Cyberthreat intelligence and monitoring
Cyber threat intelligence and monitoring are critical to stopping a modern cyberattack. Still, many organizations do not have the staff, expertise, or budget to collect, process, and analyze the information required to stop attacks. Without access to the most up-to-date cyber threat intelligence, your organization is more likely to suffer an attack.
This article discusses cyberthreat intelligence, how intelligence is developed, the types of intelligence available to different audiences, and the alternatives available to any organization that cannot take on an in-house cyberthreat intelligence program.
What is cyberthreat intelligence and monitoring?
"Threat intelligence is evidence-based knowledge, including context, mechanisms, indicators, implications and actionable advice, about an existing or emerging menace or hazard to assets that can be used to inform decisions regarding the subject's response to that menace or hazard." ― Gartner
Cyberthreat intelligence (CTI) is actionable data collected and used by cybersecurity systems and / or an organization’s security experts to help them better understand vulnerabilities, take appropriate action to stop an attack, and protect the company’s network and endpoints from future attacks. The data includes information such as who the attacker is and what their capabilities, motivations and attack plans are.
Cyberthreat monitoring is a solution that uses strategic intelligence to continuously analyze, evaluate and monitor an organization’s networks and endpoints for evidence of security threats, such as network intrusion, ransomware and other malware attacks. Once a threat is identified, the threat monitoring software issues an alert and stops it.
Why is cyberthreat intelligence important?
You cannot reliably stop any cyberattack without a detailed threat report. In the age of remote work, where employees are using BYOD devices and unprotected networks, CTI is more important than ever. With threat intelligence and monitoring, an organization has the most robust data protection and information necessary to stop or mitigate cyberattacks. CTI provides:
· Insight into the data ― including context ― to help prevent and detect attacks
· Prioritized alerts, which help you respond faster to incidents
· Improved communication, planning, and investment by identifying the real risks to the business.
Who can benefit from cyberthreat intelligence?
Organizations, large and small, governments, and nation-states can benefit from CTI. However, few organizations have analysts on staff to work through the volume of information and make decisions on what data is valid and what threats are real. Experts have estimated that it would take 8,774 analysts working full-time for one year to process the same amount of security event data that machine learning (ML) can process in the same timeframe.
This is why many organizations look to artificial intelligence (AI) and machine learning to analyze the tactical and operational threat intelligence needed for timely detection and incident response to satisfy a sensible security posture.
Cyberthreat intelligence lifecycle and process
Industry experts state that there are five or six iterative process steps to the cyber threat intelligence lifecycle, which turns raw data into intelligence. The CIA first developed a six-step lifecycle process, while other security experts have combined and condensed the lifecycle process down to five steps as follows:
Cyberthreat intelligence lifecycle ― planning, collection, processing, analysis, dissemination
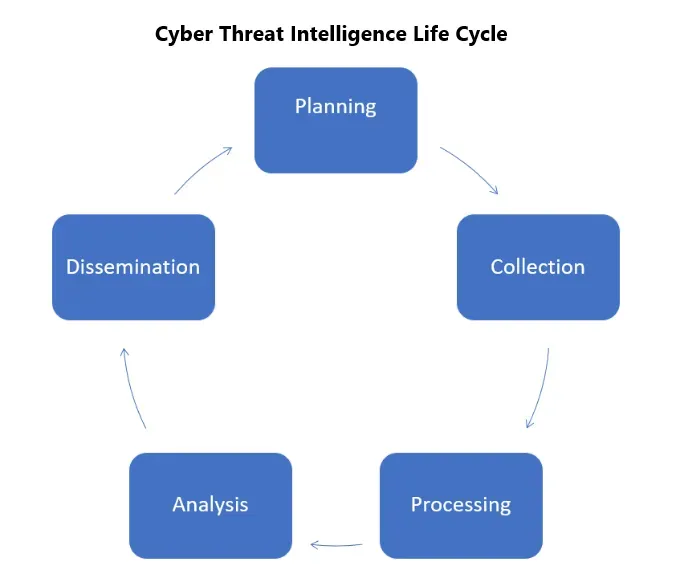
1. Planning and direction. In this phase, the CISO or CSO sets the goals and objectives of the cyberthreat intelligence program. This includes identifying the sensitive information and business processes that need to be protected, the security operations required to protect the data and the business processes, and prioritizing what to protect.
