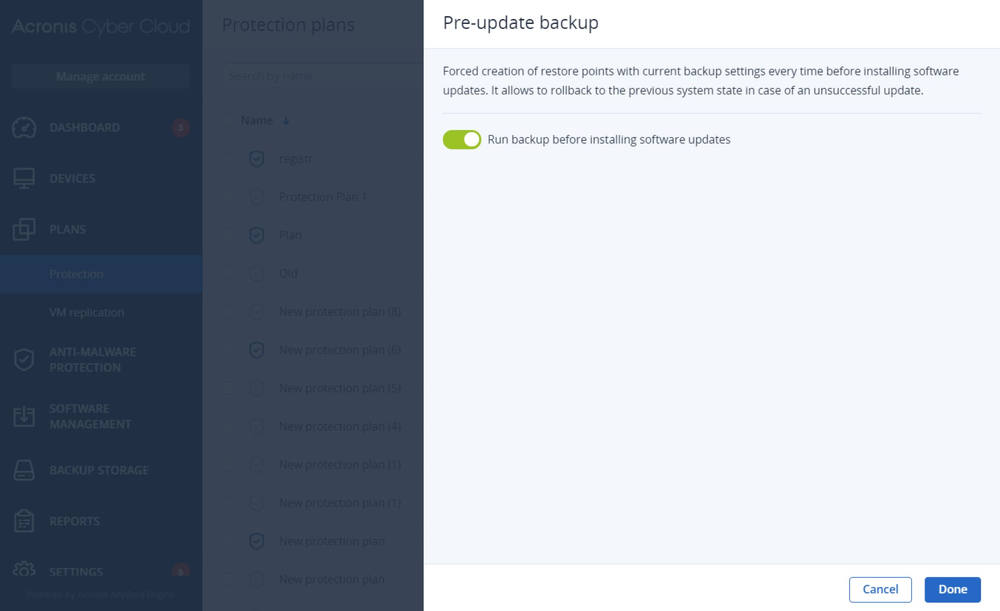
Forensic backup
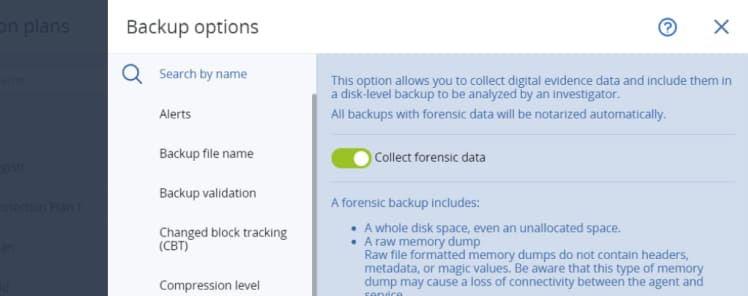
Simplify future analysis by collecting digital evidence from disk-level backups. Enables clients’ to manage their compliance requirements and run faster internal investigations.
