You are on United States website. Change region to view location-specific content:
Global
English
Select another region
Choose region and language
- Americas
- Asia-Pacific
- Europe, Middle East and Africa
- Worldwide


We all have valuable personal data on various devices, such as family photos, important documents and cherished memories. Yet not all of us can confidently say that their data is protected with a secure backup.
Data loss happens unexpectedly for various reasons, including hardware failure, accidental deletion, malware attacks or even natural disasters. Cloud services for file sharing are unreliable ― deleted or corrupted files can also disappear from the backup cloud. Only a reliable backup tool provides peace of mind.
Most backup tools fail users because they are too complicated or require sophisticated configuration. We designed our tool for busy people who only want reliable personal backups.
See what the community on Reddit is saying about us.
“Acronis True Image and you're safe anytime. I have a backup of my System drive in it's “best state”. If things ever go south, I restore it to it's previous best state.”
“Acronis True Image is also a good backup utility that can either run in Windows, or make a Linux-based USB stick backup that can boot to a slim Linux, and make a backup outside of Windows.”
“Acronis has always been my go to software for any backups. They always have a way to deal with any complicated technical details associated with backups.”
“I use Acronis. And #1 seems to be one of their approaches. Nothing can alter a backup. You must give consent. I like this approach.”
Please wait, this may take
a few seconds...
“The backups I make with Acronis True Image are part of my life. They make it possible for me to access my work and be able to get back to it.”
William Goldstein
Grammy-nominated composer, pianist and recording artist
“I was hit by a ransomware attack and a gentleman told me on the phone that I should pay a certain amount of money to get my data back. But in the back of my head, I knew that I had the ace card as I had Acronis True Image.”
Eli Yablonovitch
Professor of Electrical Engineering and Computer Sciences at UC Berkeley
Acronis solutions are trusted by thousands worldwide
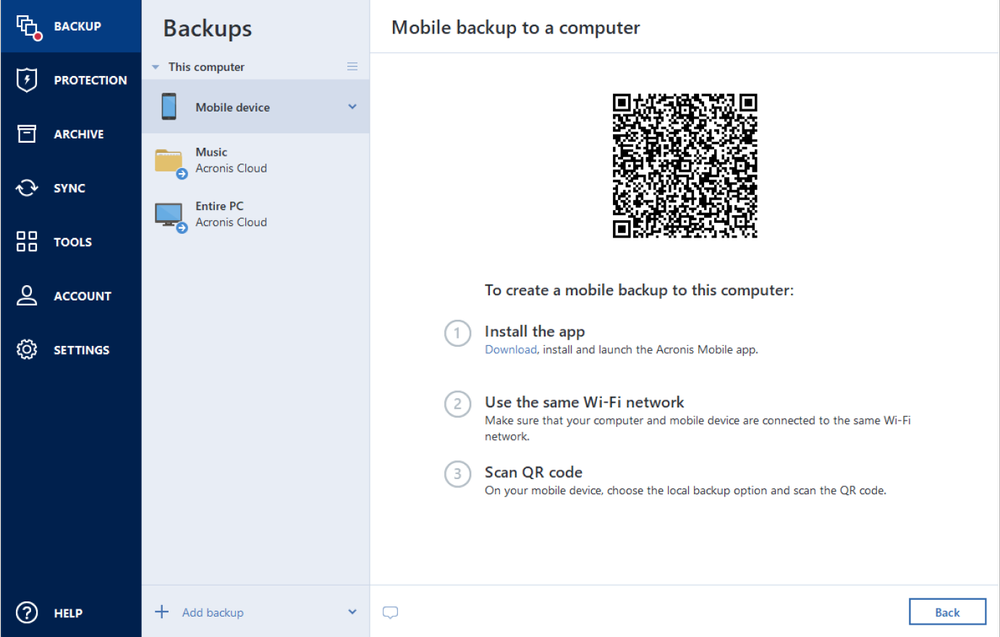
Never worry about losing your photos, videos, contacts or important files again. With the Acronis Mobile app, you can easily back up everything that matters on your phone and keep it safe in the cloud. Access your files anytime, anywhere from the Acronis Cloud, whether you're switching devices or just want peace of mind. It’s fast and always ready to protect your digital life.

Looking for help?