2. Collection. Data is gathered from multiple sources, such as open-source feeds, in-house threat intelligence, vertical communities, commercial services, and dark web intelligence.
3. Processing. The collected data is then processed into a suitable format for further analysis.
4. Analysis. In this step, the data is combined from different sources and transformed into actionable intelligence so that analysts can identify patterns and make informed decisions.
5. Dissemination. The threat data analysis is then published appropriately and disseminated to the company’s stakeholders or customers.
We refer to the process as a "cyberthreat intelligence cycle" because tackling digital attacks is not a one-and-done process but a circular process that takes each cyber experience and applies it to the next.
What is cyberthreat modeling?
Cyberthreat modeling is a practice designed to optimize network security. It does so by locating system vulnerabilities, identifying clear objectives, and developing a strategy to counter the potential effects of cyberattacks against an application or a computer system.
While it can be executed at any development stage, it bears the most fruit if completed at the start of a project. The logic is as follows ― the sooner you identify new vulnerabilities, the easier it will be to deal with them. On the other hand, if weak points remain unattended, they may turn into serious security issues down the road.
The approach enables your IT team to dive deep into the potential dangers to your system and how they can impact your network. Cybersecurity professionals can use the practice to fortify all potential entry points, apply application security in line with potential weak spots, and protect internet-of-things environments.
The threat modeling procedure depends on the examined system. Nonetheless, any tech-dependent organization can benefit from it. Threat modeling enables security professionals to narrow down the particular hits targeting a specific system. This eliminates potential confusion and enables teams to focus only on the ones capable of affecting your business. Packed with such knowledge, your security team could defend the company system long before an attack impacts it.
However, threat modeling requires a thorough process to optimize your cyberdefenses up to their teeth. In the next section, we will discuss the needed steps for threat modeling to benefit your business the most. All of them can “act” individually as they’re independent processes. Nevertheless, executing them together provides the most comprehensive view of any potentially damaging scenario.
Let’s go over the steps now.
Steps for comprehensive threat modeling
The steps for robust threat modeling can be simplified to preparation, examination, implementation, and review. However, all of those depend on a series of questions to work optimally.
Below is a list of questions threat hunters must ask before concluding a final threat model.
· What threat models are best suited to your company?
Answering this question requires inspecting data flow transitions, data classifications, and architecture diagrams to arrive at a virtual network model in need of protection.
· What are the drawbacks?
For this one, you must research the major threats to your network and apps.
· What to do in the face of a potential cyberattack?
For this question, you’d need to identify the best way to counteract specific vulnerability issues and scenarios in which threat actors exploit those vulnerabilities.
· How is the threat model performing?
Companies must follow up on counterattack processes to determine their quality, efficiency, and feasibility. Conducting a thorough review of the model’s performance could catalyze a better planning process and quicken your progress.
To comprise the questions into a list of steps, you can check out the list below.
1. Outline the security concerns of a specific system, app, or process.
2. Make a list of suggestions for potential threats that need to be verified as the conditions change over time.
3. Form a concrete list of threats.
4. Form a list of remediation and elimination actions.
5. Monitor and grade the methods in use to determine their success rate and validity as the threats evolve.
Now that you’re familiar with the basic outlines of threat modeling, let’s go over the threat modeling process in a bit more depth.
The threat modeling process
As we’ve mentioned, threat modeling can define an organization’s assets, pinpoint applications’ role in the bigger picture, and comprise a security profile for specific applications.
The process proceeds to identify and prioritize potential threats. Afterward, security professionals can use the gathered data (and conclusions) to classify potentially harmful events and determine what actions could be taken to resolve issues.
In essence, threat modeling is taking a step back to access a company’s digital and network assets, pinpoint external and insider threats, determine existing malicious indicators, and devise a plan to protect against them (or to recover sensitive information securely if a threat manages to penetrate company defenses).
In the same way a "kill chain" outlines the structure of an attack in the military, you can create a "cyber kill chain" to understand how attackers think and counter them proactively.