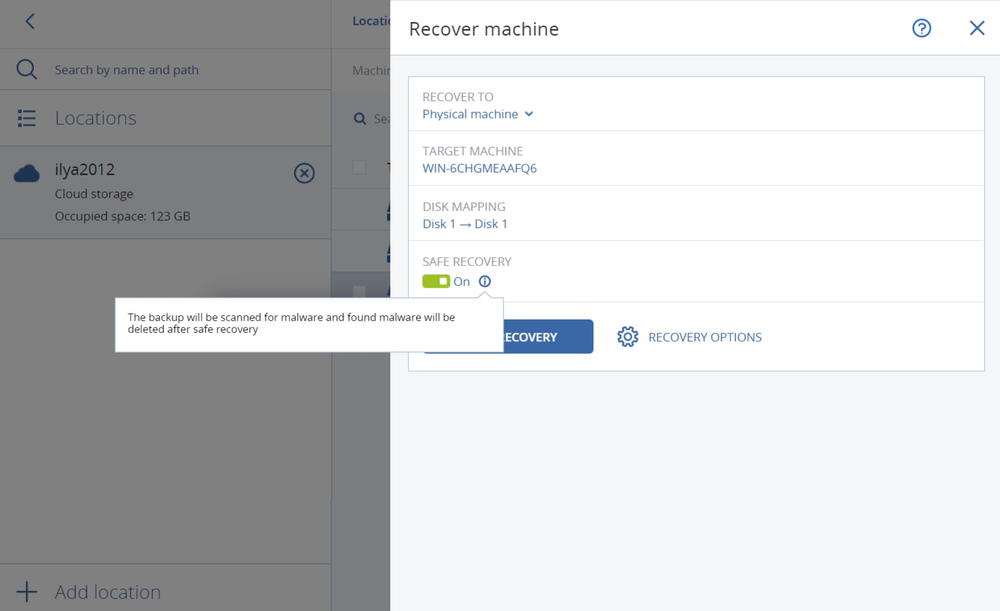
Safe recovery
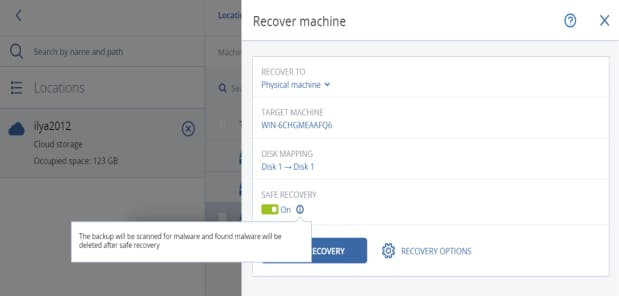
Avoid malware reinfection by automatically patching the machine and then scanning your system and backup images using the latest anti-malware definitions.
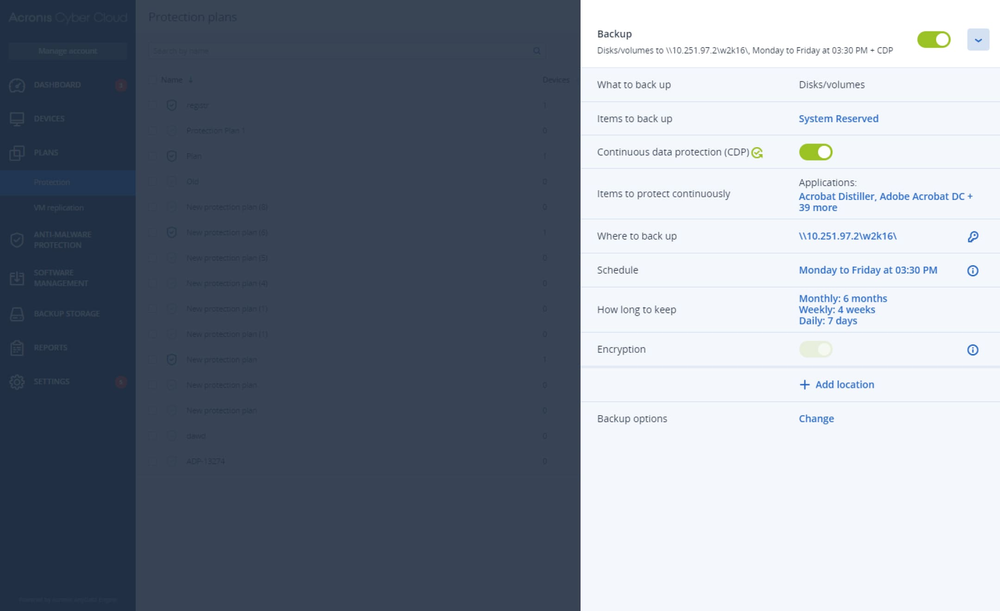
Continuous data protection
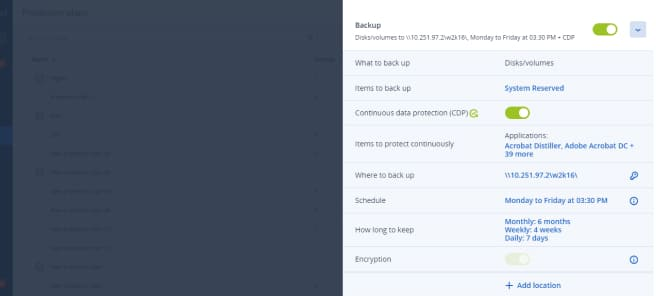
Safeguard critical data. Acronis’ agent continuously backs up listed applications so recent changes aren’t lost if the machine needs to be reimaged.