Backup software creates reserve copies of your data. In case of a data loss event, you can use these copies to recover the original data. Backups are useful for two primary purposes:
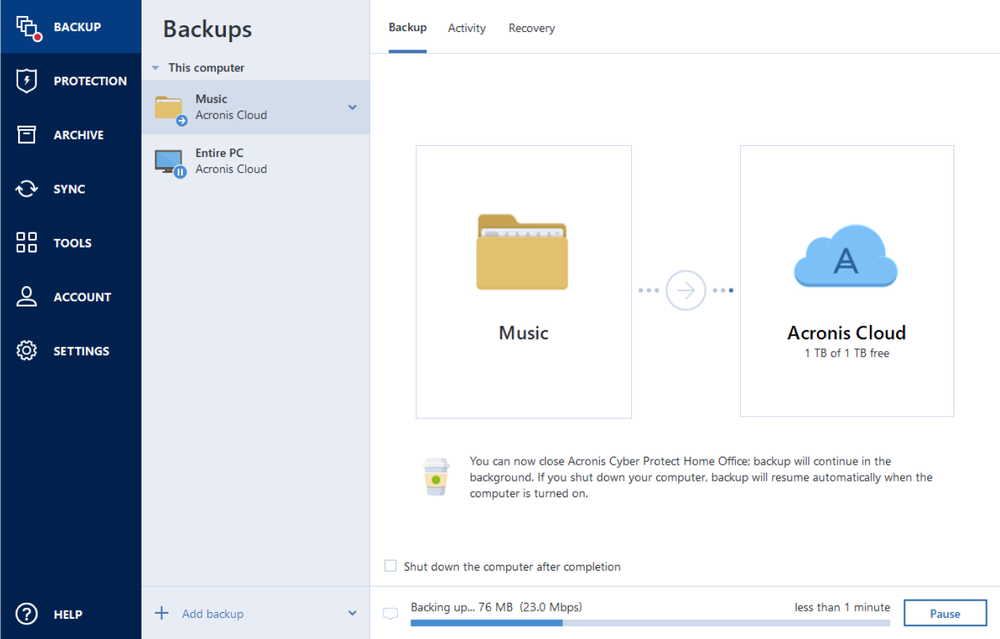
Back up all your data after every significant event in your system. For example, after you bought a new computer, reinstalled the operating system or installed an important system update.
You can also schedule backups to run automatically and on a regular basis. In this case, you will always have the latest version of your data for recovery.