Below, we’ll break down the threat modeling process into additional steps so you can follow them more easily.
Keep in mind ― every individual process is unique depending on the network, company preferences, and arising issues. However, the basic approach remains somewhat concrete.
1. Create a secure design, network model, or application defense system.
2. Ensure that resources are invested as efficiently as possible to avoid unnecessary spending (be it in the form of more money or as more people assigned to do a task).
3. Make security a top priority. In most cases, robust security outweighs short-term profitability, as a secured system will bring more profits in the long run (and will guard them effectively as long as it’s operational).
4. Inform stakeholders of the system’s development.
5. Specify all potential system threats.
6. Identify compliance requirements in line with the specific system or application being addressed.
7. Ensure that all measures taken comply with the needed regulations.
8. Define the necessary controls to counter cybercriminals before, during, and after potential attacks.
9. Build said controls and present them transparently to all stakeholders.
10. Assess all risks connected to the threat management system.
11. Document impactful threats for the system.
12. Document mitigation efforts applied to counter various threats.
13. Ensure that the company’s goals are not impacted by ill-intended actors or adverse events.
14. Test the system to ensure its workability in the face of indicators of compromise to protect your company’s network.
15. Build on the foundations you’ve created until you complete a comprehensive security plan for your specific use case.
Advantages of threat modeling to mitigate the effect of cyberthreats
As challenging as threat modeling may sound, it significantly benefits companies implementing it correctly.
For example, the approach can provide a comprehensive view of software projects and point out the needed security measures to protect the data in said projects. With it, you can document known security threats (to the application) and take the needed actions to address them adequately. Otherwise, if your IT teams are acting on pure instinct without supporting evidence, they may not be able to make the most optimal decisions regarding your data’s safety.
Well-designed threat models can ensure that an application on your network is secured against all known cyberthreats. Additionally, realistic threat modeling can turn out to be the most efficient way to fulfill a list of practical tasks for your business.
Let’s go over them below.
· Detect issues in the software development life cycle (SDLC) before any coding work has started.
· Pinpoint slippery design flaws, otherwise undetectable by traditional testing methods and code reviews.
· Evaluate an expansive list of threats you might miss considering otherwise.
· Optimize testing budgets.
· Identify data protection and security requirements.
· Remediate software issues before app release, thus preventing additional costs spent for recoding post deployment.
· Consider exotic threats specific to the unique nature of your application.
· Keep a clear view of potential external and insider threats to the specific application.
· Pinpoint assets, vulnerabilities, malicious agents and the needed controls to optimize application components (to reduce the potential attack surface for malicious actors).
· Calculate and set a potential location of hackers, skills, motivations and capabilities to understand and locate potential cyberattackers targeting your system architecture.
Misconceptions about the cybersecurity aspects of threat modeling
The term “threat modeling” raises several misconceptions for many users. Some of them perceive that the approach can only be applied when designing an application. Others consider it an optional task, easily substituted by code review and penetration testing. There are also companies that see the process simply as an overcomplicated, redundant activity.
Below, we will examine these misconceptions to give you a clearer idea.
· Code review and penetration testing aren’t substitutes for threat modeling
Code review and penetration testing are effective when finding bugs in the code; they’re a fundamental part of any application development process. However, with threat modeling, you can initiate dedicated security assessments and uncover complex design flaws that, if left unfixed, may invite security breaches.
· Threat modeling can be conducted post deployment as well
As we’ve mentioned, it’s best to initiate threat modeling at the start of the design stage. Nonetheless, that doesn’t mean you shouldn’t turn to the approach post deployment, too.
As an application becomes more accessible post-deployment, new cyberthreats may arise. Without a threat assessment of all current threats to an application, you can’t secure it against all potential risks. By monitoring weaknesses in the post-deployment stage, you enable quicker and more effective remediation for the application.
· Threat modeling isn’t a complicated process if approached sensibly
Plenty of developers find threat modeling to be challenging. The process seems time consuming and tiresome when examined before a plan has been laid out. However, you can divide it into workable tasks classified into systematic steps. Each task follows the previous one, so as long as you follow the “script,” you can complete threat modeling without much hassle. Be it regarding a simple web app or complex architecture.