Unleash more potential with services
Gain advantage over competitors with industry-unique cyber protection capabilities, minimizing security risks and reducing management burdens.

Upcoming events
Our top prevention resources
Frequently asked questions
- Does Acronis Cyber Protect Cloud provide all-in-one solution for MSPs?Acronis Cyber Protect Cloud is the industry-first solution that unites cybersecurity, data protection, and endpoint management in one integrated solution – with one agent and a single management console. In addition to greatly reducing the resources needed to operate because it consolidates multiple solutions, it creates easy upsell and cross-sell opportunities for increased profitability.
Acronis Cyber Protect Cloud is easy to deploy with automatic machine discovery and remote agent installation. It reduces the administrative burden with centralized, group, and multi-tenant management and built-in secure remote connections for assistance.
Service providers can track and plan their work much more efficiently with hardware inventory collection, change tracking, vulnerability assessments, and centralized monitoring and reporting via a single pane-of-glass.
It greatly eases daily service providers tasks thanks to integrations with most common RMM and PSA tools, hosting control panels and billing systems, and marketplace providers such as Autotask, ConnectWise (Automate, Manage, Control), Kaseya, Atera, Plesk, cPanel, CloudBlue, and AppDirect.
Moreover, service providers can turn themselves into value-added resellers and sell beyond the end-customer market with reseller management.
- Is cloud storage better than local storage for backup as a service (BaaS)?Depending on your client, they may have a preference on whether they want to store their data locally or in the cloud. Acronis offers service providers the option to back up to cloud storage hosted by Acronis, Google or Microsoft, their own cloud storage, or local networked storage. Supports more than 25 platforms, including Microsoft SQL clusters, Microsoft Exchange clusters, Oracle DB, and SAP HANA, which are supported in the Backup add-on for Acronis Cyber Protect Cloud.
- What is a cloud-based disaster recovery solution?A cloud-based disaster recovery solution is an offsite recovery option that ensures high-availability of business-critical data by quickly restoring workloads after natural disasters, human error, cyberattacks, or hardware or server failures. Disaster Recovery for Acronis Cyber Protect Cloud provides an all-in-one backup and disaster recovery solution to help service providers minimize complexity while growing their margins.
- Does Acronis Cyber Protect Cloud include endpoint protection?Acronis Cyber Protect Cloud includes best-of-breed anti-ransomware technology, strengthened with AI- and behavior-based detection focused on zero-day attacks. It also provides essential data loss prevention through device control.
Both the Acronis Cyber Protect Cloud agent and backups are protected by our comprehensive self-defense technology that prevents tampering.
The Security + XDR add-on extends endpoint protection with full-stack anti-malware to prevent a wider scope of threats, including web-based attacks and exploitation techniques. It increases the speed and accuracy of detection while ensuring zero-false positives. All collaborative applications benefit from prioritized protection, preventing exploitation of their processes. For more aggressive scanning, the anti-malware scans in the Acronis Cloud reduce the load on endpoints while ensuring no threat can reoccur.
Acronis Cyber Protect Cloud with Security also eases remediation and makes security investigations less costly by collecting digital forensic evidence and storing them in backups.
- Does Acronis Cyber Protect Cloud contain a patch management solution?Acronis Cyber Protect Cloud provides vulnerability assessment technology to properly identify security gaps before they pose a serious threat to the IT environment.
The Management add-on helps map the vulnerability assessment process to patch management for prioritized patching based on criticality. It also reduces the service provider’s management burden with patch management automation and fail-safe patching technology, which automatically backs up the system before a patch is applied to enable easy rollback in case the update renders the system unstable.
Acronis enables you to deliver add-on services to your clients
Strengthen your cyber protection services with Acronis!
Sorry, your browser is not supported.
It seems that our new website is incompatible with your current browser's version. Don’t worry, this is easily fixed! To view our complete website, simply update your browser now or continue anyway.