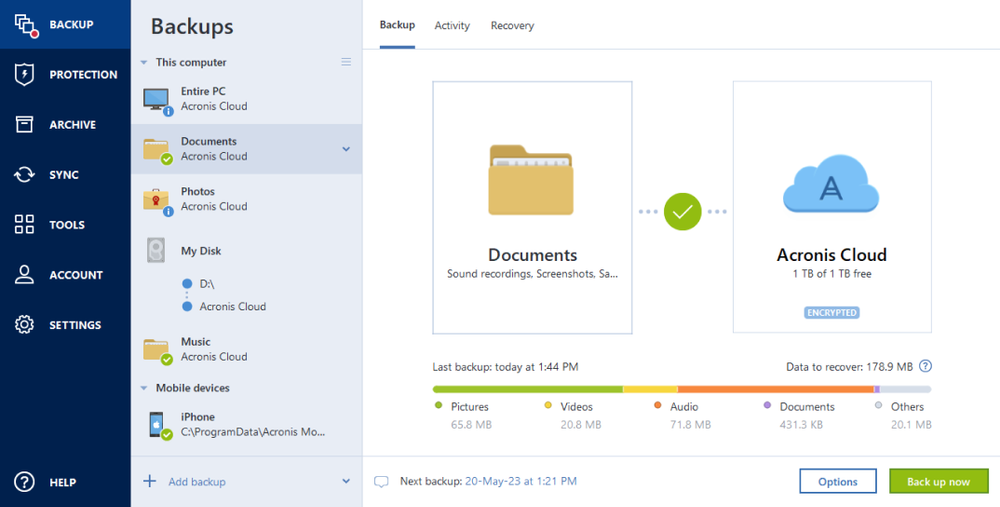
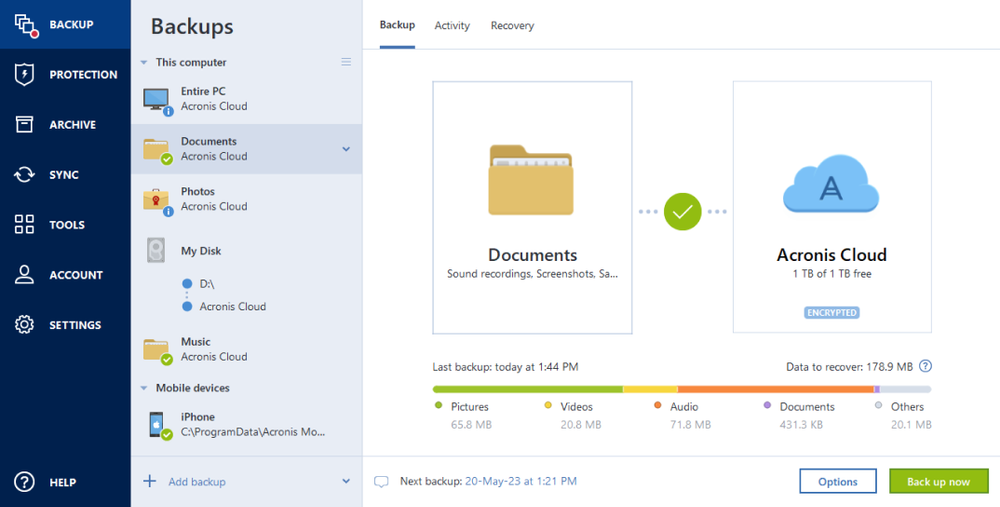
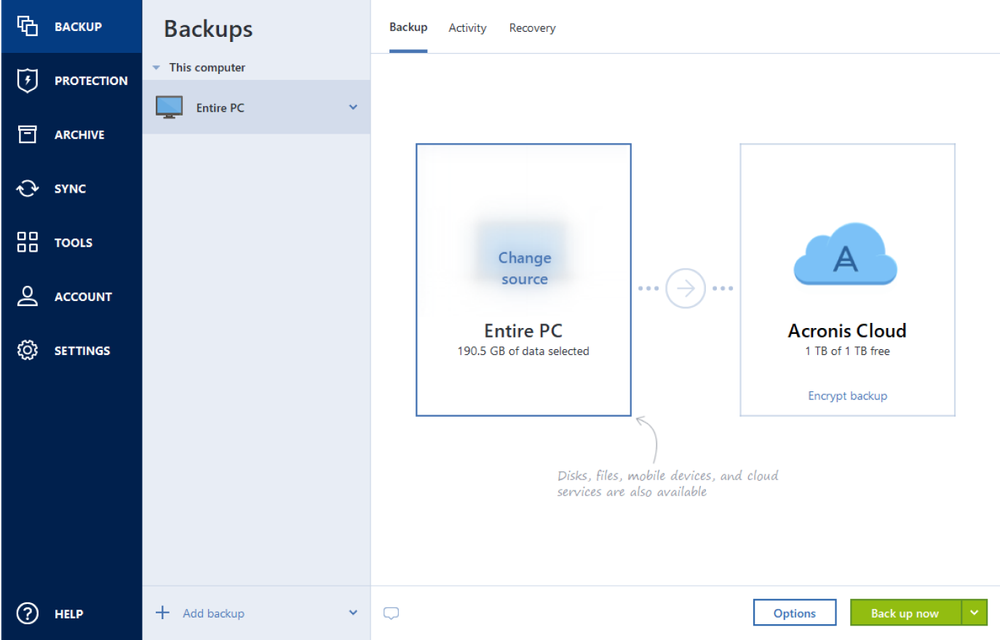
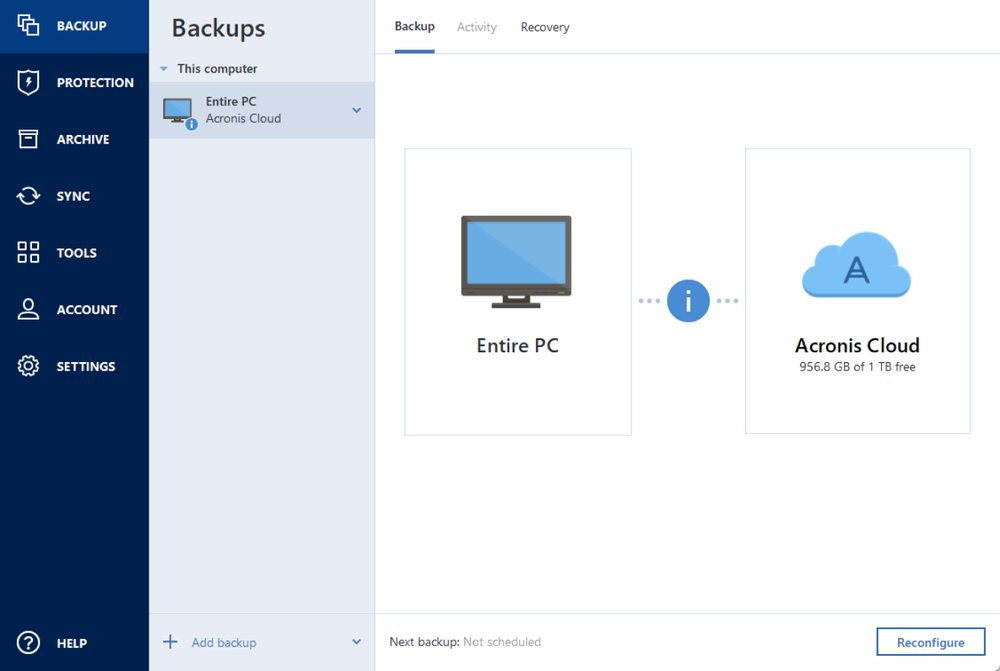
With Acronis True Image, you have the flexibility to store your backed-up files in various locations, depending on your needs:
You can choose the storage location that best suits your needs during the backup setup process. Acronis True Image ensures that your data is securely stored, no matter which option you choose.