Threat modeling techniques for security teams
Decomposition is a fundamental part of the threat modeling process. Here, the term refers to taking an application or infrastructure, breaking it down into elements, and then taking each element to inspect it against potential weaknesses.
By decomposing, you can understand how an application works and interacts with all system entities. Furthermore, you can determine which entities can pose cybersecurity threats or invoke issues for the application.
To complete a decomposition process, you need to study the application’s (or system’s) behavior within the context of as many different scenarios as possible. Such cases may include:
· How the application behaves for users with different access levels?
· How does it behave while connected to various network architectures?
· How the system processes different data types?
After answering the questions above, you should have a comprehensive list of potential entry points and weak spots and, more importantly, understand how these change, depending on a specific interaction.
To ease their work process, IT teams should rely on diagrams outlining the data flow. This way, they can actually see a visual representation of data movement within, through and out of a system (or an application).
Diagrams could also show how data changes at different processing or storage stages. Lastly, diagrams display where you store specific data as it moves across the system.
Data flow diagrams also enable teams to identify trust boundaries. Essentially, teams should be able to determine the points at which data must be validated before it can be allowed to enter a specific entity (that will use said data to conduct tasks).
Data should be able to flow wherever it needs to be processed (local servers, the cloud, secondary-location storage).
Regardless of the destination, data will enter different networks. Data flow diagrams should outline the precise moment when sensitive information crosses over from one network to another. Once the intersection points have been set, your teams can set up trust boundaries at particular locations. This will alert security protocols to enact protection procedures to secure the network against malicious code should a hacker attempt to penetrate your defenses.
Threat modeling approaches
Now that you’re familiar with the basic practices, let’s explore specific approaches to the process.

STRIDE
The first methodology on the list is developed by Microsoft, and it aids IT teams in identifying system weaknesses in six categories.
Spoofing ― when an intruder poses as a different user, component, or another system feature containing an identity in the targeted system.
Tampering ― altering data within an application or a system to enable malicious actions.
Repudiation ― when an intruder denies performing a malicious activity due to insufficient proof of their actions.
Information disclosure ― the exposure of protected data to otherwise unauthorized users.
Denial of service ― when an attacker uses illegitimate means to exhaust or deny services required to provide service to users.
Elevation of privilege ― when an intruder executes commands and functions, they shouldn’t be allowed to.
DREAD
Microsoft dropped this approach in 2008 due to inconsistencies found. However, many other organizations currently use it. In essence, it enables ranking and risk management in five categories.
Damage potential ― ranking the damage extent made possible due to an exploited weakness.
Reproducibility ― ranking the complexity needed to reproduce an attack.
Exploitability ― assigning a numerical rating to efforts needed to launch a malicious attack.
Affected users ― presenting a value to calculate how many users would be impacted if an exploit is made widely available.
Discoverability ― measuring the ease of discovering a specific exploit.
Trike
Trike presents an open-source intelligence network aimed at defending a system rather than attempting to replicate how hackers can attack it. With Trike, you can make a model of an application or system and rely on the CRUD acronym to determine who can access specific system actions.
The actions are as follows: create data, read data, update data and delete data.
Using the data from CRUD, IT teams can assign risk levels to different asset classes. They can identify weak links, assign risk values to them, and then build a risk model comprising assets, actions, roles, and calculated risk exposure.
P.A.S.T.A.
P.A.S.T.A. stands for “Process for Attack Simulation and Threat Analysis.” It’s a seven-step methodology focused on risk management.
With it, your teams can access dynamic threat identification, classification, and scoring processes. Once they apply structured analytical techniques to inspect known exploits, developers can implement the tactical intelligence to an asset-centric mitigation approach since they can “see” the application (or system) through the eyes of the attackers.
P.A.S.T.A. follows seven steps to complete its course:
1. Defining objectives
2. Defining the technical scope of the project
3. Decomposition
4. Analysis
5. Weaknesses analysis
6. Attack modeling
7. Risk and impact on the business analysis
Attack tree
Here, teams can build a conceptual diagram to show how assets (or targets) could be attacked in a tree-like fashion. The diagram supports a root node, with children nodes and leaves being gradually added.
The child nodes represent conditions to meet to make the (direct) parent node true. Each parent node is satisfied exclusively by its direct child nodes. It also includes “AND” and “OR” options to represent alternative steps available to achieve specific goals.
VAST
A foundational element of ThreatModeler, VAST stands for “Visual, Agile, and Simple Threat modeling.” The approach provides tactical intelligence for the specific needs of application architects, developers, cyber security teams, etc.
In essence, VAST strives to offer a unique application and infrastructure visualization plan to ease all individuals involved with an application’s creation. It can do so by presenting a model that doesn’t require any specialized security expertise to be viewed and understood.
Common Vulnerability Scoring System (CVSS)
CVSS strives to capture the principal characteristics of a vulnerability and show its severity via a numerical score. The score ranges from 0-10, with 10 being the most severe.
The security teams involved can then translate the score into a quantitative representation ― low, medium, high or critical.
Such a representation should help companies to assess unique vulnerabilities and optimize their vulnerability management process effectively.
OCTAVE
An approach designed by Carnegie Mellon University, OCTAVE stands for “Operationally Critical Threat Asset and Vulnerability Evaluation.” It’s a risk-based assessment and planning strategy. It emphasizes organizational risk assessment without addressing technological risks.
The approach comprises three phases:
1. Organization evaluation ― security teams should build asset-based threat profiles here.
2. Information infrastructure evaluation ― here, you need to identify the weak spots in your infrastructure.
3. Evaluation of potential risks to the organization’s critical assets and decision making here, you should develop and plan a comprehensive security strategy.
T-MAP
T-MAP is majorly aimed at Commercial off-the-shelf (COTS) systems. It is used to calculate attack path weights. The created model comprises UML diagrams with values in four categories: access class, target assets, vulnerability and affected value.
Quantitative threat modeling method
Here, we have a complex approach comprising STRIDE, attack trees and CVSS. The method oversees several pressing issues for cyber-physical systems. Such systems typically contain complex independencies for their components, so it’s best to address such a hybrid environment with a hybrid methodology.
Firstly, you can build components attack trees for all STRIDE categories. The trees should illustrate the dependencies in all attack categories, as well as the values for low-level component attributes.
Afterward, you should apply the CVSS tactic to calculate the scores corresponding to the tree’s components.
NIST
NIST stands for the National Institute of Standards and Technology. The Institute has developed a threat modeling system that focuses primarily on data. It suggests four stages of action:
1. First, you need to identify the system, and outline how it works, including how it manages data (this includes data within the system and data the system is dependent on).
2. Ascertain applicable attack paths addressed by the model.
3. Conclude on necessary security operations to counter cyberthreats.
4. Analyze the created model to determine its effectiveness.
What are the six steps of threat modeling?
Threat modeling can be broken down into two primary processes ― Discovery and Implementation.
These processes can then be divided into three subprocesses each.
- Discovery
This is the process where cybersecurity professionals identify critical infrastructure and the issues surrounding it.
They also use tactical intelligence to determine possible paths hackers may use to attempt infiltration.
- Implementation
This process relies on the strategic intelligence gathered in the discovery phase. Cybersecurity professionals can analyze the data to determine organizational and repetitional impact, prioritize the most damaging attacks, and calculate the needed steps to fortify assets alongside the prioritized paths for said attacks.
Discovery
The discovery phase comprises three crucial steps ― locating the most sensitive information assets and prioritizing them to complete a comprehensive risk assessment regarding your digital environment.
1. Identification of assets
First, you must catalog all company assets; those include data, apps, network components, etc. You can divide the assets into two primary categories.
· Data assets
Data assets comprise data, components, and functions that hackers can use to penetrate your system. For example, hackers can exploit various data assets to “assist” their cryptomining operations or harvest customer data to sell on the dark web.
· Business assets
Here, you’ll place data, components, and applications vital for the continued operations of your organization. Cybercriminals targeting your business assets could be related to ongoing sabotage campaigns to disrupt your business activity.
Some assets would fall into both categories. For them, the best practice is to catalog them comprehensively rather than strictly define them.