Yes, you can run manual and scheduled or automated backups with Acronis backup software. See here how to perform this for Windows and for Mac operating systems.
Yes. You can back up data on all computers, smartphones and tablets registered for the same account. For more information on backing up multiple devices, see the procedures for Windows and for Mac.
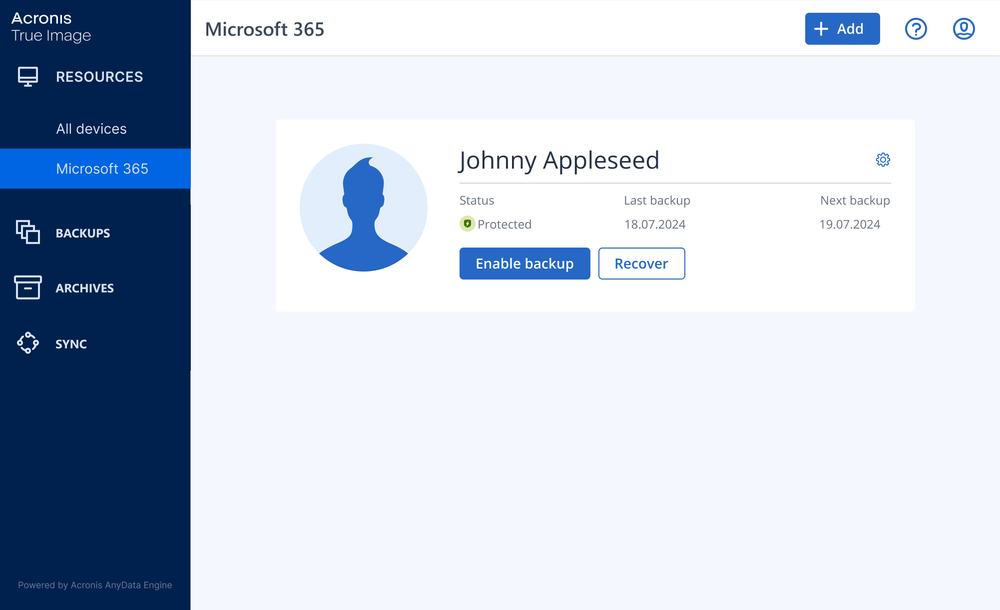
Yes, you can. An online dashboard enables you to track and control the protection status and backups of all computers, smartphones and tablets registered for the same account. For more information, see these procedures for Windows and for Mac.
Acronis True Image provides the following types of protection:
Computer backup software like Acronis True Image works by creating copies of your personal files, applications and system settings, which are then stored securely in a designated location. Here’s how it typically works:
By using Acronis True Image, you can safeguard your data against loss, hardware failure and other risks, giving you peace of mind knowing your information is securely backed up.
When it comes to protecting your valuable data at home, Acronis True Image stands out as one of the best home backup software solutions available. Here’s why:
For its powerful features, ease of use and trusted reliability, Acronis True Image is widely regarded as one of the best home backup software solutions available, offering peace of mind that your data is securely backed up and easily recoverable.
Sorry, your browser is not supported.
It seems that our new website is incompatible with your current browser's version. Don’t worry, this is easily fixed! To view our complete website, simply update your browser now or continue anyway.