2. Analyzing the attack surface
Most modern hackers won’t go through the trouble of customizing attacks to target your business. You can view them as opportunists locked on any system's most direct entry points. Their prime goal is to exploit already known vulnerabilities to compromise or steal sensitive data.
The primary exploits within most companies are compromised hardware, software, and unprotected admin accounts (those still equipped with their default passwords).
Hackers can go through all three entry points until they find an exploit and carry out an attack.
To counter that, businesses should map out the environmental components surrounding the abovementioned assets. Keep in mind, the process includes not only the primary components but also those with any access to them (be it communication or containment).
Once the map is complete, you’d have a thorough plan of your attack surface. The attack surface comprises the exposed components that enable a malicious actor to access your assets.
Security specialists should outline all elements on the attack surface, calculate data flow, and demonstrate how an attack may penetrate through one (or more) of the components.
3. Analyzing the attack vectors
Attack surface refers to the plane of exposed asset-related components. Attack vectors are the different paths criminals can take to arrive at one of the weak spots on the plane.
You should map all components and their available functionality to include security applications and controls. Typically, hackers could use multiple ways to exploit a specific path.
Afterward, you should collect all relevant data regarding known exploits corresponding to each component in the list.
Now that you’ve got all the information, you need to try and think like a hacker. It’s up to your security teams to outline the hacker’s approach to launching an attack based on the collected information on weak spots. Here, consider everything you can think of ― their objectives, motivations, hacking skill levels, ability to monetize their efforts, etc.
Once that’s done, you should be able to assess how a potential hacker may attempt to infiltrate your systems.
Implementation
Having all the data from discovery is nice and all, but it needs to undergo comprehensive analysis to benefit you to the fullest. First, you’ll need to break down the impact of each attack vector, then prioritize their potential effects on the whole company, and ― lastly ― build a complete instructions list on vulnerability mitigation regarding every possible issue.
4. Comprehensive analysis
Risk assessment and management are the pillars of cybersecurity best practices for this step. They enable you to ensure you’re taking the best possible measures to mitigate risks and secure your resources.
Here, you can use all the data from discovery to assess each attack’s expected impact. It’s best to include any deductions made in the discovery phase and all threat intelligence and indicators of compromise.
As cyberattacks typically trigger a chain of events, it’s critical to go through all potential milestones and determine the various ways an attack may damage your company. You can follow the below list to ease your analysis phase:
· Data breaches resulting in leaked data regarding all involved parties
· Enhanced costs to replace any compromised equipment
· Damage to your company’s reputation among consumers and competitors
· Any legal actions taken due to a successful attack
· Overall business downtime following crucial components sabotage
5. Prioritization
As you’ve probably noticed, each step relies on the previous one to gather information and improve your critical security strategy.
In step 5, your goal is to prioritize all the previously discovered weak spots. As it’s nearly impossible to eliminate the risk of all potential threats, your cybersecurity specialists should focus on protection against the most fearsome, highest-impact threats.
Realizing the potential occurrence of a high-impact attack is a fundamental part of any risk management process. However, calculating the impact of such attacks outweighs their occurrence potential.
Following best practices, you could mitigate most (or all?!) critical exploits and counter as many additional issues as possible, depending on their standing in your impact-assessment list.
6. Enforcing security controls
The last step revolves around security controls. Such controls should effectively counter, remove, or mitigate all exposed vulnerabilities.
Here, it’s critical to analyze existing security operations to enforce continuous improvements. In doing so, you may pinpoint additional security gaps missed in the initial discovery phase.
Lastly, a complete security model should be viewed as a living element of your infrastructure. Even after you’ve gone through all creation steps, monitoring performance and applying security validation to ensure continuous security for your assets is crucial.
Why do we need to have threat information? What is it used for?
Why has cybersecurity become a fundamental part of information technology?
Let’s examine current cybercrime statistics instead of diving into a philosophical dispute.
According to an UpCity study, U.S. businesses reported over $6.9 billion in losses in 2021 due to cybercrimes. “Only 43% of those businesses feel financially prepared to face a cyberattack in 2022.”
Since 2016, Business Email Compromise attacks have generated $43.31 billion in spoils for cyberattackers, according to the FBI’s Internet Crime Complaint Center (IC3)
According to the Cybersecurity Ventures Almanac, cybercrime is so persistent that it’s estimated to cost organizations and individuals globally $10.5 trillion annually by 2025.
The above numbers may seem more relevant to big businesses and government institutions, but individual users may also fall victim to data breaches.
According to a Proofpoint report, cybercriminals increasingly target mobile devices, as smartphones are a gateway to personal details and login information. Following a successful attack, hackers can hold your sensitive data hostage to extort money or sell it on the black market.
As social engineering campaigns don’t intend to slow down, smishing attempts have more than doubled in the U.S. over the past year. In the U.K., over half of the attacks were designed around delivery notifications. Additionally, cybercriminals rained down over 100,000 telephone-oriented attacks per day.
Cybercrime is an all-evolving presence in the modern technology and communication landscape. Digital marauders can threaten data in various ways, so businesses and individuals should rely on best practices in cybersecurity to mitigate the risk of losing their data to a cyberattack.
What are the five threat levels for potential cyberattacks?
Threat levels are designed to indicate the likelihood of a cyberattack. They go as follows:
- Low ― a cyberattack is highly unlikely to occur
- Moderate ― a cyberattack is possible but not likely to occur
- Substantial ― a cyberattack is likely to occur
- Severe ― a cyberattack is highly likely to occur
- Critical ― an attack is highly likely to occur in the near future
Types of threat intelligence and monitoring
Depending upon the requirements and audience, there are three categories or types of cyberthreat intelligence.
What is strategic threat intelligence?
Strategic threat intelligence is developed for executive-level and / or board review. It includes non-technical intelligence reports that talk about a cyberattack's trends, risks and consequences so that the reader understands the impact on business decisions. The approach is typically generated on demand, and the information can take the form of a report, briefing, white paper, policy document or industry publication.
What is tactical threat intelligence?
Security defenders and decision-makers use tactical threat data to help them understand the latest attack vectors and techniques. By continuously understanding the latest attack approach and methods, an organization can develop better defense strategies and allocate security resources.
What is operational threat intelligence?
Operational intelligence provides specific information to help incident response teams stop an attack by better understanding the nature of the attack, the attack method, and its timing. A modern cybersecurity solution that uses ML is the best method for developing operational threat intelligence.
Acronis provides their customers with ongoing cyberthreat intelligence
Acronis Cyber Protect Cloud, part of the Acronis Cyber Cloud platform for service providers, and Acronis Cyber Protect for on-premises systems are industry-first solutions that integrate backup and cybersecurity capabilities in one solution to protect all data, applications and systems. Cyber protection requires researching and threat monitoring and abiding by the Five Vectors of Cyber Protection ― safety, accessibility, privacy, authenticity and security (SAPAS).
To support its approach, Acronis established a global network of Cyber Protection Operation Centers (CPOC) to monitor and research cyber threats 24/7. This global network constantly monitors Acronis’ partners, customers, and a battery of outside sources to detect and analyze the broad universe of cyberattacks. This monitoring enables Acronis engineers to research modern threats to help build easy, efficient and secure cyber protection solutions. In addition, CPOC research is also used to create threat alerts and smart protection plans to keep Acronis Cyber Protect users protected from the latest threats.
Acronis partners and customers can access these real-time threat alerts for the latest on malware, vulnerabilities, natural disasters and other global events that may affect their data protection. As a user, this enables your organization to continually get updates to the cybersecurity landscape without the need to monitor multiple different sources yourself constantly. In addition, you can automatically adjust protection plans based on these security alerts to ensure proactive protection against emerging threats.
If your organization is a small-to-medium-sized business, you may not have the security experts and budget to develop and monitor cyberthreat intelligence and stop modern-day attacks. This is why Acronis developed Acronis Cyber Protect Cloud for service providers. It enables the managed service provider (MSP) you work with to protect all of your workloads from advanced cyberattacks proactively. In addition to protecting critical business data, the solution can make compliance for, let's say, the General Data Protection Regulation (GDPR) easier.
With Acronis Cyber Protect, your organization has real-time protection with AI-based static and behavioral heuristic antivirus, anti-malware, anti-ransomware, and anti-cryptojacking technologies.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 50+ countries. Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.



